Last updated on Apr 3, 2026

Get the free FIPS 199 System Categorization Form
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
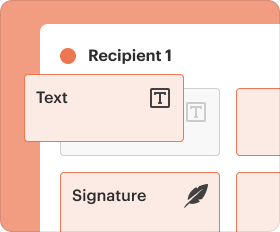
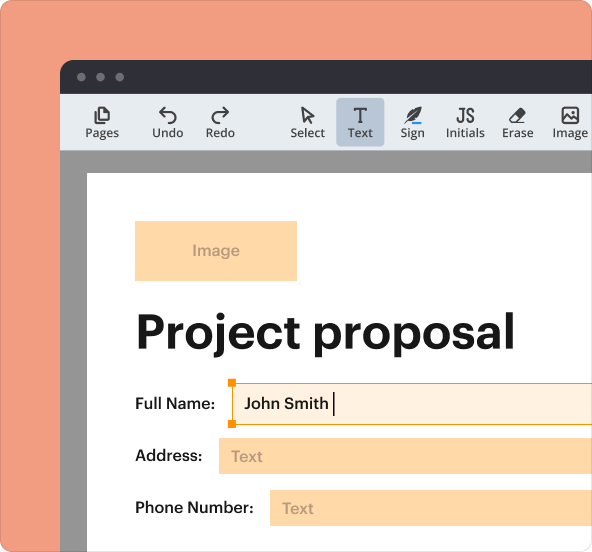
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is fips 199 system categorization
The FIPS 199 System Categorization Form is a government document used by federal agencies to categorize information systems based on potential security impacts.
pdfFiller scores top ratings on review platforms




Who needs fips 199 system categorization?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to fips 199 system categorization
What is the FIPS 199 System Categorization Form?
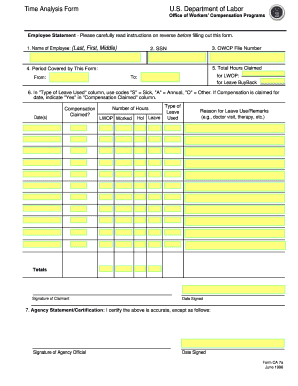
The FIPS 199 System Categorization Form is a critical document utilized by government agencies to categorize information systems based on the potential impact of unauthorized disclosure, modification, or destruction of information. Its primary purpose is to assess security categories, ensuring compliance with the Federal Information Processing Standards. Categorizing information systems is significant as it helps to determine the safety measures needed to protect sensitive data.
The form requires the signature of the Designated Approving Authority (DAA), which symbolizes accountability and oversight within the system security framework. Properly completing and signing this form is crucial for establishing a reliable security posture for federal agencies.
Purpose and Benefits of the FIPS 199 System Categorization Form
The FIPS 199 System Categorization Form serves multiple purposes, most notably in aiding government agencies to assess the security categories of their systems. By utilizing this form, organizations can ensure compliance with stringent federal regulations while significantly enhancing their overall security posture.
Using the form also addresses potential risks, such as unauthorized access or modification of sensitive information, which can have dire consequences. Key benefits include standardization within agencies, which fosters a cohesive approach to information security practices.
Who Needs the FIPS 199 System Categorization Form?
Key personnel responsible for completing the FIPS 199 System Categorization Form include the Designated Approving Authority (DAA), Information System Security Officer (ISSO), and System Owners. Each role has specific responsibilities in the process of form completion and carries implications for signing.
-
The DAA is responsible for the final approval and must sign the form.
-
The ISSO assists in categorizing the information system's security needs.
-
System Owners provide essential information regarding the system they manage.
Various government agencies may find the form relevant, particularly in scenarios where systems handle sensitive or classified data.
How to Fill Out the FIPS 199 System Categorization Form Online
To complete the FIPS 199 System Categorization Form using pdfFiller, follow these steps:
-
Access the form through pdfFiller's platform.
-
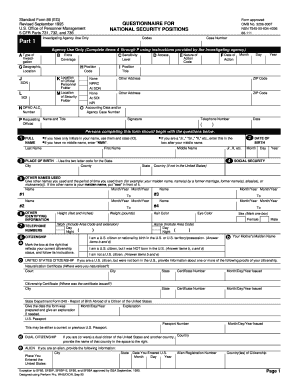
Enter the required system information, including the system name and description.
-
Select the appropriate impact levels based on your assessment.
-
Complete any additional required fields as instructed.
-
Review the form for accuracy and ensure all necessary information is included.
-
Submit the completed form electronically through the platform.
Utilizing an online editor like pdfFiller streamlines the completion process, allowing for easy editing and eSigning.
Field-by-Field Instructions for the FIPS 199 System Categorization Form
Each field in the FIPS 199 System Categorization Form plays a vital role in accurately reflecting the information system's security requirements. Users should provide detailed information based on the specific prompts within the form.
Some common mistakes to avoid include:
-
Failing to accurately assess impact levels.
-
Providing vague descriptions in the system information field.
By following the field instructions closely, users can enhance the accuracy of their submissions and ensure compliance with required standards.
