Last updated on Apr 4, 2026

Get the free McKesson Security Agreement
We are not affiliated with any brand or entity on this form
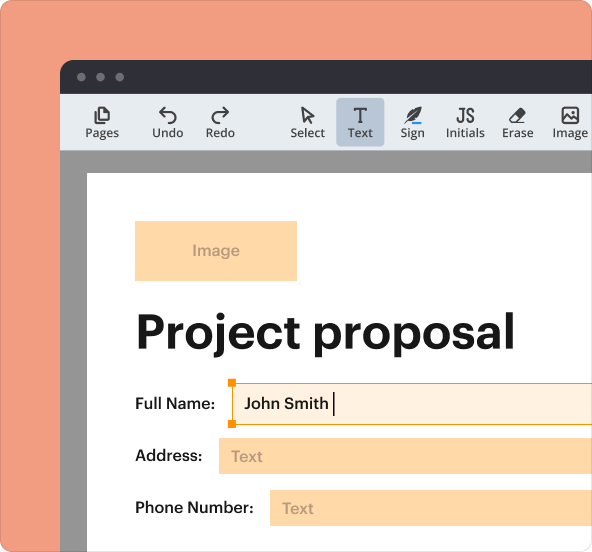
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

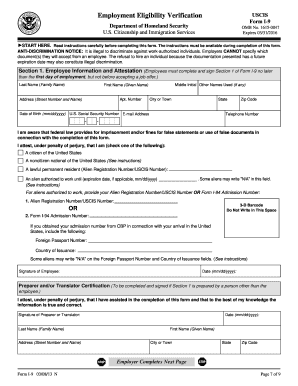
What is mckesson security agreement
The McKesson Security Agreement is a healthcare form used by the Medical University of South Carolina (MUSC) to safeguard patient information by regulating access to electronic medical records (EMR).
pdfFiller scores top ratings on review platforms




