Last updated on Apr 8, 2015

Get the free Identity Theft Prevention Program
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is Identity Theft Program
The Identity Theft Prevention Program is a regulatory document used by utility companies to establish procedures for identifying and responding to potential identity theft risks associated with customer accounts.
pdfFiller scores top ratings on review platforms




Who needs Identity Theft Program?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to Identity Theft Program
What is the Identity Theft Prevention Program?
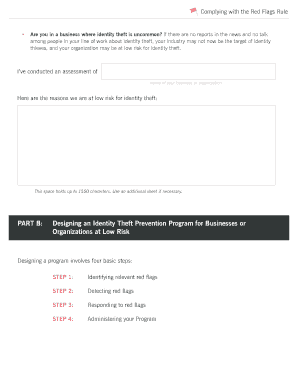
The Identity Theft Prevention Program is a crucial framework designed to protect consumers and utility companies against fraud. This program ensures compliance with the FTC's Red Flags Rule by establishing specific procedures to identify and serve notice of potential identity theft risks. The documentation outlines clear definitions, identifies red flags, and includes essential steps for response and mitigation.
Key elements of the program documentation typically include compliance requirements, identification of security vulnerabilities, and procedural protocols to address incidents of identity theft effectively.
Purpose and Benefits of the Identity Theft Prevention Program
Implementing an Identity Theft Prevention Program is vital due to the increasing risks associated with utility accounts. Utility companies face a heightened risk of compromised customer information, making such programs essential for fraud prevention.
By adopting this program, companies can strengthen customer account protection and enhance consumer trust while effectively mitigating identity theft risks. This proactive approach not only safeguards sensitive data but also fortifies the overall credibility of utility providers in the eyes of their customers.
Key Features of the Identity Theft Prevention Program
The program document consists of essential components that guide its users through compliance and security protocols. These include a detailed overview of red flags and definitions critical for identifying potential fraud.
-
Definitions and explanations of various identity theft indicators.
-
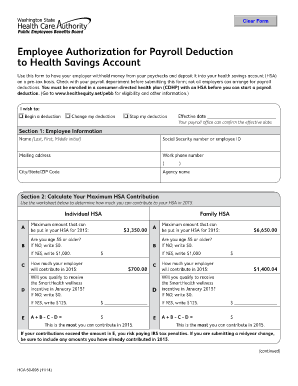
Fillable fields and checkboxes designed for user input.
-
Clear personal instructions to facilitate accurate completion.
-
Procedures aimed at detecting and responding to identity theft risks.
Who Needs the Identity Theft Prevention Program?
Utility companies are the primary stakeholders required to implement the Identity Theft Prevention Program. They play a significant role in protecting customer data and ensuring compliance with legal standards.
Potential clients, including individual consumers, must also be aware of the importance of this program, as it directly impacts their security against identity theft. Situations necessitating this program often arise from increased risk levels associated with customer data management.
How to Complete the Identity Theft Prevention Program Online
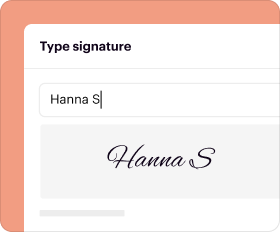
To fill out the form online using pdfFiller, follow these simple steps. First, access the online form through the designated platform. Familiarize yourself with the layout and navigation tools available.
-
Begin by entering the required information in the designated fillable fields.
-
Utilize checkboxes to ensure all necessary information is included.
-
Review the completed form to avoid errors, focusing on common pitfalls often encountered during the process.
Submission Methods and Delivery
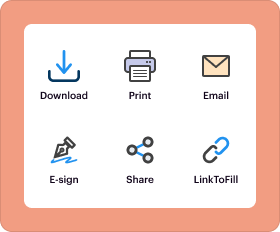
Once the Identity Theft Prevention Program has been completed, multiple submission methods are available to ensure ease of delivery. You can submit your documents online or opt for mailing them to the appropriate agency.
-
Instructions for tracking your submission to confirm it has been received.
-
Importance of retaining a copy of the submission for your records to safeguard personal compliance.
Post-Submission Process and Tracking
Following the submission of your program documentation, there are specific steps to confirm the receipt of your submission. Processing times may vary, so it's advisable to stay updated.
If additional information is required or amendments are necessary, knowing how to proceed is essential for compliance. Understanding common rejection reasons can also enhance the accuracy of future submissions.
