Last updated on Apr 4, 2026

Get the free Bomb Threat / Suspicious Object Report
We are not affiliated with any brand or entity on this form
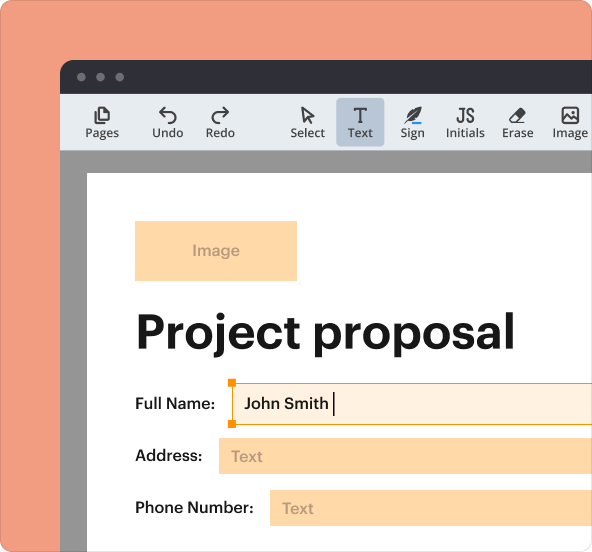
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
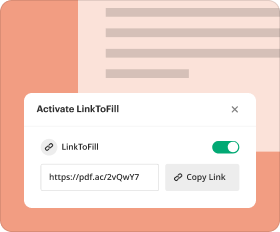
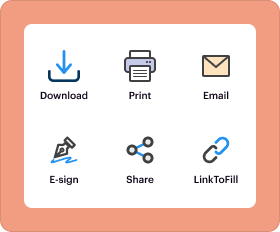
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is bomb threat suspicious object
The Bomb Threat / Suspicious Object Report is a form used by university personnel to document details of bomb threats or suspicious objects on campus.
pdfFiller scores top ratings on review platforms




Who needs bomb threat suspicious object?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to bomb threat suspicious object
What is the Bomb Threat / Suspicious Object Report?
The Bomb Threat / Suspicious Object Report is a specialized form designed to document the specifics of bomb threats and suspicious objects. This form serves as an essential tool for capturing critical details, enhancing safety protocols, and ensuring prompt communication with the authorities. Recording accurate information about these threats plays a significant role in campus security and response initiatives.
This report is a crucial component in managing potential risks that may arise in university settings. By utilizing the bomb threat report form or suspicious object report, individuals can contribute to a safer campus environment.
Purpose and Benefits of the Bomb Threat / Suspicious Object Report
Timely reporting of such incidents is vital for campus safety. The Bomb Threat / Suspicious Object Report facilitates swift action, allowing the university's police department to respond effectively. This procedure not only aids in immediate response but also emphasizes ongoing efforts to safeguard the community.
Utilizing this university police department form establishes a clear pathway for emergencies, thereby reinforcing the overall emergency response checklist and campus safety measures. Understanding the importance of this report ensures better preparedness among university staff.
Key Features of the Bomb Threat / Suspicious Object Report
The Bomb Threat / Suspicious Object Report contains several essential fields aimed at efficient data entry. Important elements include:
-
Time of call
-
Exact words of the caller
-
Specific questions to ask the caller
-
Details about the caller's voice and background noises
-
Information regarding the person receiving the call
This structured format allows users to make use of fillable fields and checkboxes, ensuring comprehensive documentation of every detail.
Who Needs the Bomb Threat / Suspicious Object Report?
This report is essential for various stakeholders within the university, including staff, faculty, and safety officers. Scenarios necessitating the use of this report often encompass any report of suspicious activity or direct bomb threats received through calls or reports.
By clearly identifying the target users and the contexts in which the form is required, the university can ensure all relevant personnel are equipped with the necessary tools for effective risk management.
How to Fill Out the Bomb Threat / Suspicious Object Report Online (Step-by-Step)
Filling out the Bomb Threat / Suspicious Object Report digitally is straightforward. Here’s a step-by-step guide:
-
Access the form using pdfFiller.
-
Begin by entering the time of the call in the designated field.
-
Capture the caller's words verbatim to ensure accuracy.
-
Proceed to answer all specific questions, circling back to details about the caller's voice as necessary.
-
Review all filled sections for completeness before submission.
Adhering to this guide will help ensure that critical information is documented appropriately through the campus safety form.
Common Errors and How to Avoid Them
Filling out the Bomb Threat / Suspicious Object Report can sometimes lead to common errors, impacting the effectiveness of this crucial document. Some frequent mistakes include:
-
Failing to capture the caller's exact words
-
Omitting the time of the call
-
Neglecting to fill in all required fields
-
Submitting without a final review
To maintain the integrity of the report, it is vital to validate all information before submission. Understanding these common pitfalls can help improve the accuracy of reporting.
