Last updated on Apr 3, 2026

Get the free System Authorization Access Request (SAAR) Form
We are not affiliated with any brand or entity on this form
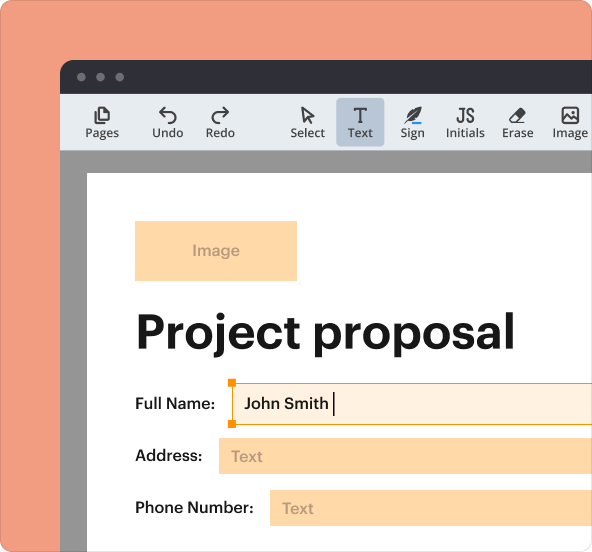
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is system authorization access request
The System Authorization Access Request (SAAR) Form is a government document used by the Department of Defense (DoD) to validate the trustworthiness of individuals seeking access to DoD systems and information.
pdfFiller scores top ratings on review platforms




Who needs system authorization access request?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to system authorization access request
Understanding the System Authorization Access Request (SAAR) Form
The System Authorization Access Request (SAAR) Form, known formally as DD Form 2875, serves a vital role within the Department of Defense (DoD). This form is specifically designed to validate the trustworthiness of individuals requesting access to DoD systems and information. It requires critical personal details, including the individual's name and social security number, making accuracy essential.
Key components of the SAAR Form include necessary fields such as user identification, organizational affiliation, and signature lines. Each of these elements plays an essential part in ensuring that only authorized personnel gain access to sensitive data, reinforcing the importance of trustworthiness among users within military and defense contexts.
The Importance of the SAAR Form in Military and Defense Context
The SAAR Form is critical for maintaining security and compliance in military environments. It safeguards sensitive information from unauthorized access, ensuring established protocols are adhered to, which ultimately enhances organizational integrity.
Requestors and supervisors must utilize the SAAR to establish controlled access levels for users, preventing unauthorized personnel from compromising sensitive systems. By implementing this form, the risks associated with potential security breaches are effectively mitigated, protecting national security assets and personnel.
Who Should Use the System Authorization Access Request (SAAR) Form?
The SAAR Form is intended for a diverse group of stakeholders involved in the access request process. Key roles include:
-
Requestor: Initiates the access request process and fills out the form.
-
Supervisor: Reviews the request and provides approval.
-
Information Owner: Validates the need for access based on job responsibilities.
-
IAO or Appointee: Ensures proper processing of the request.
-
Security Manager: Oversees compliance with security policies.
Each role has specific prerequisites for completing the form, including signing and dating it, ensuring all necessary approvals are in place prior to submission.
Step-by-Step Guide: How to Fill Out the SAAR Form Online
Filling out the SAAR Form online can be accomplished efficiently using tools like pdfFiller. Follow these steps for a smooth process:
-
Access the SAAR Form through pdfFiller's platform.
-
Complete each field, ensuring to enter accurate personal information.
-
Pay special attention to sensitive fields, such as social security number.
-
Review the form thoroughly to verify accuracy.
-
Submit the form electronically once all fields are completed.
Utilizing pdfFiller's features can help avoid common errors, so it's essential to familiarize yourself with the functionality they offer.
Common Mistakes to Avoid When Submitting the SAAR Form
Successful submission of the SAAR Form relies heavily on error-free completion. Some common mistakes to avoid include:
-
Neglecting to obtain signatures from required roles.
-
Entering incorrect personal details or organizational information.
-
Failing to review the form with stakeholders before submission.
Double-check compliance with all requirements and ensure that the form aligns with the expected standards to minimize the risk of rejection.
Submission Process for the SAAR Form
Once the SAAR Form is complete, users must navigate the submission process carefully. Acceptable submission methods include:
-
Email submission to the appropriate authority.
-
Physical mailing to the designated department.
