Last updated on Apr 4, 2026

Get the free RIT Computer Security Checklist
We are not affiliated with any brand or entity on this form
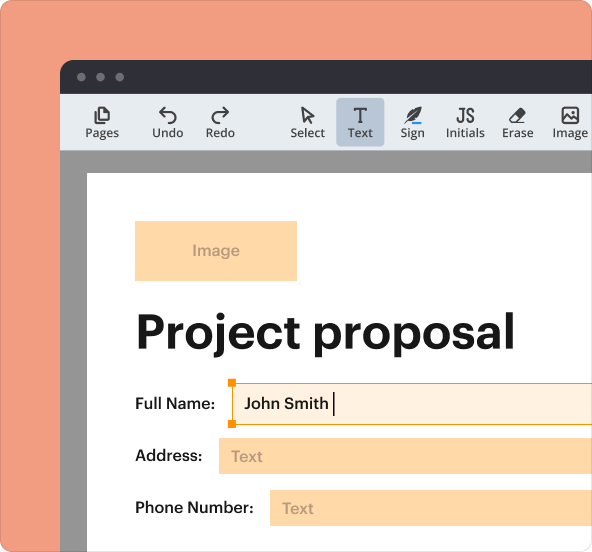
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is rit computer security checklist
The RIT Computer Security Checklist is a document used by end-users and managers at the Rochester Institute of Technology to ensure all computers connecting to the RIT network meet security requirements.
pdfFiller scores top ratings on review platforms




Who needs rit computer security checklist?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to rit computer security checklist
What is the RIT Computer Security Checklist?
The RIT Computer Security Checklist is a vital resource aimed at enhancing computer security at the Rochester Institute of Technology (RIT). This checklist serves as a guide for both end-users and managers, ensuring that necessary security measures are in place. The main purpose of the RIT Computer Security Checklist is to provide a standardized framework to confirm that computers connecting to the RIT network meet established security requirements.
Purpose and Benefits of the RIT Computer Security Checklist
The necessity of the RIT Computer Security Checklist stems from the imperative to maintain a secure computing environment. Confirming security measures is critical for protecting sensitive information. Key benefits of this checklist include:
-
Ensuring the installation of anti-virus software, security patches, and encryption efforts.
-
Facilitating compliance with RIT’s network security requirements.
-
Promoting awareness of security practices among users, which leads to overall enhanced protection.
Key Features of the RIT Computer Security Checklist
The RIT Computer Security Checklist encompasses several important components that must be verified. Essential items included in the checklist are:
-
Verification of anti-virus installation and functionality.
-
Confirmation of firewall settings and configurations.
-
Specific checks for RIT-owned or leased devices, including whole-disk encryption.
By utilizing the RIT security checklist template, users can ensure their compliance with required security protocols effectively.
Who Needs the RIT Computer Security Checklist?
This checklist must be completed by individuals in specific roles, primarily end-users and managers. Their signatures affirm compliance with security policies. Failure to complete this form can lead to significant implications, including non-compliance with network security measures.
How to Fill Out the RIT Computer Security Checklist Online (Step-by-Step)
Completing the RIT Computer Security Checklist is straightforward. Follow these steps for accurate completion:
-
Access the checklist using the pdfFiller platform.
-
Fill out the necessary fields, ensuring all sections are completed.
-
Verify that digital signatures are provided where required.
-
Review the checklist for compliance with RIT's security policies before submission.
Common Errors and How to Avoid Them When Completing the RIT Computer Security Checklist
Users often encounter certain pitfalls while filling out the checklist. Common errors include:
-
Missing signatures that could delay the processing of the form.
-
Failure to verify that all installations, such as software and security measures, are confirmed.
To ensure completeness, double-check that all fields are filled accurately before submission, as this is crucial for compliance.
