Last updated on Apr 4, 2026

Get the free Malicious Product Tampering Application
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
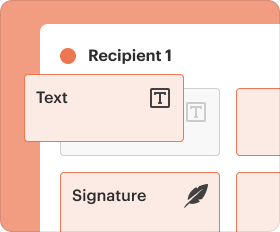
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
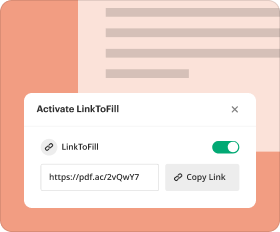
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

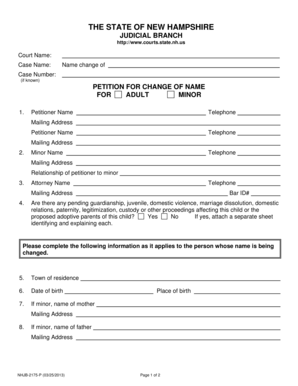
What is malicious product tampering application
The Malicious Product Tampering Application is a business form used by companies to apply for insurance coverage against product tampering and accidental contamination.
pdfFiller scores top ratings on review platforms




Who needs malicious product tampering application?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to malicious product tampering application
What is the Malicious Product Tampering Application?
The Malicious Product Tampering Application serves a vital role for businesses seeking insurance coverage against the risks of product tampering and accidental contamination. This application is essential for companies that manufacture, process, or distribute products susceptible to tampering. Scenarios in which businesses may require this form include instances of previous product tampering incidents or when entering into contracts that necessitate higher insurance coverage due to their operational hazards.
Purpose and Benefits of the Malicious Product Tampering Application
The Malicious Product Tampering Application offers significant advantages, particularly for insurance coverage. By utilizing this form, businesses can better manage risks related to product tampering and accidental contamination. Key benefits include enhanced protection for brand reputation, financial coverage for potential losses, and peace of mind knowing that their operations are safeguarded against unforeseen incidents.
Additionally, this application aids in establishing rigorous risk management protocols, which can reduce liability exposure and improve overall corporate governance.
Who Needs the Malicious Product Tampering Application?
A variety of businesses and industries should consider applying for the Malicious Product Tampering Application. These typically include food and beverage manufacturers, pharmaceutical companies, and consumer goods suppliers. Corporate roles most responsible for filling out this application often encompass risk management officers, quality assurance managers, and compliance directors, ensuring that all necessary information is accurately provided.
Eligibility Criteria for the Malicious Product Tampering Application
To successfully apply for the Malicious Product Tampering Application, certain eligibility criteria must be met. Businesses should have established quality assurance plans and provide specific details regarding their operations and product lines. Required information may include:
-
Historical data on previous incidents of tampering.
-
Information about suppliers and manufacturing locations.
-
Records of product safety protocols.
How to Fill Out the Malicious Product Tampering Application Online (Step-by-Step)
Filling out the Malicious Product Tampering Application online can be accomplished efficiently by following these steps:
-
Access the application through the designated online platform.
-
Gather company information, including product details and operational history.
-
Complete all required fields accurately, ensuring no sections are left blank.
-
Review the application for any errors or omissions.
-
Submit the completed application and retain a confirmation for tracking purposes.
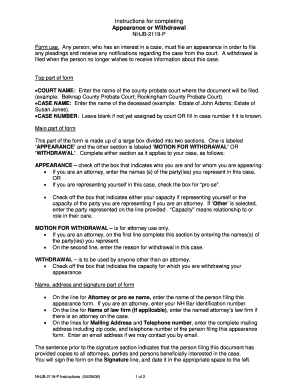
Field-by-Field Instructions for the Malicious Product Tampering Application
Each section of the Malicious Product Tampering Application requires careful attention. Key fields typically include:
-
Name of the applicant, which must be complete and precise.
-
Detailed description of the product and associated risks.
-
Historical tampering incidents, where applicable.
Common errors to avoid include incomplete answers and missing documentation, as these can lead to application delays or denials.
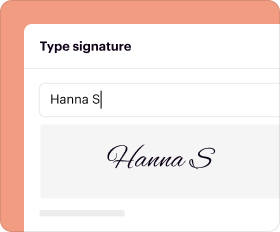
How to Sign and Submit the Malicious Product Tampering Application
The signing process for the Malicious Product Tampering Application is crucial, requiring the authorized corporate officer's signature to verify the accuracy of the information provided. Submission methods may include online submission or physical mailing, depending on the requirements outlined by the insurance provider. Once submitted, applicants can track their application status to remain informed about its processing.
Fees, Deadlines, and Processing Time for the Malicious Product Tampering Application