After submission, users can expect a review process that may take time, and any delays or incomplete submissions could have consequences for access approval. It is essential to monitor the status following submission to ensure that access requests are addressed in a timely manner.
Understanding Security and Compliance Related to the SAAR Form
Handling sensitive information via the SAAR Form necessitates stringent privacy measures. Users must adhere to record retention requirements to comply with federal regulations, ensuring data is managed responsibly throughout and after the access request process.
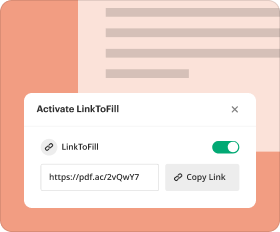
Platforms like pdfFiller employ rigorous security protocols, which are crucial when navigating the complexities of security compliance and data protection. Understanding these measures can help users feel confident about their safety while submitting information through digital means.
Streamlining Your SAAR Form Experience with pdfFiller
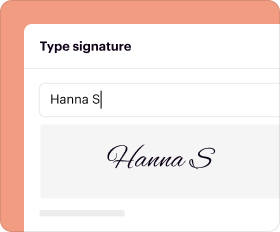
pdfFiller offers a robust solution to simplify the completion of the SAAR Form. Key features include eSignature capabilities and fillable fields that enhance the user experience. By utilizing these tools, users can significantly improve their efficiency in managing the form-filling process.
Additionally, pdfFiller maintains high-security standards, including 256-bit encryption and compliance with regulations such as HIPAA and GDPR, ensuring document protection throughout the filling and submission process. Embrace the ease of filling out the SAAR Form through pdfFiller for increased productivity and security.
How to fill out the system authorization access request
-
1.To access the System Authorization Access Request (SAAR) Form on pdfFiller, start by visiting the pdfFiller website and use the search bar to find 'SAAR Form' or 'DD Form 2875'.
-
2.Once located, click on the form to open it in the pdfFiller interface, where you can view and edit the document.
-
3.Before filling out the form, gather key information such as your name, social security number, organization details, and job title.
-
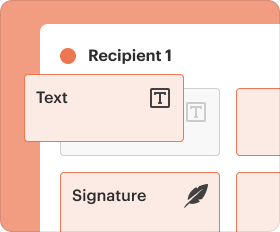
4.Begin filling in the required fields by clicking on each blank area or checkbox. pdfFiller allows you to type directly into the form or use dropdown menus, making it user-friendly.
-
5.Ensure to complete all necessary sections, including personal details and any required signatures from your supervisor, information owner, and security manager.
-
6.After completing the form, review all entered information thoroughly to confirm accuracy and completeness.
-
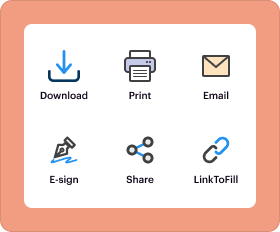
7.Finalize your document by saving it on pdfFiller. You can download it as a PDF, print directly from the platform, or share via email for further processing.
-
8.If submitting the form, ensure it reaches the appropriate security office or department as per your organization's instructions.
Who is eligible to fill out the SAAR Form?
Any individual seeking access to Department of Defense systems, including military personnel and defense civilians, is eligible to fill out the SAAR Form. Approval from supervisors and security managers is also necessary.
Is there a deadline for submitting the SAAR Form?
While there is no specific deadline for submitting the SAAR Form, it is advisable to submit it as soon as access is required to avoid delays in account setup.
How do I submit the SAAR Form once completed?
After completing the SAAR Form, it should be printed and submitted to your organization’s security office or designated personnel for processing and necessary approvals.
What supporting documents do I need with the SAAR Form?
Typically, you may not need additional documents beyond the filled-out form. However, it's important to confirm with your security office if specific identification or justification is required.
What are common mistakes to avoid while filling out the SAAR Form?
Common mistakes include omitting required fields, providing incorrect personal information, and failing to obtain all necessary signatures. Always double-check for completeness before submission.
How long does it take to process the SAAR Form?
The processing time for the SAAR Form varies by department. Generally, it can take from a few days to several weeks, depending on the organization's policies and workload.
What if I need to change or revoke access after my SAAR Form is submitted?
To change or revoke access, you’ll need to submit a new SAAR Form indicating the required changes and obtain the necessary approvals from relevant authorities.
Related Catalogs
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.