Submission Methods for the RIT Computer Security Checklist
Once completed, the RIT Computer Security Checklist can be submitted through various methods. Users have the following options:
-
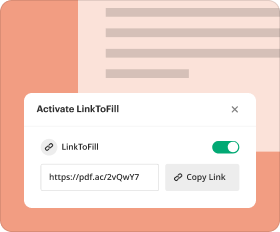
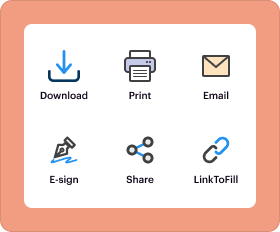
Online submission via the pdfFiller platform.
-
In-person delivery to designated administrative offices.
Be sure to adhere to any specific delivery requirements or deadlines as outlined on the form.
What Happens After You Submit the RIT Computer Security Checklist
After submission, users can expect a thorough review of the checklist. The process includes:
-
A confirmation of receipt and verification of the submitted details.
-
Potential follow-up in case of any incomplete or incorrect information.
This review is essential for maintaining ongoing security and compliance for the RIT Computer Security Checklist.
Using pdfFiller for the RIT Computer Security Checklist
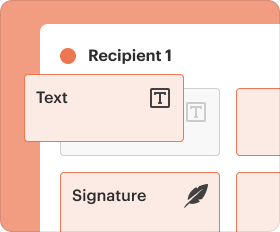
pdfFiller significantly enhances the experience of filling out and managing the RIT Computer Security Checklist. Key features of pdfFiller include:
-
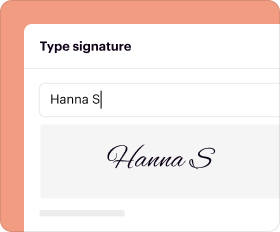
eSigning capabilities for quick completion and validation of the checklist.
-
Document sharing options for easy collaboration on security compliance.
-
Robust security measures, including 256-bit encryption, to protect sensitive data.
Leveraging pdfFiller tools ensures a more streamlined and secure process for completing the checklist efficiently.
How to fill out the rit computer security checklist
-
1.Access pdfFiller and search for the RIT Computer Security Checklist. Once located, click on the form to open it.
-
2.Use the navigation tools on pdfFiller to move through the form’s sections. Familiarize yourself with the layout and fields required.
-
3.Before completing the checklist, gather necessary information such as antivirus status, security patches, and encryption details related to the device you are documenting.
-
4.Begin filling out the form by entering your information in the designated fields, including confirming security measures like antivirus software and firewalls.
-
5.Ensure accuracy in your responses. Check off the specific security requirements relevant to RIT-owned or leased devices to meet compliance.
-
6.After completing the fields, review your answers carefully to ensure all required information is correct and complete.
-
7.Once satisfied with your response, move to the signature section. Print your name, sign, and ensure your manager's signature is obtained as well.
-
8.Finally, save the completed checklist, choose to download it for personal records, or submit it via email using pdfFiller's submission options.
Who is required to sign the RIT Computer Security Checklist?
Both the end-user and their manager must sign the RIT Computer Security Checklist to validate that required security measures have been implemented.
What is the purpose of the RIT Computer Security Checklist?
The checklist ensures that all computers connecting to the RIT network comply with security standards, including the necessary installation of antivirus software and firewalls.
Is there a deadline for submitting the completed RIT Computer Security Checklist?
While specific deadlines may depend on managerial directives, it is advisable to complete and submit the checklist routinely, especially before major network access changes or reviews.
What happens if the RIT Computer Security Checklist is not submitted?
Failure to submit the checklist may result in restricted access to the RIT network or potential disciplinary action, as compliance with security protocols is critical.
Are there any specific documents needed to fill out the checklist?
You will need access to your computer’s security status, such as antivirus installation and encryption settings, which should be recorded or noted prior to completing the checklist.
What common mistakes should I avoid when completing the checklist?
Avoid leaving any fields blank, ensure all security measures are properly checked, and double-check that both required signatures are obtained to prevent submission issues.
How quickly will the RIT Computer Security Checklist be processed after submission?
Processing times may vary; however, it is typically reviewed in accordance with the institution’s IT policies. Follow up with your manager if you do not receive confirmation.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.