Last updated on Apr 4, 2026

Get the free Computer Security Incident Handling Form
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

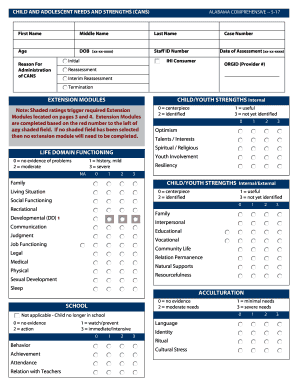
What is computer security incident handling
The Computer Security Incident Handling Form is a business document used by organizations to document and manage computer security incidents effectively.
pdfFiller scores top ratings on review platforms




Who needs computer security incident handling?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to computer security incident handling
What is the Computer Security Incident Handling Form?
The Computer Security Incident Handling Form is a critical document utilized by organizations to effectively document and manage computer security incidents. This form features various components crucial for comprehensive incident management, ensuring that every detail is recorded and addressed appropriately. It plays a pivotal role in the incident management process by providing a standardized method for reporting security incidents.
Utilizing a security incident reporting template helps organizations streamline their incident documentation, facilitating timely responses and effective communication among all parties involved in the incident response process.
Purpose and Benefits of the Computer Security Incident Handling Form
The primary purpose of the Computer Security Incident Handling Form is to assist organizations in documenting security incidents systematically. This form offers various benefits, such as aiding in the proper documentation necessary for an effective incident response. Moreover, it enhances communication between parties such as the Computer Incident Response Team (CIRT), corporate security, and legal affairs.
Additionally, using a cybersecurity incident form helps organizations maintain legal compliance and protects their interests during investigations. By filling out an incident survey form, teams can ensure that all necessary information is collected to comply with relevant regulations.
Key Features of the Computer Security Incident Handling Form
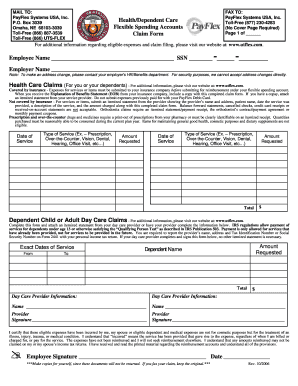
The Computer Security Incident Handling Form comprises essential features designed to facilitate incident documentation. Sections within the form include incident contact lists and identification details, allowing for efficient tracking of relevant parties involved in the response.
-
Fields for entering titles, contact information, and specifics about the incident.
-
Checkboxes for roles that require signing and acknowledgment by team members.
This structure ensures that critical information is captured and that all stakeholders, including those using the incident identification form, are properly engaged in managing security incidents.
Who Needs the Computer Security Incident Handling Form?
The Computer Security Incident Handling Form is essential for multiple roles within an organization. Required signatories include positions such as the Corporate Security Officer, Legal Officer, and the Chief Information Officer (CIO), among others. Each role plays a crucial part in ensuring the effective handling and resolution of security incidents.
-
Corporate Security Officer
-
CIO
-
Legal Affairs Officer
-
CIRT Member
-
Corporate Public Affairs Officer
Collaboration among these signatories is vital for a comprehensive approach to incident management, reinforcing the importance of the corporate security form in the documentation process.
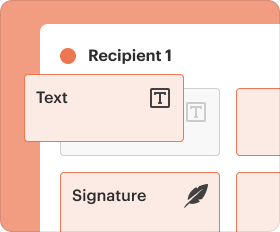
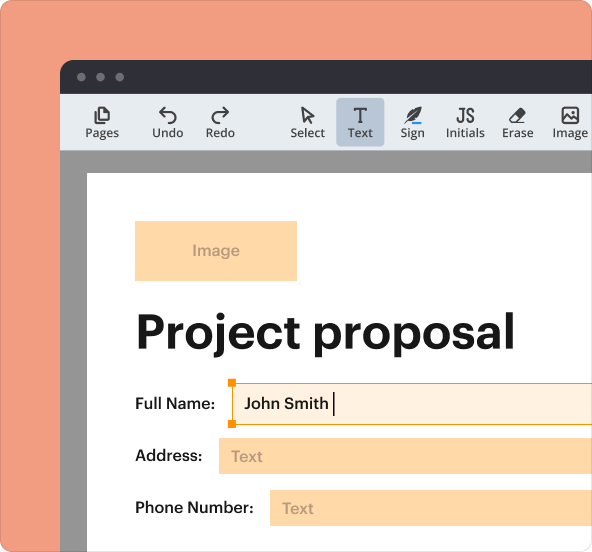
How to Fill Out the Computer Security Incident Handling Form Online
Completing the Computer Security Incident Handling Form online involves a straightforward process. Users can navigate through designated fillable fields intended for various types of information, including names, titles, and specific incident details.
-
Access the fillable form and identify the fields that require your input.
-
Enter the required details accurately, ensuring all information is up-to-date.
-
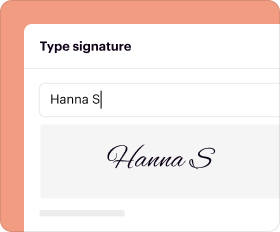
Add signatures as necessary to finalize the document.
This step-by-step guide simplifies the process of using the security incident reporting template, ensuring a confident and correct submission of the sans institute incident form.
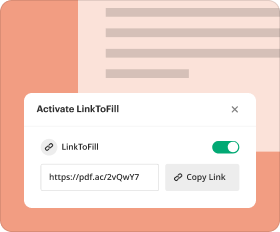
Submission and Delivery of the Computer Security Incident Handling Form
After completing the Computer Security Incident Handling Form, users must submit the document securely. Various methods are available for submission, including email and direct upload to secure platforms.
-
Ensure the form is submitted through secure electronic channels.
-
Implement best practices for secure delivery to protect sensitive information.
-
Monitor submission status to confirm successful delivery and receipt.
By following these guidelines, users can ensure effective use of the security incident management template during the submission process.
What Happens After You Submit the Computer Security Incident Handling Form?