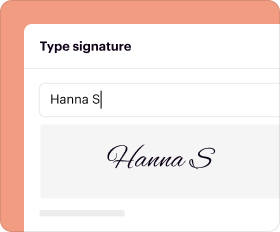
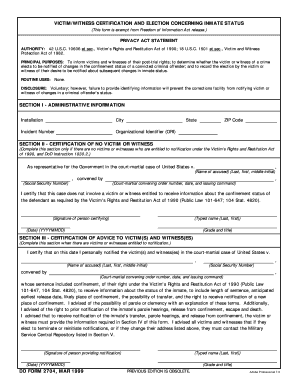
How to Sign the FIPS 199 System Categorization Form
Signing the FIPS 199 System Categorization Form is essential for ensuring accountability, particularly with the DAA's signature indicating final approval. Options for signing include traditional wet signatures and digital signatures.
Utilizing pdfFiller for eSigning provides a seamless experience, ensuring that signatures are securely captured. Digital signatures offer advantages over wet signatures, including easier tracking and enhanced security through encryption.
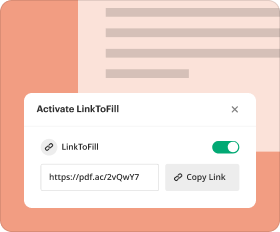
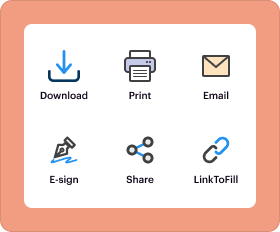
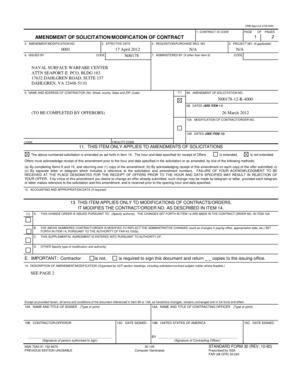
Submission Methods for the FIPS 199 System Categorization Form
Users have several options for submitting the completed FIPS 199 System Categorization Form:
-
Email submission directly through the pdfFiller platform.
-
Physical mailing of the printed form, ensuring it is sent to the correct address.
Keep in mind the importance of understanding deadlines and keeping a copy of the submission for records. Confirmation of receipt may be required depending on the submission method chosen.
Security and Compliance for the FIPS 199 System Categorization Form
When handling the FIPS 199 System Categorization Form, data protection and compliance are of utmost importance. Security measures such as 256-bit encryption help safeguard sensitive information throughout the submission process.
Agencies must also comply with regulations like HIPAA and GDPR in relation to record retention requirements. Non-compliance can have serious implications for government agencies, making it imperative to adhere to all security protocols when managing this form.
Using pdfFiller to Simplify Your FIPS 199 System Categorization Form Process
pdfFiller enhances the FIPS 199 System Categorization Form process by offering a comprehensive platform that simplifies form filling. Users can edit, eSign, and securely share documents all in one place, making compliance easier to achieve.
With over 100 million users relying on pdfFiller, the platform stands out as a trusted solution for government forms, offering capabilities that ensure efficient document management.
How to fill out the fips 199 system categorization
-
1.Access pdfFiller and locate the FIPS 199 System Categorization Form using the search feature.
-
2.Open the form in pdfFiller’s interface for editing.
-
3.Gather necessary information beforehand, such as system details and impact level criteria.
-
4.Begin filling the form by entering system information in the designated fields.
-
5.Use the provided instructions to evaluate and input the impact levels accurately.
-
6.Consult with colleagues if unsure about specific categorizations or signatures required.
-
7.Ensure that the Designated Approving Authority (DAA) reviews all completed information.
-
8.Obtain the required signatures, especially from the DAA, ensuring compliance.
-
9.Once all fields are completed and signed, review the document for any errors or missed items.
-
10.Finalizing the form involves saving your work and correcting any discrepancies.
-
11.To save, click the download button to store the file on your computer.
-
12.Submit the completed form as per your agency's protocols, which may include emailing or uploading in a centralized system.
Who is eligible to complete the FIPS 199 System Categorization Form?
Eligibility to complete the form generally includes personnel in specific roles such as the Designated Approving Authority, System Owners, and Information System Security Officers within federal agencies.
Are there deadlines for submitting the FIPS 199 form?
While there may not be universal deadlines, agencies typically establish internal timelines for submission to align with compliance reviews or audits. Check with your agency for specifics.
How can the FIPS 199 System Categorization Form be submitted?
The form can be submitted digitally by uploading it to the relevant government system or emailing it to designated authorities as per your agency's submission guidelines.
What supporting documents are required when submitting the FIPS 199 form?
Typically, accompanying documents may include security assessment reports, risk assessments, and any previous categorization materials relevant to the system being evaluated.
What are common mistakes to avoid when filling out the form?
Common errors include incomplete fields, missing signatures, failing to specify the correct impact levels, and not consulting the provided instructional guidance before submission.
How long does processing take after submitting the FIPS 199 form?
Processing times can vary by agency but usually depend on internal review mechanisms. On average, it may take two to four weeks for formal assessments to be completed.
What concerns should I address when using the FIPS 199 form?
Ensure clarity in defining the security categories, accurately assess impact levels, and review for compliance with the latest federal security standards to avoid future security vulnerabilities.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.