Last updated on Apr 3, 2026

Get the free US Army Information Security Inspection Checklist
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is us army information security
The US Army Information Security Inspection Checklist is a military document used by inspectors to evaluate compliance with information security protocols.
pdfFiller scores top ratings on review platforms




Who needs us army information security?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to us army information security
What is the US Army Information Security Inspection Checklist?
The US Army Information Security Inspection Checklist is designed to evaluate compliance with information security protocols within military units. This essential military information security form serves as a guide for assessing adherence to procedures established by AR 380-5.
The checklist features a structured layout that includes checkboxes, signature fields, and compliance status indicators. By establishing a clear and organized form, it simplifies the inspection process for military personnel.
Purpose and Benefits of the US Army Information Security Inspection Checklist
The significance of the US Army Information Security Inspection Checklist lies in its ability to ensure compliance with critical information security protocols. Utilizing this military security compliance checklist enhances security measures and promotes proper handling of classified documents.
Moreover, the checklist standardizes inspection processes across various military units, facilitating consistent evaluations and improving overall security readiness.
Key Features of the US Army Information Security Inspection Checklist
This checklist is equipped with several crucial features that enhance its effectiveness in security management:
-
Items pertinent to security management and classified document handling.
-
Signature lines for the primary inspector and a section for compliance status.
-
Checkboxes and blank fields that facilitate ease of use during inspections.
These features collectively contribute to the comprehensive assessment of security protocols within military operations.
Who Needs the US Army Information Security Inspection Checklist?
The primary users of the US Army Information Security Inspection Checklist include roles such as Primary Inspectors who are responsible for conducting inspections within military units. This form is vital for military units of any size and mission type, providing a standardized approach to security evaluations.
Understanding when this form is necessary contributes to a more secure military environment.
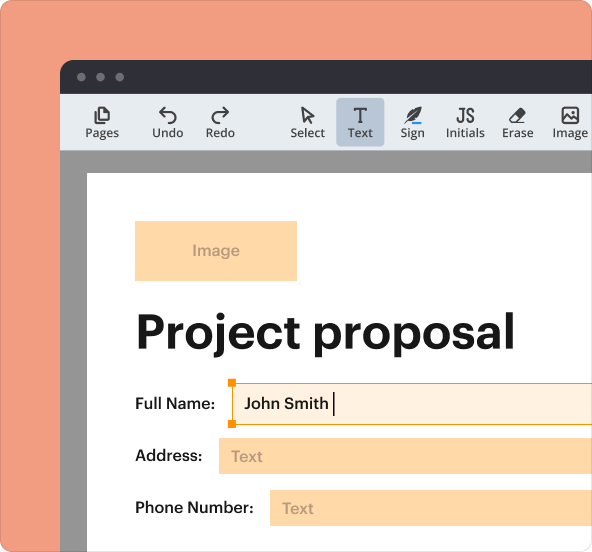
How to Fill Out the US Army Information Security Inspection Checklist Online (Step-by-Step)
To fill out the US Army Information Security Inspection Checklist online, follow these steps:
-
Access the checklist through an online platform.
-
Complete each section by filling in the relevant fields.
-
Ensure all checkboxes related to security compliance are marked.
-
Have the primary inspector sign and date where required.
-
Review the form for any errors before submission.
Utilizing a tool like pdfFiller can streamline the filling process, ensuring compliance and efficiency.
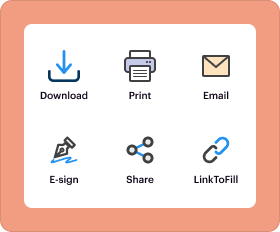
Submission Methods and Delivery of the US Army Information Security Inspection Checklist
Submitting the US Army Information Security Inspection Checklist can be done through various methods, including electronic submission and traditional paper forms. Users should follow recommended practices to ensure successful delivery of the form.
Be aware of deadlines and processing times for submissions to guarantee compliance with military protocols.
Common Errors and How to Avoid Them in the US Army Information Security Inspection Checklist
When completing the US Army Information Security Inspection Checklist, users may encounter several common mistakes:
-
Omissions of required signatures or dates.
