
Get the free Chronology of Data Breaches - health and fitness - doczz - oag ca
Show details
NOTICE ADMINISTRATOR
PO BOX 2824
ARNAULT, MN 550218629IMPORTANT NOTICE
PLEASE READ THIS LETTER IN ITS ENTIRETY×0123456789* SEQNAME1
NAME2
ADDRESS1
ADDRESS2
CITY STATE ZIP
COUNTRYSIDE
Dear Customer
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign chronology of data breaches
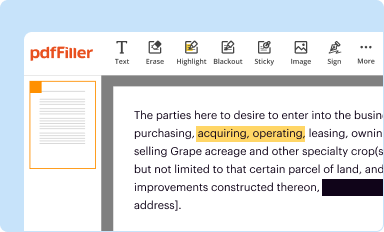
Edit your chronology of data breaches form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
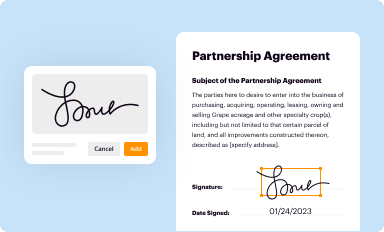
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
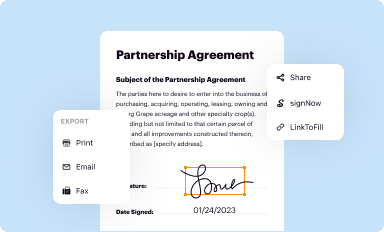
Share your form instantly
Email, fax, or share your chronology of data breaches form via URL. You can also download, print, or export forms to your preferred cloud storage service.
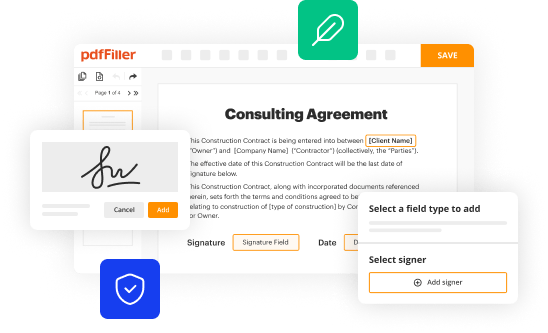
How to edit chronology of data breaches online
To use the professional PDF editor, follow these steps below:
1
Check your account. If you don't have a profile yet, click Start Free Trial and sign up for one.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit chronology of data breaches. Rearrange and rotate pages, add new and changed texts, add new objects, and use other useful tools. When you're done, click Done. You can use the Documents tab to merge, split, lock, or unlock your files.
4
Get your file. When you find your file in the docs list, click on its name and choose how you want to save it. To get the PDF, you can save it, send an email with it, or move it to the cloud.
pdfFiller makes dealing with documents a breeze. Create an account to find out!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out chronology of data breaches
How to fill out chronology of data breaches
01
To fill out a chronology of data breaches, follow these steps:
02
Gather all the relevant information about the data breaches. This may include the date of the breach, the type of data compromised, the affected individuals or organizations, and any known details about the cause or impact of the breach.
03
Organize the information in a chronological order, starting with the oldest breaches and moving towards the most recent ones.
04
Include as much detail as possible for each breach, such as the method of attack, the security measures in place at the time, and any actions taken in response to the breach.
05
Make sure to cite your sources and provide references for each piece of information. This is important for maintaining credibility and allowing others to verify the accuracy of the chronology.
06
Update the chronology regularly as new breaches occur or additional information becomes available.
07
Consider categorizing the breaches based on common characteristics, such as the industry or sector affected, the type of data compromised, or the nature of the attack. This can help identify patterns or trends in data breaches over time.
08
Share the chronology with relevant stakeholders, such as cybersecurity professionals, government agencies, or organizations involved in data breach prevention and response.
09
Use the chronology as a reference and learning tool to improve data security practices and enhance incident response procedures in the future.
Who needs chronology of data breaches?
01
A chronology of data breaches may be needed by various individuals or organizations, including:
02
- Cybersecurity professionals who want to analyze trends and patterns in data breaches to develop more effective prevention and mitigation strategies.
03
- Government agencies responsible for regulating data privacy and security, who need to stay informed about the frequency and severity of data breaches to develop or enforce relevant policies.
04
- Organizations that have experienced a data breach and want to learn from past incidents to prevent similar breaches in the future.
05
- Researchers or analysts studying the field of data breaches and looking for comprehensive data sets to support their work.
06
- Media outlets reporting on cybersecurity issues and wanting to provide accurate and up-to-date information to their audience.
07
- General public interested in staying informed about data breaches and understanding the evolving landscape of data security threats.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I execute chronology of data breaches online?
pdfFiller makes it easy to finish and sign chronology of data breaches online. It lets you make changes to original PDF content, highlight, black out, erase, and write text anywhere on a page, legally eSign your form, and more, all from one place. Create a free account and use the web to keep track of professional documents.
Can I edit chronology of data breaches on an iOS device?
Use the pdfFiller app for iOS to make, edit, and share chronology of data breaches from your phone. Apple's store will have it up and running in no time. It's possible to get a free trial and choose a subscription plan that fits your needs.
Can I edit chronology of data breaches on an Android device?
You can make any changes to PDF files, like chronology of data breaches, with the help of the pdfFiller Android app. Edit, sign, and send documents right from your phone or tablet. You can use the app to make document management easier wherever you are.
What is chronology of data breaches?
Chronology of data breaches is a timeline or sequence of events detailing when data breaches occurred.
Who is required to file chronology of data breaches?
Entities or organizations that experience a data breach are required to file chronology of data breaches.
How to fill out chronology of data breaches?
Fill out the chronology of data breaches by providing detailed information about each data breach incident, including dates, types of data compromised, and remediation actions taken.
What is the purpose of chronology of data breaches?
The purpose of chronology of data breaches is to document and track data breach incidents for regulatory compliance and internal auditing purposes.
What information must be reported on chronology of data breaches?
Information reported on chronology of data breaches may include dates of data breaches, types of data compromised, number of affected individuals, and remediation actions taken.
Fill out your chronology of data breaches online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Chronology Of Data Breaches is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.




















