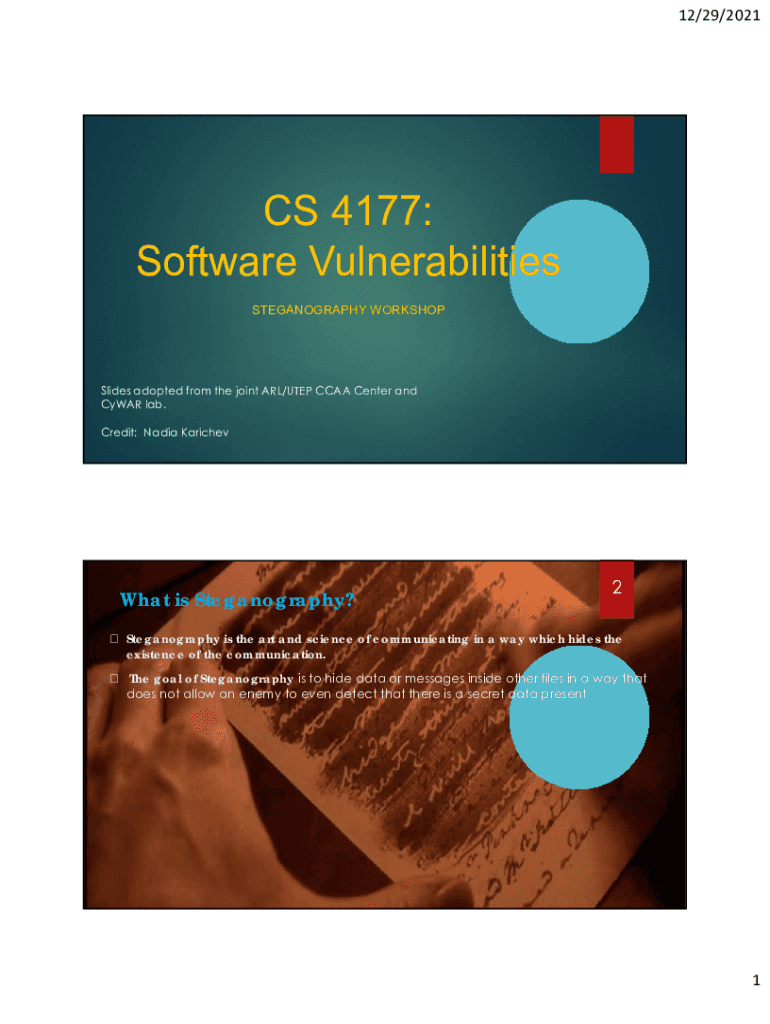
Get the free CS 4177: Software Vulnerabilities - UTEP Computer Science
Show details
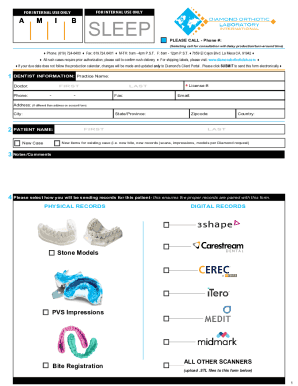
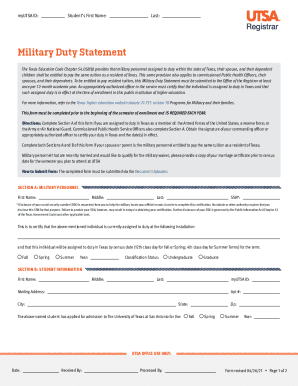
12/29/2021CS 4177: Software Vulnerabilities STEGANOGRAPHY WORKSHOPSlides adopted from the joint ARL/UTEP NCAA Center and Year lab. Credit: Nadia KarichevWhat is Steganography?2Steganography is the
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign cs 4177 software vulnerabilities

Edit your cs 4177 software vulnerabilities form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your cs 4177 software vulnerabilities form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit cs 4177 software vulnerabilities online
Here are the steps you need to follow to get started with our professional PDF editor:
1
Register the account. Begin by clicking Start Free Trial and create a profile if you are a new user.
