Last updated on Mar 27, 2026

Get the free US DoD System Authorization Access Request Form
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is us dod system authorization
The US DoD System Authorization Access Request Form is a government document used by individuals to request access to Department of Defense systems and information.
pdfFiller scores top ratings on review platforms




Who needs us dod system authorization?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to us dod system authorization
What is the US DoD System Authorization Access Request Form?
The US DoD System Authorization Access Request Form, specifically the DD Form 2875, is essential for individuals seeking access to Department of Defense (DoD) systems. This form serves as a formal request within the military system access framework. It includes necessary fields to capture user details, such as NAME (Last, First, Middle Initial), and requires multiple signatures for validation.
Completing this form ensures that the requestor provides pertinent information, justifying their need for access to sensitive military systems, resonating with its significance in facilitating secure operations.
Purpose and Benefits of the US DoD System Authorization Access Request Form
The DD Form 2875 is pivotal in establishing authorized access to military systems. This form streamlines the application process for potential users by clarifying the security clearance process, which is vital for maintaining operational security.
Having authorized access offers myriad benefits, including enhanced operational capabilities, improved data accessibility, and compliance with regulatory standards. Understanding the necessity of this government security clearance form is essential for all potential requestors.
Who Needs the US DoD System Authorization Access Request Form?
Several roles within the military and government sectors are required to complete the DD Form 2875. The following individuals must participate in the signing process:
-
Requestor
-
Supervisor
-
Information Owner/OPR
-
IAO or Appointee
-
Security Manager
Each role has specific eligibility criteria that must be met to ensure the access request's validity. This comprehensive approach guarantees that all necessary parties review and approve the request.
How to Fill Out the US DoD System Authorization Access Request Form Online (Step-by-Step)
Completing the DD Form 2875 online involves several steps to ensure accuracy and compliance. Follow these directions carefully:
-
Access the online form and locate the required fields.
-
Input your NAME (Last, First, Middle Initial) and other personal details as needed.
-
Provide justification for your access request in the designated section.
-
Review all entries and ensure that required information is complete.
-
Proceed to obtain signatures from all involved parties within your organization.
This step-by-step process is crucial for ensuring that your submission is thorough and accurate, significantly enhancing the chances of approval.
Common Errors and How to Avoid Them
Filling out the DD Form 2875 can lead to several common mistakes. Understanding these pitfalls can streamline your application process:
-
Failing to gather all necessary signatures before submission.
-
Omitting required fields can lead to delays in processing.
-
Providing insufficient justification for access requests.
To avoid these errors, ensure all listed requirements are addressed and double-check your entries for completeness before you submit the form.
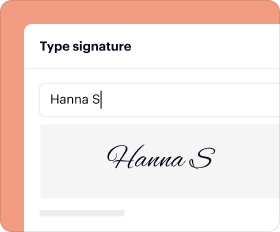
How to Sign the US DoD System Authorization Access Request Form
Signing the DD Form 2875 can be done through various methods. Depending on your organization's policies, consider the following:
-
Digital signatures are increasingly accepted for convenience.
-
Wet signatures may still be required for certain roles, such as the Security Manager.
It is imperative to secure all necessary signatures as specified in the submission guidelines, ensuring validation before proceeding with your request.
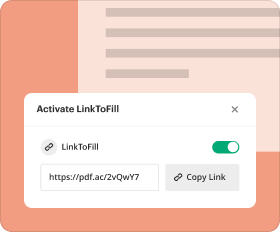
Where and How to Submit the US DoD System Authorization Access Request Form?
Upon completing the DD Form 2875, you should submit it via the appropriate channels, which can include:
-
Online submission through designated military portals.
-
Physical mail to the relevant office as per instructions.
Be mindful of submission methods and deadlines, as these factors can impact the processing time for access approvals. Timeliness is crucial to ensure a smooth review process.
What Happens After You Submit the US DoD System Authorization Access Request Form?
After submitting the DD Form 2875, it undergoes a review process. Understanding the potential outcomes is vital:
-
Your application will be assessed for completeness and accuracy.
-
Expect timelines for feedback on your request, which may vary.
Tracking the status of your application can be beneficial, allowing you to stay informed of any updates or required actions post-submission.
