Last updated on Mar 26, 2026

Get the free System Authorization Access Request Form
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is system authorization access request
The System Authorization Access Request Form is a government document used by individuals to request access to Department of Defense (DoD) systems and information.
pdfFiller scores top ratings on review platforms




Who needs system authorization access request?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to system authorization access request
What is the System Authorization Access Request Form?
The System Authorization Access Request Form (SAAR) is a critical document used within the Department of Defense (DoD) to facilitate access to its systems and sensitive information. This form serves as a formal request for individuals seeking permission to access specific DoD resources. It is vital for ensuring that individuals meet the necessary security requirements before gaining access to classified information.
The SAAR form is intrinsically linked to DD Form 2875, which provides the groundwork for authorization procedures. By understanding the nuances of the System Authorization Access Request Form, individuals can navigate the authorization process more effectively.
Purpose and Benefits of the System Authorization Access Request Form
The primary function of the System Authorization Access Request Form is to justify access to DoD systems. By validating the requestor's trustworthiness, the form helps streamline the process of granting access while enhancing overall security measures. Furthermore, including organizational and personal details serves an important role in auditing and ensuring compliance with security protocols.
Benefits of utilizing this form include increased efficiency in accessing DoD systems and a reinforced security framework, which collectively protect sensitive information from unauthorized access.
Roles Involved in the System Authorization Access Request Form
Several key roles are critical to the submission and approval process of the System Authorization Access Request Form:
-
Requestor: The individual seeking access.
-
Supervisor/UAM: Responsible for reviewing and endorsing the request.
-
Security Manager: Ensures adherence to security protocols.
-
Information Owner/OPR: Validates the need for access.
-
IAO or Appointee: Finalizes the approval process with signature.
Each role has specific signature requirements and responsibilities, emphasizing the need for collaboration to ensure an effective and compliant processing of requests.
Eligibility Criteria for the System Authorization Access Request Form
Eligibility to submit the System Authorization Access Request Form is primarily restricted to individuals affiliated with organizations within the DoD. This requirement ensures that only authorized personnel can request system access.
Specific criteria vary based on the role one plays within the approval process, which further underscores the importance of the organizational connection for the intended access.
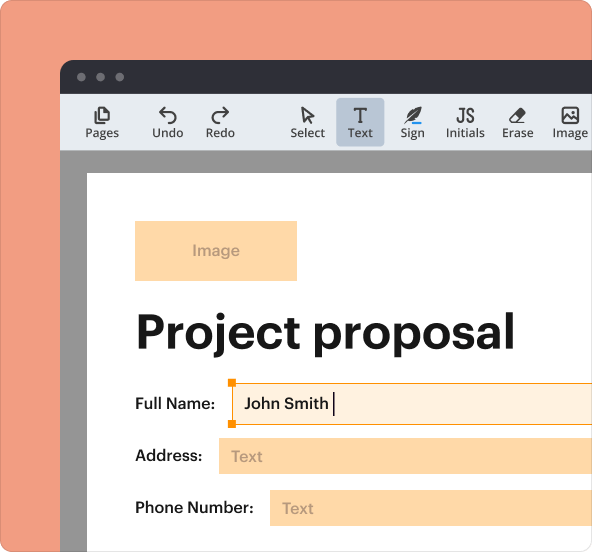
How to Fill Out the System Authorization Access Request Form Online
Filling out the System Authorization Access Request Form online is a straightforward process. Here is a step-by-step guide to assist you:
-
Access the online form via pdfFiller.
-
Carefully read through the instructions provided.
-
Fill in your personal and organizational details accurately.
-
Provide justification for access based on your role and responsibilities.
-
Review for any common errors before submission.
Completing these steps diligently will enhance the accuracy of your submission, facilitating a smoother approval process.
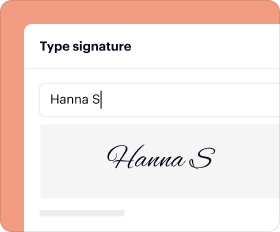
How to Sign the System Authorization Access Request Form
The signing process for the System Authorization Access Request Form necessitates understanding the differences between digital signatures and wet signatures. Each role involved in the submission process has specific signature requirements that must be adhered to for the form to be considered valid.
Signatures play a crucial role in the validation of the document, enhancing its credibility during the review and approval stages.
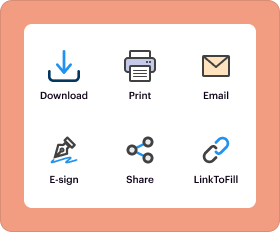
Submission Methods for the System Authorization Access Request Form
Submitting the filled-out System Authorization Access Request Form can be accomplished through various methods. Options include both electronic submission and traditional paper-based approaches. It is important to follow the designated pathways within the DoD to ensure your request is received promptly.
