Last updated on Apr 4, 2026

Get the free Security Vulnerability Self-Assessment Guide
We are not affiliated with any brand or entity on this form
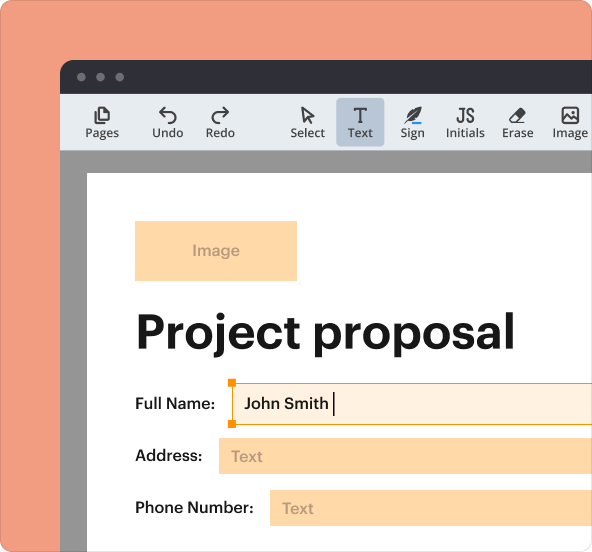
Why pdfFiller is the best tool for your documents and forms
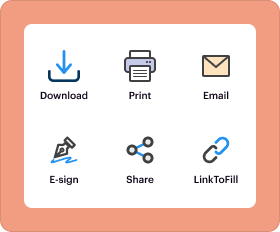
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is security vulnerability self-assessment guide
The Security Vulnerability Self-Assessment Guide is a form used by small drinking water systems in the United States to identify and address potential security vulnerabilities.
pdfFiller scores top ratings on review platforms




Who needs security vulnerability self-assessment guide?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to security vulnerability self-assessment guide
What is the Security Vulnerability Self-Assessment Guide?
The Security Vulnerability Self-Assessment Guide serves as a crucial document for small drinking water systems in the United States, specifically those catering to populations between 3,300 and 10,000. This guide is designed to assess and address potential security vulnerabilities within these systems, emphasizing the importance of proactive measures.
Water system personnel, including management and security teams, are the primary users of this guide, which equips them with the necessary resources to improve their water system security. These personnel directly interact with the various components of the water system and play a vital role in safeguarding public health.
Importance and Benefits of the Security Vulnerability Self-Assessment Guide
Completing the Security Vulnerability Self-Assessment Guide is essential for identifying weaknesses in water systems and enhancing overall security. By engaging in this assessment, water systems can discover vulnerabilities that might compromise public safety and environmental integrity.
Submitting the guide is a legal requirement enforced by the U.S. EPA Administrator, with serious potential consequences for systems that neglect this responsibility. Ensuring compliance not only protects water safety but also upholds regulatory standards.
Who Needs the Security Vulnerability Self-Assessment Guide?
The guide is meant for a variety of water system personnel who are tasked with completing the assessment form. Roles may include operators, managers, engineers, and security officers, all of whom share the responsibility of maintaining water infrastructure protection.
By understanding their specific responsibilities, these individuals can effectively utilize the guide to bolster water system security. Examples of teams that would benefit include risk assessment teams and emergency response coordinators.
Key Features of the Security Vulnerability Self-Assessment Guide
The assessment guide includes multiple sections critical for a comprehensive evaluation, such as:
-
Water sources
-
Treatment plants
-
Distribution systems
-
Personnel roles
-
Information storage
Additionally, there is an emergency contact list and requirements for the certification of completion. The guide provides explicit instructions to help users accurately fill out each section.
How to Fill Out the Security Vulnerability Self-Assessment Guide Online
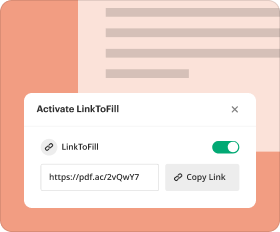
Filling out the Security Vulnerability Self-Assessment Guide online can be streamlined using pdfFiller. To begin, access the form through the platform, where detailed instructions guide users through each step.
A field-by-field breakdown highlights the specific information required, ensuring users gather necessary documents beforehand. This preparation allows for a smoother completion process and minimizes errors.
Submitting the Security Vulnerability Self-Assessment Guide
Submitting the guide involves several options, including online submissions and traditional mail. It is essential to be aware of the respective deadlines for filing to avoid delays in compliance.
While there may be fees associated with submission, understanding these potential costs is crucial. After submission, users will receive confirmation, and tracking options will be provided to ensure that the guide is processed correctly.