Security and Compliance Considerations for the Identity Theft Prevention Program
Handling sensitive data under the Identity Theft Prevention Program demands stringent security measures. Effective practices include the use of encryption and adherence to compliance regulations such as HIPAA.
Data protection is not only a legal obligation but also a critical component in building trust with consumers. pdfFiller is committed to upholding this standard in document management, ensuring users can safeguard their information effectively.
Utilizing pdfFiller for Your Identity Theft Prevention Program
pdfFiller provides an efficient platform for managing your Identity Theft Prevention Program. Users can benefit from a suite of capabilities to create, edit, and securely submit their documents with ease.
This user-friendly tool enhances the entire document preparation process, making it simpler for utilities and consumers to meet their identity theft prevention needs while ensuring customer account protection is prioritized.
How to fill out the Identity Theft Program
-
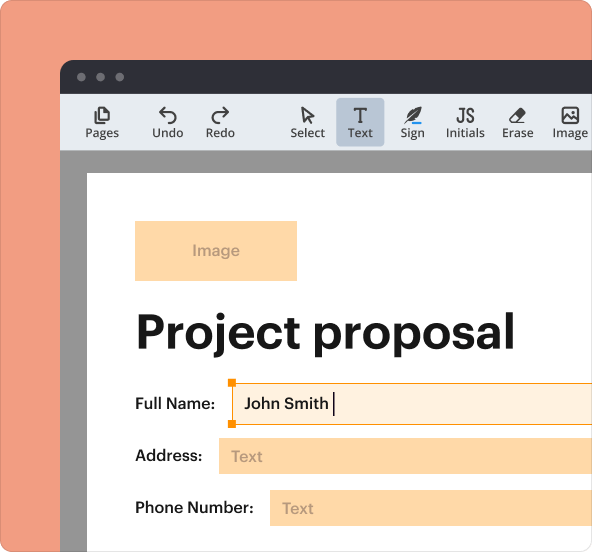
1.To access the Identity Theft Prevention Program form on pdfFiller, navigate to the site and enter the form’s title in the search bar.
-
2.Once you have located the form, click on it to open it in the pdfFiller interface.
-
3.Before you start filling out the form, gather all necessary information related to customer accounts, including any existing procedures and policies your utility company has in place.
-
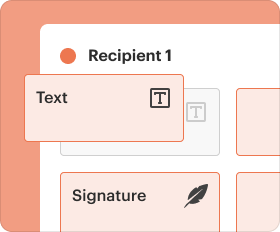
4.Use the toolbar on pdfFiller to navigate through the various sections of the form. Click on each fillable field to enter the required information.
-
5.Pay attention to the red flags and definitions provided in the document, ensuring your responses reflect the steps needed for identity theft detection and prevention.
-
6.After completing all sections, review each field to ensure accuracy and completeness. Use the preview function to see the form as it will appear once finalized.
-
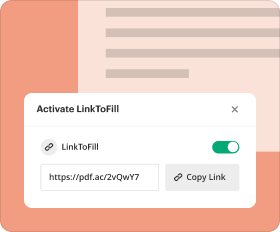
7.Once you are satisfied with the filled form, save your work. You can conveniently download it to your device or submit it electronically through the pdfFiller interface.
Who is eligible to use the Identity Theft Prevention Program?
The Identity Theft Prevention Program is designed for utility companies that need to comply with the Federal Trade Commission's Red Flags Rule. Any utility company managing customer accounts can utilize this program.
What are the key deadlines for completing this form?
The form must be completed and implemented as per the timelines set by the Federal Trade Commission's guidelines. Regular reviews should be conducted to ensure compliance with any updates in regulations.
How do I submit the Identity Theft Prevention Program?
After filling out the form on pdfFiller, you have the option to save it for your records, download it, or submit it directly to your regulatory body through the platform's submission options, depending on your specific requirements.
What supporting documents are required with this form?
While the form itself does not require additional documents, you should have your utility company’s policies and any relevant procedural documents handy to ensure comprehensive risk assessment and prevention strategies.
What common mistakes should I avoid when filling out the form?
Ensure that all fields are filled in completely. Common mistakes include leaving fields blank, failing to define relevant red flags, and not aligning procedures with practices outlined in the guidelines.
What is the typical processing time after submitting the form?
Processing times vary by state and regulatory body, but it is advisable to follow up after submission to confirm receipt and inquire about the status of your compliance review.
Can I update the Identity Theft Prevention Program after submission?
Yes, updates can be made to the program as needed, especially when new identity theft risks or regulations arise. Regular reviews and updates are recommended to maintain efficacy.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.