Additionally, understanding the timing and deadlines for submissions can prevent delays in processing, making this step essential for compliance.
Security and Compliance for the System Authorization Access Request Form
Security is paramount when handling the System Authorization Access Request Form. The document is subject to multiple security measures, including encryption, to protect sensitive data. Compliance with regulations such as HIPAA and GDPR is also critical to ensure that individual information is handled with the utmost care.
Data protection is essential within the military context, reinforcing the need for robust security practices when managing access requests.
Sample of a Completed System Authorization Access Request Form
For enhanced understanding, a visual reference of a completed System Authorization Access Request Form is beneficial. Key sections of the form include:
-
Name (Last, First, Middle Initial)
-
User Signature or UAM Signature for Deactivation
-
Supervisor/UAM Signature
These sections represent critical information that must be accurately filled out, and recognizing common pitfalls can aid in reducing errors when completing the form.
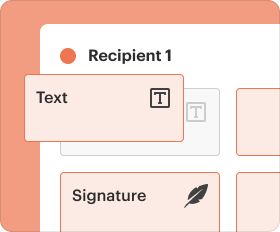
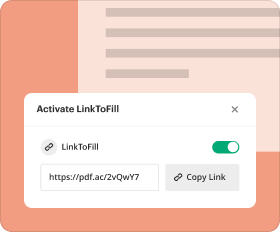
Using pdfFiller to Complete Your System Authorization Access Request Form
Utilizing pdfFiller to complete your System Authorization Access Request Form offers numerous advantages. The platform allows for easy editing, eSigning, and management of documents directly from any web browser, eliminating the need for downloads.
Moreover, the security features embedded within pdfFiller, such as 256-bit encryption, provide a reliable environment for handling sensitive documentation required in the request process. The combination of ease of use and robust security makes pdfFiller an optimal choice for your form-filling needs.
How to fill out the system authorization access request
-
1.Start by accessing pdfFiller and searching for 'System Authorization Access Request Form'. You can find it quickly by typing the form name into the search bar.
-
2.Once the form opens in pdfFiller, take a moment to familiarize yourself with its layout, including various fields, checkboxes, and signature areas.
-
3.Before you begin filling out the form, ensure that you have all necessary information gathered. This includes your personal details, justification for access, and relevant supervisory approvals.
-
4.Begin filling out the form by entering your last name, first name, and middle initial in the designated fields. Proceed to add your email address and contact number.
-
5.Complete all sections of the form, including specifying your role, and business justification for accessing the system. Utilize the provided space for detailed explanations.
-
6.Fill out the sections requiring signatures. Ensure that you include the names and signatures of your supervisor, security manager, information owner, and any appointed individuals designated by your organization.
-
7.After completing all fields, carefully review the form for accuracy. Verify that all sections have been filled correctly, and double-check signature areas to confirm all necessary signatures are present.
-
8.Once satisfied, click the save option to keep a record of your completed form. You can choose to save it as a PDF file directly on your device.
-
9.If you need to submit the form electronically, follow the instructions provided by your organization. Ensure you understand the submission method before proceeding.
-
10.Finally, download the filled form to your device or submit it directly via email or through the designated organizational platform, based on your procedures.
Who is eligible to fill out the System Authorization Access Request Form?
Any individual seeking access to Department of Defense systems can fill out the System Authorization Access Request Form, provided they obtain necessary approvals from their supervisor and security manager.
Is there a submission deadline for this form?
While there may not be a specific deadline for submitting the System Authorization Access Request Form itself, it's best practice to submit it as soon as you require access for timely processing.
How should I submit the completed form?
The completed System Authorization Access Request Form can typically be submitted electronically via email to your security office or approved submission channel, following your organization's procedures.
What documents do I need to provide with this form?
Generally, you will need to provide identification details, your justification for system access, and any necessary approvals from your supervisor and security manager to complete the form.
What are common mistakes to avoid when completing this form?
Common mistakes include omitting required signatures, leaving sections incomplete, and not providing sufficient justification for access. Double-check that all fields are filled and reviewed before submission.
How long does it take to process this request?
Processing times for the System Authorization Access Request Form can vary depending on the organization's workload. Generally, it can take anywhere from a few days to several weeks.
What if I need to make changes to my submitted form?
If you need to make changes after submission, contact your security office immediately. They can provide guidance on how to amend your request or resubmit an updated form.
Related Catalogs
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.