Who needs mckesson security agreement?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to mckesson security agreement
Understanding the McKesson Security Agreement
The McKesson Security Agreement is essential for safeguarding patient information within the healthcare system. Its primary purpose is to ensure the confidentiality and integrity of electronic medical records (EMR) at the Medical University of South Carolina (MUSC). The agreement is a crucial component for individuals who require access to sensitive patient data via McKesson and Citrix WebApps.
This healthcare security agreement not only protects individual patient information but also helps maintain compliance with industry regulations, promoting a secure environment for electronic health records.
Why You Need the McKesson Security Agreement
The necessity of the McKesson Security Agreement is underscored by the importance of patient information security in healthcare. This agreement outlines how confidentiality and integrity are maintained concerning electronic medical records (EMR). By signing this form, individuals contribute to protecting sensitive patient data from unauthorized access.
Ultimately, the agreement serves as a vital tool for ensuring the security of healthcare access forms and maintaining trust in the medical community.
Who Should Use the McKesson Security Agreement
The McKesson Security Agreement is designed for specific roles within the healthcare setting, including:
-
User
-
Department Chair/Supervisor
-
Sponsor
Each of these roles has implications regarding authorized access to EMR through McKesson and Citrix WebApps, emphasizing the need for careful oversight to protect patient information.
Key Features of the McKesson Security Agreement
The agreement includes several important sections and fields that users must complete, such as:
-
Personal information
-
Job details
-
Security questions
Understanding the significance of each of these sections is critical. Specific signatures from the user, department chair/supervisor, and sponsor (if applicable) ensure that access to patient data is handled securely.
How to Complete the McKesson Security Agreement
Completing the McKesson Security Agreement online requires attention to detail. Follow these steps:
-
Access the agreement form from the specified portal.
-
Fill in all required fields accurately, including personal and job information.
-
Address security questions with precise responses to enhance security protocols.
-
Obtain necessary signatures before finalizing the submission.
Common pitfalls include incomplete fields and failure to secure the required signatures, which can delay the process of obtaining access to EMR.
Submitting the McKesson Security Agreement
Upon completing the McKesson Security Agreement, submission can be done through various methods. Users should:
-
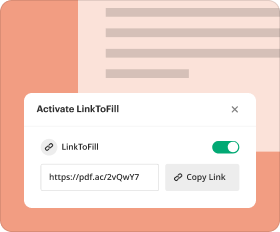
Submit the form online via the designated platform.
-
Consider offline submission options if required by the institution.
Often, supporting documentation may be necessary for the submission, so it's crucial to prepare these documents in advance.
Consequences of Not Submitting the McKesson Security Agreement
Failing to complete or submit the McKesson Security Agreement may lead to serious repercussions. Unauthorized access to patient information poses significant risks, not just to individual privacy, but also to the integrity of the healthcare system.
If the form is filed late or not submitted at all, individuals may face formal consequences including denial of access to EMR. Understanding these implications helps ensure compliance and security in the handling of patient data.
Ensuring Security and Compliance with the McKesson Security Agreement
Maintaining security and compliance when dealing with the McKesson Security Agreement involves implementing several key measures. Users should follow best practices for managing sensitive documents, such as:
-
Utilizing secure storage solutions for electronic documents.
-
Regularly reviewing compliance with relevant regulations, including HIPAA.
Adhering to these guidelines is paramount for protecting patient data and ensuring the integrity of healthcare processes.
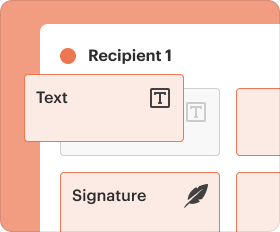
How pdfFiller Can Simplify the Process
pdfFiller offers numerous features that can enhance the experience of filling out the McKesson Security Agreement. Key benefits include:
-
Editability of PDFs to make necessary adjustments easily.
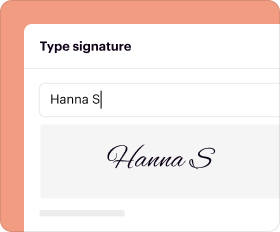
-
Secure eSigning capabilities that protect sensitive information.
These advantages make pdfFiller an ideal choice for handling healthcare security agreements efficiently and securely.
Next Steps After Completing Your McKesson Security Agreement
After submitting the McKesson Security Agreement, it's essential to track the status of your application. Users should also:
-
Check for confirmation of submission.
-
Be prepared to correct or amend the form if required in the future.
Always keep a personal copy of the agreement for your records, ensuring you have access to this important document as needed.
How to fill out the mckesson security agreement
-
1.Access the McKesson Security Agreement on pdfFiller by searching for the document title in the search bar or by navigating to the designated healthcare forms section.
-
2.Once opened, familiarize yourself with the fillable fields outlined in the form's structure.
-
3.Before starting to fill out the form, gather the necessary information, such as your first name, middle initial, last name, social security number, date of birth, phone number, job title, department/division, and email alias.
-
4.Begin entering your personal information in the respective fields. Use the placeholders as guides for the required format to ensure accuracy.
-
5.Complete all necessary sections that require information input, including personal details, department chair/supervisor information, and sponsor signature if applicable.
-
6.Double-check your entries for any typographical errors or missing information as you fill in the fields.
-
7.After filling out the form, review the entire document to ensure all sections are completed and accurate.
-
8.To finalize the form, add your signature and the date in the designated areas.
-
9.Once everything is filled out and reviewed, save the document by clicking on the save button in pdfFiller.
-
10.You can download the completed form for your records or submit it directly through pdfFiller, following any required submission methods the organization may have.
Who is eligible to fill out the McKesson Security Agreement?
Anyone requiring access to electronic medical records at MUSC must fill out the McKesson Security Agreement, including healthcare professionals, sponsors, and relevant supervisors.
What is the deadline for submitting the McKesson Security Agreement?
While specific deadlines may not be mentioned, it is advisable to submit the McKesson Security Agreement as soon as possible to ensure timely access to necessary patient information.
How do I submit the completed McKesson Security Agreement?
After completing the form, you can submit it via pdfFiller if applicable or follow the submission guidelines provided by your department or MUSC for the form's physical submission.
What supporting documents are required for this form?
Typically, supporting documents may include identification verification. However, confirm with your department for specific requirements when submitting the McKesson Security Agreement.
What are common mistakes to avoid when filling out the form?
Ensure all required fields are filled in completely, double-check for typographical errors, and confirm that your signature and date are included to avoid any processing delays.
How long does it take to process the McKesson Security Agreement?
Processing times can vary, but it is generally advisable to allow up to several days for the agreement to be reviewed and approved. Check with your department for specific timelines.
Can I edit my McKesson Security Agreement after submission?
Once submitted, changes may not be allowed unless explicitly specified by your department. It is best to check with them regarding any options for amendment to the submitted form.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.