Applying for the Malicious Product Tampering Application may involve associated fees, which can vary based on the insurance provider. Some providers may offer fee waivers under certain conditions. It is essential to keep track of application deadlines and typical processing times, as this helps manage expectations regarding approval timelines.
What Happens After You Submit the Malicious Product Tampering Application?
After submitting the Malicious Product Tampering Application, applicants can expect to receive confirmation of submission, allowing them to monitor the status. Potential outcomes following review may include approval of coverage or denial, with rejection reasons typically communicated to guide reapplication efforts.
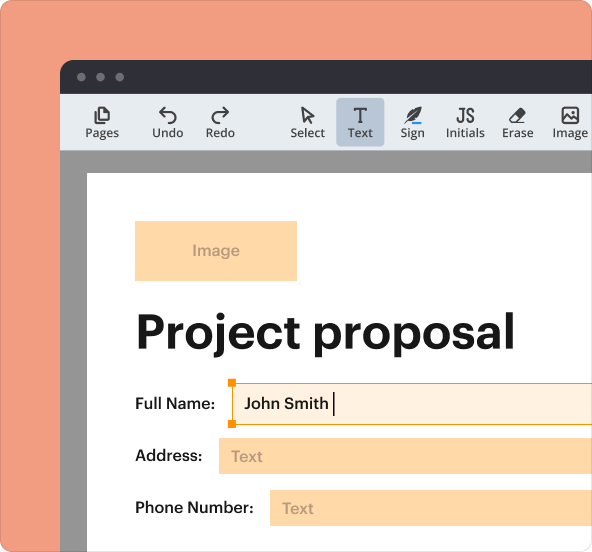
Why Choose pdfFiller for Your Malicious Product Tampering Application?
pdfFiller simplifies the process of completing the Malicious Product Tampering Application through its user-friendly platform. The tool ensures security features such as 256-bit encryption, making it suitable for handling sensitive documents. Additionally, pdfFiller's capabilities enhance efficiency in form completion, ensuring a smooth experience for users managing their applications.
How to fill out the malicious product tampering application
-
1.To complete the Malicious Product Tampering Application on pdfFiller, first, visit pdfFiller's website and log into your account.
-
2.Search for the 'Malicious Product Tampering Application' using the search bar or navigate through the business forms section.
-
3.Once you find the form, click on it to open in the pdfFiller editing interface.
-
4.Start filling in the applicant’s details, including the name, contact information, and the business’s operations summary.
-
5.Gather information regarding your company's products, sales data, manufacturing locations, and previous incidents of tampering or contamination before filling out the form.
-
6.Utilize pdfFiller’s drag-and-drop feature to add any necessary documents or upload required supporting files directly.
-
7.Complete all sections of the form, ensuring to check boxes and fill mandatory fields as indicated by the instructions.
-
8.After reviewing your inputs for accuracy, navigate to the signature section and add an authorized corporate officer’s signature using pdfFiller’s e-signature tool.
-
9.Once everything is complete, review the entire form for errors or omissions.
-
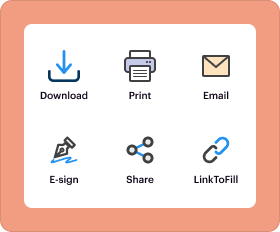
10.To save your application, click on 'Save' or 'Download' to keep a copy for your records.
-
11.If desired, submit the form directly via email or download it to submit through other channels by clicking on the appropriate option in pdfFiller.
Who is eligible to apply using the Malicious Product Tampering Application?
Any business involved in manufacturing or distributing products that require coverage against tampering or contamination can apply using the Malicious Product Tampering Application, provided they have an authorized corporate officer to sign.
What is the deadline for submitting this application?
There is typically no strict deadline, but it is advisable to submit the application as soon as possible to ensure coverage before any potential incidents occur. Always check with your insurance provider for specific timelines.
How should I submit the Malicious Product Tampering Application?
You can submit the completed application through pdfFiller by either emailing it directly from the platform or downloading it for submission via physical mail or fax, depending on your insurance company’s requirements.
What supporting documents are required with the application?
Commonly required supporting documents may include proof of prior insurance, details about your product’s quality assurance plan, and any prior claims or incidents related to product tampering or contamination.
What are some common mistakes to avoid when filling out the form?
Ensure all fields are completed accurately and do not leave any sections blank. Common mistakes include failing to include required signatures and providing inaccurate information regarding product safety practices.
How long does it take to process this form?
Processing times for the Malicious Product Tampering Application can vary by insurance company but generally may take a few days to a couple of weeks. Check directly with your insurer for specifics.
What if I have questions while filling out the form?
If you have questions while completing the form, consider reaching out to your insurance agent for assistance or refer to pdfFiller's customer support for help navigating the platform.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.