Security and Compliance for the US DoD System Authorization Access Request Form
When handling the DD Form 2875, security and compliance are of utmost importance. Key considerations include:
-
Utilizing services that offer 256-bit encryption to protect sensitive information.
-
Ensuring compliance with standards such as HIPAA and GDPR through secure document management practices.
Maintaining vigilance with data security measures fosters trust and protects the integrity of your access request.
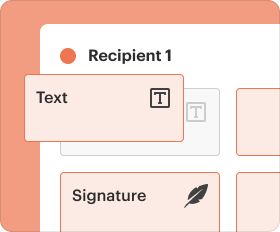
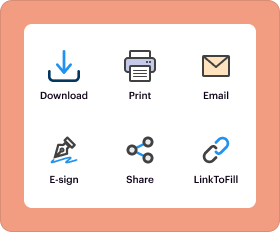
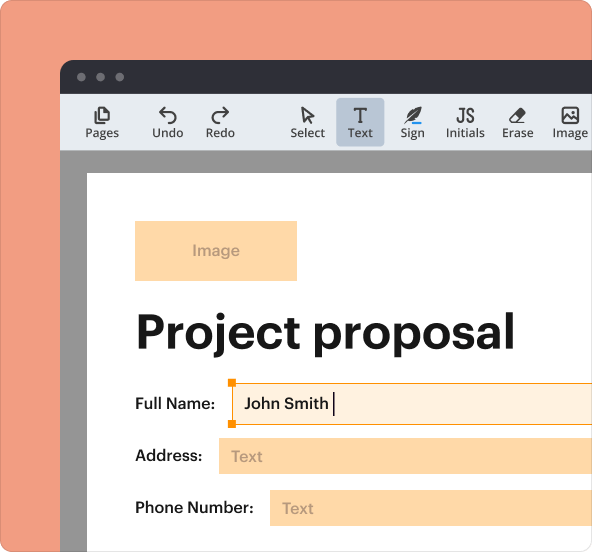
Experience Easy Form Management with pdfFiller
pdfFiller simplifies the form completion and management process, offering valuable tools for users. With features designed specifically for handling forms like the DD Form 2875, users can:
-
Edit and annotate documents easily.
-
eSign forms quickly and securely.
Leveraging pdfFiller enhances the experience of managing the US DoD System Authorization Access Request Form, providing a secure and efficient solution for all users.
How to fill out the us dod system authorization
-
1.Begin by visiting pdfFiller and log in or create an account if you haven't already.
-
2.Search for the US DoD System Authorization Access Request Form using keywords like 'DD Form 2875'.
-
3.Once the form is displayed, click on it to open it in the pdfFiller editor.
-
4.Review the form and gather necessary information, including personal details and organizational info.
-
5.Fill in your name, supervisor's details, and relevant backgrounds in the designated fields.
-
6.Use checkboxes to indicate what accesses you are requesting.
-
7.Complete required signature fields, verifying who needs to sign the document according to the form requirements.
-
8.Regularly save your work to prevent loss of any entered data.
-
9.Once all fields are filled, review the form for accuracy and completeness.
-
10.Use the preview option to see the final appearance of your completed form.
-
11.Save the filled form to your account for future access.
-
12.Download a copy of your completed form to your device.
-
13.Submit the form according to your organization's procedures, ensuring all approvers have signed.
Who is eligible to fill out the US DoD System Authorization Access Request Form?
Eligible applicants include military personnel, civilian employees of the DoD, and contractors who need access to DoD systems for their roles.
What is the deadline for submitting the request form?
There are typically no strict deadlines for this form, but it should be submitted as soon as access is needed. Delays in submission may postpone access approval.
How do I submit the completed US DoD System Authorization Access Request Form?
Submission methods vary by organization. Generally, you may need to email the completed form or submit it through a designated internal system.
What supporting documents are required when submitting the form?
Usually, you will need to provide identification and justification documents, such as your work credentials or a letter of approval from your supervisor.
What are common mistakes to avoid when filling out this form?
Ensure that all fields are completed clearly and accurately. Common mistakes include missing signatures and incorrect personal or organizational information.
How long does it take to process the access request?
Processing times can vary based on the organization and the nature of the request. Generally, allow several days to weeks for approval.
Can I make changes to the form after submitting it?
If you need to make changes after submission, contact your organization’s administrative office as soon as possible to request a re-evaluation.
Related Catalogs
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.