-
Leaving sections incomplete or unchecked.
-
Failing to review the checklist before submission.
To prevent these issues, validating the form for accuracy and completeness before submission is crucial.
How pdfFiller Can Help with the US Army Information Security Inspection Checklist
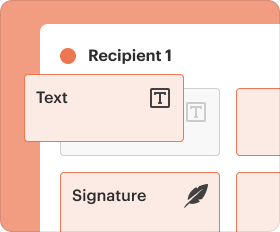
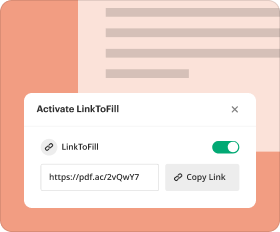
pdfFiller offers various advantages for users of the US Army Information Security Inspection Checklist. Key capabilities include:
-
Editing and annotating the checklist for clarity and accuracy.
-
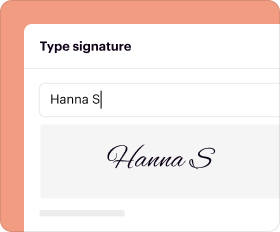
eSigning features that simplify the signing process for inspectors.
-
Robust security measures such as 256-bit encryption for handling sensitive documents.
By leveraging pdfFiller, users can ensure efficient form management while maintaining compliance with security regulations.
What Happens After You Submit the US Army Information Security Inspection Checklist?
After submitting the US Army Information Security Inspection Checklist, users can expect a series of confirmations regarding their submission status. Tracking submission status is advisable to ensure that all required aspects have been completed.
Maintaining proper record-keeping post-submission is also vital for future reference and audit purposes.
See an Example of a Completed US Army Information Security Inspection Checklist
Viewing a sample completed US Army Information Security Inspection Checklist can greatly aid in understanding the expectations for filling out the form. Focus on key areas within the example that are essential for compliance and inspection readiness.
A filled checklist serves not only as a record of compliance but also as a helpful reference for future inspections.
How to fill out the us army information security
-
1.Access the US Army Information Security Inspection Checklist on pdfFiller by searching for its title in the document search bar after logging in.
-
2.Once opened, examine the form layout. Familiarize yourself with the sections containing checkboxes for inspection items and fields for compliance status.
-
3.Before filling out the form, gather necessary information related to the inspection. This includes security policies in your unit, previous inspection reports, and compliance status for listed items.
-
4.Begin completing the checklist by clicking on each checkbox to indicate compliance status. Use the text fields to add detailed notes where necessary.
-
5.Pay special attention to the signature fields. Ensure that the primary inspector signs and dates the form within the designated area.
-
6.Review the completed checklist for any missed items or errors. Make sure all sections are filled accurately according to the security protocols.
-
7.Once satisfied with the information provided, you can download the completed checklist. Use the save function to securely store it on your device.
-
8.If submission is required, check the guidelines provided by your unit. Use pdfFiller to send the form via email or upload it to the designated portal, depending on submission methods.
Who is eligible to fill out the US Army Information Security Inspection Checklist?
The form should be completed by designated military inspectors, commanding officers, or authorized personnel responsible for information security compliance within military units.
Are there any deadlines for submitting this checklist?
Submission deadlines often depend on specific military operations or audit schedules. It is advised to check with your commanding officer for any applicable timelines related to the inspection.
How do I submit the completed checklist?
You can submit the completed checklist via email or through your unit's internal upload portal. Ensure compliance with your unit’s specific submission procedures.
What supporting documents are required with this checklist?
While the checklist itself is standalone, it may be helpful to attach relevant security policy documents, previous inspection reports, or any records showing compliance with AR 380-5.
What are common mistakes to avoid when filling out this checklist?
Common mistakes include failing to check all required boxes, neglecting to provide thorough remarks in the text fields, and overlooking the signature requirement before submission.
What is the processing time for the submitted checklist?
Processing time can vary based on the unit’s internal review protocols. Typically, expect a response within a few weeks, but check with your unit for specifics.
What additional resources are available for filling out this checklist?
You can consult the US Army regulations related to information security, or seek assistance from your unit's security officer for guidance on filling out the checklist accurately.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.