Get the free Checklist of Technology, Tools and Tactics for Effective Web Protection
Show details
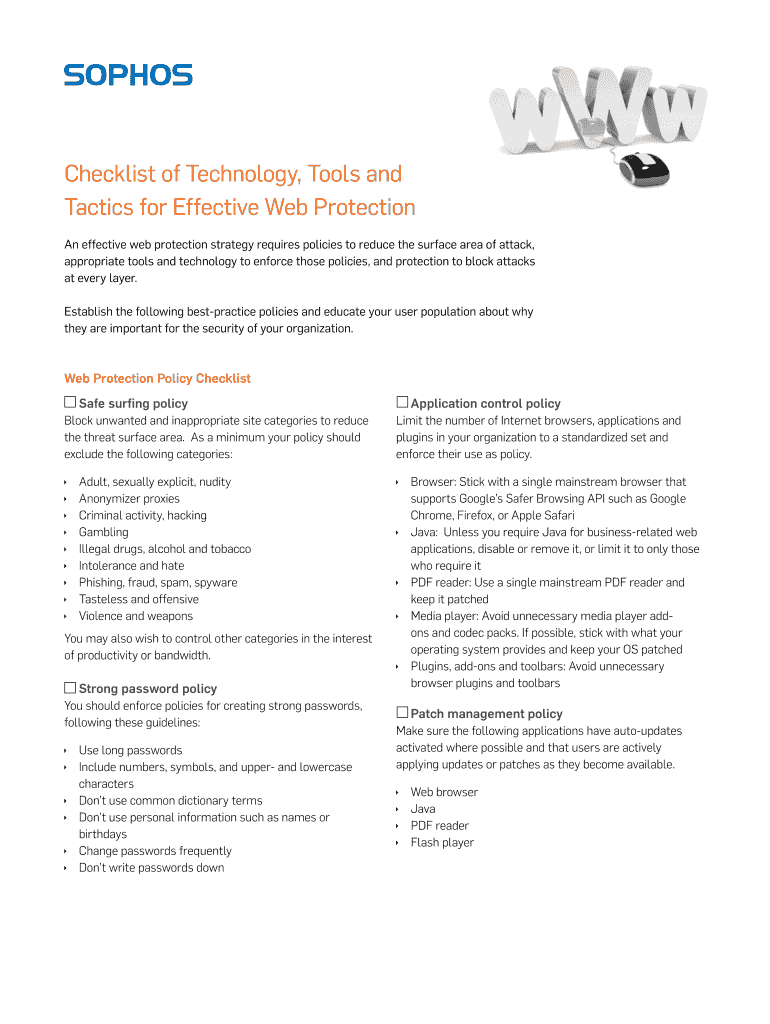
This document outlines best-practice policies, technology, and tools for establishing effective web protection strategies to minimize security risks in organizations.
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign checklist of technology tools

Edit your checklist of technology tools form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your checklist of technology tools form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit checklist of technology tools online
Here are the steps you need to follow to get started with our professional PDF editor:
1
Register the account. Begin by clicking Start Free Trial and create a profile if you are a new user.
2
Upload a document. Select Add New on your Dashboard and transfer a file into the system in one of the following ways: by uploading it from your device or importing from the cloud, web, or internal mail. Then, click Start editing.
3
Edit checklist of technology tools. Add and replace text, insert new objects, rearrange pages, add watermarks and page numbers, and more. Click Done when you are finished editing and go to the Documents tab to merge, split, lock or unlock the file.
4
Save your file. Select it from your list of records. Then, move your cursor to the right toolbar and choose one of the exporting options. You can save it in multiple formats, download it as a PDF, send it by email, or store it in the cloud, among other things.
pdfFiller makes dealing with documents a breeze. Create an account to find out!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out checklist of technology tools

How to fill out Checklist of Technology, Tools and Tactics for Effective Web Protection
01
Identify the specific web assets that need protection, such as websites, applications, and databases.
02
List the potential threats and vulnerabilities that could affect these assets.
03
Research and select appropriate technologies, tools, and tactics that can be deployed for each identified threat.
04
Create a checklist format to categorize these tools and tactics according to their purpose, such as prevention, detection, and response.
05
Regularly update the checklist to include new technologies and tools as they become available.
06
Assign responsibilities to relevant team members for implementing the selected technologies and tactics.
07
Schedule regular reviews of the checklist to ensure it remains effective and reflects current security needs.
Who needs Checklist of Technology, Tools and Tactics for Effective Web Protection?
01
Webmasters
02
IT security professionals
03
Business owners with an online presence
04
Organizations that rely on e-commerce and online transactions
05
Web developers and software engineers
06
Compliance officers concerned with data protection regulations
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is Checklist of Technology, Tools and Tactics for Effective Web Protection?
The Checklist of Technology, Tools and Tactics for Effective Web Protection is a comprehensive framework that outlines the essential technologies, tools, and strategies organizations should implement to safeguard their web assets from threats.
Who is required to file Checklist of Technology, Tools and Tactics for Effective Web Protection?
Organizations operating online, especially those handling sensitive information, are typically required to file this checklist to ensure they are adhering to best practices in web security.
How to fill out Checklist of Technology, Tools and Tactics for Effective Web Protection?
To fill out the checklist, organizations should review each item in the framework, assess their current security measures, document their technology stack, and identify any gaps in their protection strategies.
What is the purpose of Checklist of Technology, Tools and Tactics for Effective Web Protection?
The purpose of the checklist is to provide a structured approach for organizations to evaluate and enhance their web protection strategies, ensuring robust security against cyber threats.
What information must be reported on Checklist of Technology, Tools and Tactics for Effective Web Protection?
The checklist requires reporting on the types of technology and tools in use, current security measures, incidents of security breaches, compliance with relevant regulations, and areas identified for improvement.
Fill out your checklist of technology tools online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Checklist Of Technology Tools is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.