Common Mistakes to Avoid When Completing the Form
To enhance the accuracy of submissions, it is important to recognize common mistakes, particularly in frequently misfilled fields. Tips for reviewing completed forms before submission include cross-checking all entries against the requirements.
In case of errors, it is vital to have a clear understanding of how to amend submitted information, which can prevent complications later in the review process.
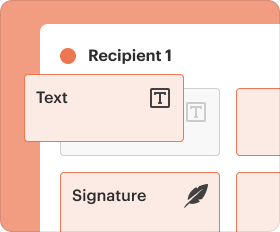
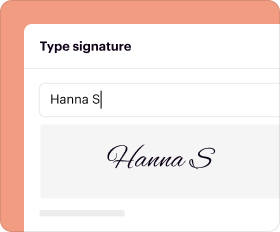
The Role of pdfFiller in Completing the Security Vulnerability Self-Assessment Guide
pdfFiller enhances the process of completing the Security Vulnerability Self-Assessment Guide by providing features such as text editing, signing, and form management. Users can leverage these capabilities to optimize their form-filling experience.
Moreover, pdfFiller ensures the security of sensitive information, complying with standards such as HIPAA and GDPR. This focus on security is critical when handling documents related to public health and safety.
What Happens After You Submit the Security Vulnerability Self-Assessment Guide
After submission, the U.S. EPA will conduct a thorough review of the provided information. Users can anticipate potential outcomes based on their submissions, which may require follow-up actions or additional information.
To check the application status, users should utilize the tracking options that confirm their submission was received and is in process, ensuring transparency throughout the review stage.
Navigating Security and Compliance with the Security Vulnerability Self-Assessment Guide
Adhering to necessary security standards is paramount when utilizing the Security Vulnerability Self-Assessment Guide. This includes understanding privacy and data protection protocols essential during the assessment phase.
Additionally, record retention requirements are critical for compliance with local and federal regulations. Properly maintaining these records protects the integrity of the water system and supports regulatory adherence.
How to fill out the security vulnerability self-assessment guide
-
1.Begin by accessing the Security Vulnerability Self-Assessment Guide on the pdfFiller platform. You can either search for the form by name in the search bar or navigate through the government forms section.
-
2.Once the form is open, take a moment to familiarize yourself with the layout. Each section is clearly labeled, and you will find blank fields, checkboxes, and instructions designed to guide your input.
-
3.Before filling in the fields, gather all necessary information about your water system. This includes details on water sources, treatment plants, distribution systems, personnel, and your emergency contact list.
-
4.As you navigate through the form, click on each blank field to enter the required information. Use pdfFiller’s annotation tools if needed to add notes or comments for clarity.
-
5.Make sure to complete every mandatory section of the form, paying close attention to the checkboxes and ensuring that all relevant data is filled out accurately.
-
6.After you have filled in all the necessary information, take a moment to review the entire form carefully. Check for any missing information and ensure all entries are correct.
-
7.Once satisfied with your completion of the guide, you can save your progress at any time. If you're ready to submit, navigate to the submission options.
-
8.To finalize the submission, download the completed form to save a copy for your records. You can also send it directly to the U.S. EPA Administrator as required, ensuring that your submission arrives by the set deadline.
Who is eligible to complete the Security Vulnerability Self-Assessment Guide?
The form is designed for personnel of small drinking water systems in the United States serving populations between 3,300 and 10,000 people. The system manager or designated staff should complete it.
What is the deadline for submitting this form?
The completed form must be submitted to the U.S. EPA Administrator by June 30, 2004. Ensure all sections are filled out accurately before submission.
How do I submit the Security Vulnerability Self-Assessment Guide?
The completed form can be submitted electronically via pdfFiller by downloading it, or it may be mailed directly to the U.S. EPA Administrator as per requirements. Ensure the signature is included if necessary.
Are there any supporting documents required with this form?
The form itself does not specify additional documents; however, it would be prudent to have your emergency contact list and other relevant records on hand for accurate completion.
What common mistakes should I avoid while filling out the form?
Make sure to read instructions carefully, avoid missing any mandatory fields, and double-check your entries for accuracy. Misunderstanding checkboxes or omitting the signature can lead to rejection.
How long does it take to process this form after submission?
Processing times can vary based on workload and submissions received by the U.S. EPA. Typically, you can expect to receive confirmation or further instructions shortly after submission.
What if I need help while completing the form?
If you encounter any issues, pdfFiller provides assistance through its support features, including tutorials and customer support options. Additionally, consulting with colleagues or legal advisors may be beneficial.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.