Once the Computer Security Incident Handling Form is submitted, it enters a review process involving relevant stakeholders such as CIRT and Legal Affairs. It’s crucial to understand the next steps and potential outcomes resulting from the report.
-
Review by involved parties is initiated to assess the incident details provided.
-
Follow-up actions and communications are essential for ensuring resolution.
-
Late submissions can lead to complications or consequences affecting the organization.
Awareness of these process steps increases the significance of utilizing the security incident reporting template effectively.
Security and Compliance in Handling Sensitive Information
Assuring users of the security measures in place is paramount when using the Computer Security Incident Handling Form. The platform features robust security capabilities, including 256-bit encryption and compliance with HIPAA regulations.
-
Data protection and privacy are prioritized when filing sensitive documents.
-
Legal compliance in incident reporting is maintained to safeguard the organization’s interests.
These security measures underline the importance of utilizing the cybersecurity incident form properly and responsibly.
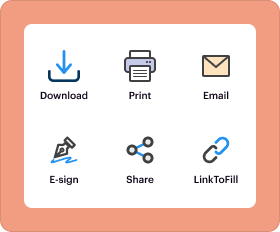
Utilizing pdfFiller for Effortless Form Handling
pdfFiller serves as an invaluable tool for users working with the Computer Security Incident Handling Form. The platform offers extensive capabilities such as editing, eSigning, and sharing forms efficiently.
-
Utilize pdfFiller’s features for seamless document management.
-
Experience the benefits of filling out the Computer Security Incident Handling Form through a user-friendly interface.
Users are encouraged to sign up for pdfFiller to enhance their document handling practices, especially regarding the corporate security form and other essential documents.
How to fill out the computer security incident handling
-
1.To access the Computer Security Incident Handling Form on pdfFiller, visit the pdfFiller website and log in to your account. If you do not have an account, you can create one for free.
-
2.Once logged in, use the search bar to type in 'Computer Security Incident Handling Form' and select it from the search results to open the form.
-
3.Navigate the form by clicking on each field. The interface allows you to fill in text fields by clicking directly on them, and checkboxes can be selected with a simple click.
-
4.Before you begin filling in the form, gather essential information such as incident specifics, involved parties, and contact details. Ensure that all data is accurate and complete.
-
5.Start entering the required information in the appropriate fields. You will find sections for names, titles, contact information, and incident details. Use the hints provided on the form to guide you.
-
6.Once you have filled in all mandatory fields, carefully review the document for any errors or missing information. This step is crucial to ensure all necessary details are included.
-
7.After reviewing the form, you can finalize it. If you need to print or send it digitally, choose the 'Download' option or save it directly to your pdfFiller account.
-
8.To submit the form, follow the instructions provided. You may need to email it to relevant stakeholders or print and sign it as needed.
Who is eligible to fill out the Computer Security Incident Handling Form?
The form can be filled out by anyone involved in the handling of security incidents, including corporate security officers, incident response teams, and legal affairs officers.
Are there deadlines for submitting the completed form?
While there are no specific deadlines mentioned, it is crucial to complete and submit the form as promptly as possible after an incident occurs to ensure timely incident response.
How should I submit the Computer Security Incident Handling Form?
You can submit the form by emailing it to the relevant stakeholders or authorities after printing and signing it. Alternatively, follow your organization’s internal submission procedures.
What supporting documents do I need to attach with the form?
Supporting documents may include detailed incident reports, evidence collected during the incident, and any prior correspondence related to the incident. Check with your organization for any specific requirements.
What common mistakes should I avoid when completing this form?
Common mistakes include incomplete fields, incorrect contact information, and missing signatures. Always double-check your entries before submitting the form.
How long does it take to process the submitted Computer Security Incident Handling Form?
Processing times may vary based on organizational protocols. However, you should follow up with the designated incident response team for specific timelines.
Can I edit the Computer Security Incident Handling Form after saving it?
Yes, if you save the form on pdfFiller, you can reopen it in your account to make edits before finalizing and submitting it.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.