What Happens After You Submit the Bomb Threat / Suspicious Object Report?
Once submitted, the Bomb Threat / Suspicious Object Report initiates a series of procedural steps. The submissions are reviewed by the university police department, which takes appropriate action based on the recorded information. Users can expect to receive updates regarding the status of their submissions.
Effective tracking of submitted reports is essential to ensure that all threats are evaluated and managed accordingly. This reinforces the university's communication protocol in emergency situations.
Security and Compliance for the Bomb Threat / Suspicious Object Report
When utilizing pdfFiller for the Bomb Threat / Suspicious Object Report, security measures are paramount. This includes the use of 256-bit encryption to protect sensitive data throughout the submission process. Compliance with regulations such as HIPAA and GDPR further ensures privacy during the management of such reports.
Being aware of these security measures positions users to handle sensitive information effectively, allowing for confident reporting.
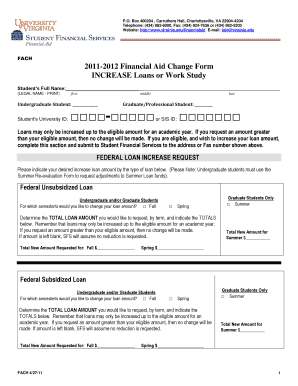
Sample or Example of a Completed Bomb Threat / Suspicious Object Report
Having a visual representation or example of a completed Bomb Threat / Suspicious Object Report can significantly enhance understanding. Each section of the form should exemplify accuracy, including filled fields for time of call, exact words of the caller, and any relevant notes on the call process.
This example serves as a guide for users to complete their forms correctly and comprehensively, ensuring all necessary details are recorded.
Experience Effortless Form Filling with pdfFiller
Using pdfFiller to complete and submit the Bomb Threat / Suspicious Object Report offers numerous advantages. The platform’s user-friendly interface streamlines the form-filling process while ensuring that submissions are accurate and timely.
Leveraging pdfFiller’s secure capabilities empowers users to report incidents confidently, enhancing overall campus safety.
How to fill out the bomb threat suspicious object
-
1.Access the Bomb Threat / Suspicious Object Report form on pdfFiller by searching for its title in the search bar.
-
2.Once the form opens, review the fields available, which include spaces for recording the time of the call, caller's words, and other crucial details.
-
3.Before starting, ensure you have all necessary information, such as the exact time, any background noises, and details about the caller's voice.
-
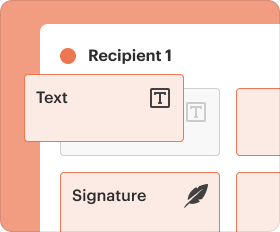
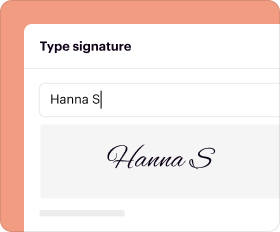
4.Begin filling out the form by clicking on the respective fields and entering the required information clearly and accurately.
-
5.Use the text boxes for free text responses and select appropriate options from checkbox fields as required by the form.
-
6.Once all fields are filled, review the information provided to check for any errors or omissions.
-
7.After confirming the form is complete, save your progress and download a copy if needed for your records.
-
8.Submit the form directly to the University Police Department through pdfFiller by following the submission instructions.
Who should use the Bomb Threat Report form?
The Bomb Threat Report form should be used by university staff, faculty, and any individuals who receive a bomb threat or notice a suspicious object. Immediate reporting to the University Police Department is essential.
What information do I need to gather before completing the form?
Before filling out the form, gather information such as the time of the call, the caller’s words, details about the caller's voice, any background noise, and the name of the person taking the report.
How do I submit the form once completed?
After completing the form on pdfFiller, you can submit it directly to the University Police Department through the platform. Ensure all fields are filled correctly before submission.
Is there a deadline for submitting this form?
There is no specific deadline for submitting the Bomb Threat Report form, but it should be filled out and submitted as soon as the threat has been received to ensure timely police response.
What are the common mistakes to avoid while filling this form?
Common mistakes include missing fields, providing vague information, and not reporting specific observations like time and background noise. Always double-check for completeness and accuracy.
Are there any fees associated with the use of this form?
There are no fees for using the Bomb Threat / Suspicious Object Report form as it is a governmental form intended for public safety and reporting.
Do I need to notarize this form?
No, the Bomb Threat / Suspicious Object Report form does not require notarization. It should be filled out and submitted directly to the appropriate authorities.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.