2
Simply add a document. Select Add New from your Dashboard and import a file into the system by uploading it from your device or importing it via the cloud, online, or internal mail. Then click Begin editing.
3
Edit cs 4177 software vulnerabilities. Add and change text, add new objects, move pages, add watermarks and page numbers, and more. Then click Done when you're done editing and go to the Documents tab to merge or split the file. If you want to lock or unlock the file, click the lock or unlock button.
4
Get your file. Select the name of your file in the docs list and choose your preferred exporting method. You can download it as a PDF, save it in another format, send it by email, or transfer it to the cloud.
With pdfFiller, it's always easy to work with documents. Check it out!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out cs 4177 software vulnerabilities

How to fill out cs 4177 software vulnerabilities
01
To fill out CS 4177 software vulnerabilities, follow these steps:
02
Start by documenting all known software vulnerabilities in your system.
03
Identify the severity level and impact of each vulnerability.
04
Determine the root cause of the vulnerabilities and investigate any potential exploits.
05
Prioritize the vulnerabilities based on their level of risk and potential impact on your system.
06
Develop a plan to address each vulnerability, including any necessary code fixes or security patches.
07
Implement the necessary changes to mitigate the vulnerabilities.
08
Test the system thoroughly to ensure the fixes have been successfully applied.
09
Continuously monitor for new vulnerabilities and apply updates as needed.
10
Regularly review and update your software vulnerability documentation as new vulnerabilities are discovered or addressed.
11
Communicate the status of software vulnerabilities and the steps taken to mitigate them to relevant stakeholders.
Who needs cs 4177 software vulnerabilities?
01
Anyone involved in software development or system administration who wants to ensure the security of their software systems can benefit from CS 4177 software vulnerabilities.
02
This includes software developers, security analysts, system administrators, IT managers, and anyone responsible for maintaining the integrity and security of software applications.
03
Additionally, organizations that handle sensitive data or have compliance requirements may need to address software vulnerabilities as part of their security practices.
04
By identifying and addressing software vulnerabilities, organizations can reduce the risk of unauthorized access, data breaches, or other security incidents that could result in financial and reputational damage.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
Can I create an electronic signature for signing my cs 4177 software vulnerabilities in Gmail?
Use pdfFiller's Gmail add-on to upload, type, or draw a signature. Your cs 4177 software vulnerabilities and other papers may be signed using pdfFiller. Register for a free account to preserve signed papers and signatures.
How do I fill out the cs 4177 software vulnerabilities form on my smartphone?
The pdfFiller mobile app makes it simple to design and fill out legal paperwork. Complete and sign cs 4177 software vulnerabilities and other papers using the app. Visit pdfFiller's website to learn more about the PDF editor's features.
Can I edit cs 4177 software vulnerabilities on an Android device?
Yes, you can. With the pdfFiller mobile app for Android, you can edit, sign, and share cs 4177 software vulnerabilities on your mobile device from any location; only an internet connection is needed. Get the app and start to streamline your document workflow from anywhere.
What is cs 4177 software vulnerabilities?
CS 4177 software vulnerabilities refer to the identification and reporting of potential weaknesses or security flaws in software programs.
Who is required to file cs 4177 software vulnerabilities?
Any organization or individual responsible for the development or maintenance of software programs is required to file CS 4177 software vulnerabilities.
How to fill out cs 4177 software vulnerabilities?
CS 4177 software vulnerabilities can be filled out by documenting the identified vulnerabilities, their potential impact, and proposed remediation strategies.
What is the purpose of cs 4177 software vulnerabilities?
The purpose of CS 4177 software vulnerabilities is to improve the overall security of software programs by identifying and addressing potential weaknesses.
What information must be reported on cs 4177 software vulnerabilities?
The report on CS 4177 software vulnerabilities must include details on the identified vulnerabilities, their severity level, potential impact, and proposed remediation measures.
Fill out your cs 4177 software vulnerabilities online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Cs 4177 Software Vulnerabilities is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.