Get the free Information Security in Big Data using Encryption and Decryption
Show details
International Research Journal of Computer Science (IR JCS) Issue 5, Volume 2 (May 2015) ISSN: 23939842 www.irjcs.com Information Security in Big Data using Encryption and Decryption SHAMAN PG Student
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign
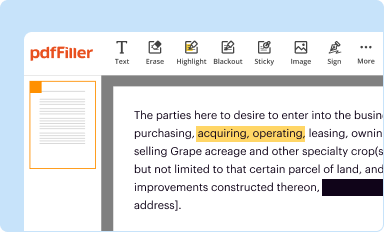
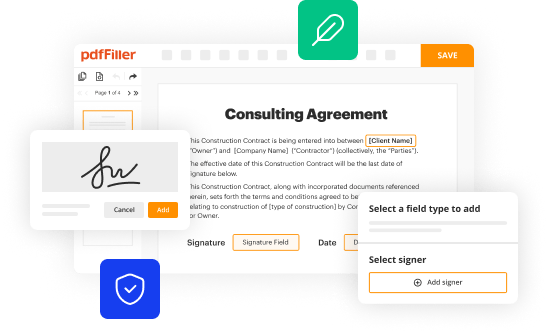
Edit your information security in big form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
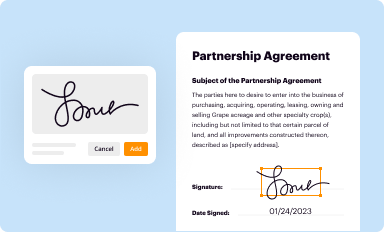
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
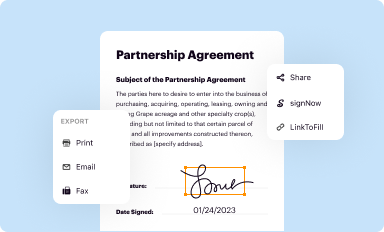
Share your form instantly
Email, fax, or share your information security in big form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit information security in big online
Here are the steps you need to follow to get started with our professional PDF editor:
1
Log in. Click Start Free Trial and create a profile if necessary.
2
Upload a file. Select Add New on your Dashboard and upload a file from your device or import it from the cloud, online, or internal mail. Then click Edit.
3
Edit information security in big. Add and change text, add new objects, move pages, add watermarks and page numbers, and more. Then click Done when you're done editing and go to the Documents tab to merge or split the file. If you want to lock or unlock the file, click the lock or unlock button.
4
Save your file. Choose it from the list of records. Then, shift the pointer to the right toolbar and select one of the several exporting methods: save it in multiple formats, download it as a PDF, email it, or save it to the cloud.
pdfFiller makes dealing with documents a breeze. Create an account to find out!
How to fill out information security in big
How to fill out information security in big:
01
Assess the current information security measures: Begin by evaluating the existing security protocols, systems, and processes in place within your organization. This includes identifying any vulnerabilities, potential threats, and areas of improvement.
02
Implement a comprehensive security framework: Develop and implement a robust security framework that encompasses all aspects of information security. This should include policies, procedures, guidelines, and best practices that address areas such as access control, data protection, incident response, and security awareness training.
03
Develop and enforce strong access controls: Establish stringent access controls to ensure that only authorized individuals have access to sensitive data and systems. This includes implementing strong authentication mechanisms, role-based access controls, and regular access reviews.
04
Protect data with encryption and data loss prevention mechanisms: Implement encryption techniques to protect sensitive data both at rest and in transit. Additionally, deploy data loss prevention mechanisms to monitor and control data leakages, unauthorized access, and misuse of confidential information.
05
Implement regular vulnerability assessments and penetration testing: Conduct regular vulnerability assessments and penetration tests to identify any weaknesses or vulnerabilities in your systems. This will help you proactively address potential security breaches and fortify your information security defenses.
06
Establish incident response and disaster recovery plans: Develop and document a comprehensive incident response plan that outlines the necessary steps to be taken in the event of a security incident. Additionally, ensure that robust disaster recovery plans are in place to facilitate the timely recovery of critical systems and data in the aftermath of an incident.
Who needs information security in big:
01
Organizations of all sizes: Information security is crucial for organizations of all sizes, whether they are small startups or large multinational corporations. Regardless of the industry, every organization faces potential threats and risks to their information security.
02
Government entities: Government agencies and departments deal with sensitive and confidential data on a regular basis. Therefore, information security is vital to safeguarding national security, citizen information, and critical infrastructure.
03
Healthcare institutions: With the proliferation of digital health records and telemedicine, healthcare institutions need robust information security measures to protect sensitive patient data and ensure patient privacy.
04
Financial institutions: Banks, insurance companies, and other financial institutions handle large volumes of sensitive financial data. Information security is crucial to protect customer accounts, prevent fraudulent activities, and maintain the trust of clients.
05
E-commerce companies: Online businesses that handle customer transactions and personal information need strong information security measures to safeguard customer data, prevent unauthorized access, and maintain the integrity of online transactions.
Fill form : Try Risk Free
For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I modify information security in big without leaving Google Drive?
People who need to keep track of documents and fill out forms quickly can connect PDF Filler to their Google Docs account. This means that they can make, edit, and sign documents right from their Google Drive. Make your information security in big into a fillable form that you can manage and sign from any internet-connected device with this add-on.
Can I sign the information security in big electronically in Chrome?
Yes. With pdfFiller for Chrome, you can eSign documents and utilize the PDF editor all in one spot. Create a legally enforceable eSignature by sketching, typing, or uploading a handwritten signature image. You may eSign your information security in big in seconds.
How do I fill out information security in big on an Android device?
Complete your information security in big and other papers on your Android device by using the pdfFiller mobile app. The program includes all of the necessary document management tools, such as editing content, eSigning, annotating, sharing files, and so on. You will be able to view your papers at any time as long as you have an internet connection.
Fill out your information security in big online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Not the form you were looking for?
Keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.