Last updated on Apr 5, 2026

Get the free System Authorization Access Request Form
We are not affiliated with any brand or entity on this form
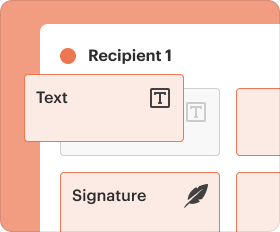
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is system authorization access request
The System Authorization Access Request Form is a security document used by the Department of Defense (DoD) to validate the trustworthiness of individuals requesting access to DoD systems and information.
pdfFiller scores top ratings on review platforms




Who needs system authorization access request?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to system authorization access request
What is the System Authorization Access Request Form?
The System Authorization Access Request Form, also known as DD Form 2875, is a critical document utilized by the Department of Defense (DoD) to facilitate access to military systems. This form serves to validate the trustworthiness of individuals seeking access to sensitive information, ensuring that only qualified personnel are granted permissions.
Completing this form requires providing detailed personal and organizational information, covering various roles that are responsible for signing off on the request. Among these roles, the requestor and supervisor stand out as key contributors, along with the information owner, Information Assurance Officer (IAO), and security manager.
Purpose and Benefits of the System Authorization Access Request Form
This form is essential for both individuals requesting access and the DoD, offering numerous benefits. Firstly, it establishes a standardized procedure, which promotes consistency and efficiency across access requests. Implementing this structured approach not only enhances security compliance but also fosters user accountability throughout the access process.
By completing the form accurately, requestors can significantly expedite approval times, thus contributing to a smoother integration of personnel into the system. Proper use of the access request form ensures compliance with national security regulations, thereby protecting sensitive information.
Key Features of the System Authorization Access Request Form
The System Authorization Access Request Form boasts several key features designed to improve the user experience and ensure compliance. It has a structured format that includes essential fields such as NAME, USER SIGNATURE, and DATE. Each section is designed to capture necessary information meticulously.
Furthermore, the form stipulates crucial signature requirements from a variety of roles including the requestor, supervisor, information owner, IAO, and security manager. It also incorporates sections specifically designated for background investigation verification and account information completion, reflecting the importance of thorough checks.
Eligibility Criteria for the System Authorization Access Request Form
Understanding who can submit the System Authorization Access Request Form is vital for compliance. The eligibility is defined by several specific roles that must sign the document, including the requestor and supervisor. Additionally, various organizational policies dictate the requirements based on security clearances.
To ensure the correct submission of the form, it is essential to review your organization's regulations, as these may introduce specific stipulations affecting who can initiate this process.
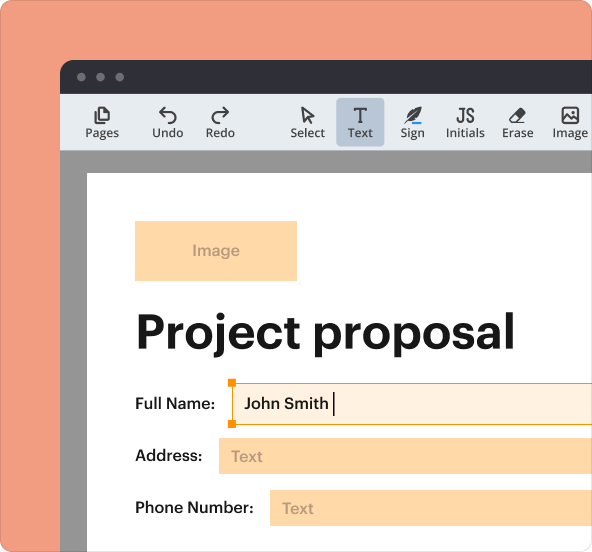
How to Fill Out the System Authorization Access Request Form Online (Step-by-Step)
Filling out the System Authorization Access Request Form digitally can streamline the process for users. To do this, follow these steps:
-
Access the form via pdfFiller.
-
Complete each field, ensuring to fill in NAME (Last, First, Middle Initial), USER SIGNATURE, and the DATE (YYYYMMDD).
-
Provide accurate personal and organizational details as required.
-
Gather signatures from all necessary parties, including your supervisor and security manager.
-
Ensure all sections are filled out to avoid common errors.
Careful attention to detail during this process will enhance accuracy and completeness, preventing delays or rejections.
Common Errors and How to Avoid Them
When completing the System Authorization Access Request Form, users frequently encounter common mistakes that can result in rejection. Here are the most prevalent errors:
-
Incomplete fields that have not been filled out accurately.
-
Missing signatures from required roles.
-
Incorrect formatting of important information such as dates.
To prevent these issues, double-check all entries for accuracy and review the form thoroughly before submission. Maintaining a review and validation checklist can also aid in identifying potential errors ahead of time.
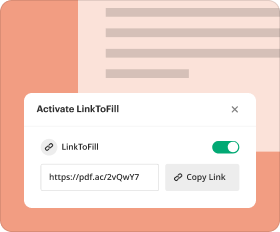
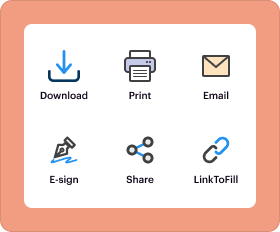
How to Submit the System Authorization Access Request Form
Once the System Authorization Access Request Form is completed, it can be submitted using a variety of methods. Users can choose from online submissions, mailing the form, or submitting it in person at designated locations. Be sure to check if any specific addresses are required for postal submissions.
Users should be aware of any potential fees associated with the submission process and anticipate the processing times for approvals, which can vary. After submission, tracking options or confirmation of receipt may also be available, ensuring you can stay informed about the status of your request.
Security and Compliance for the System Authorization Access Request Form
Security measures play a crucial role in the handling of the System Authorization Access Request Form. With sensitive information involved, data protection and privacy compliance are paramount. Users can be assured by the security features offered, including 256-bit encryption provided by pdfFiller.
It's also essential to emphasize adherence to regulatory frameworks such as SOC 2 Type II, HIPAA, and GDPR. These compliance measures are designed to protect user data and ensure that all handling processes are secure and trustworthy.
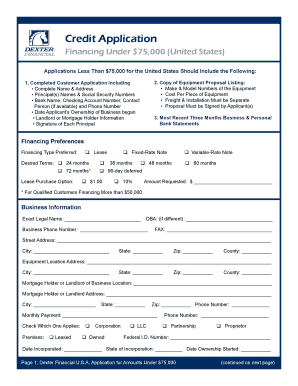
Sample or Example of a Completed System Authorization Access Request Form
To assist users in filling out the System Authorization Access Request Form correctly, a downloadable or viewable sample of a completed form is available. This example illustrates how to fill in the necessary sections clearly and accurately.
Pay particular attention to areas where users often have questions, as this reference can provide valuable insight during the completion process. It’s encouraged to utilize this sample alongside your own filling efforts.
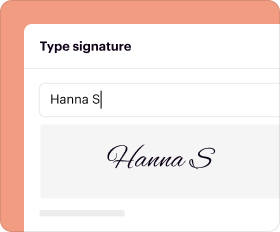
Unlock Your Access with pdfFiller
Using pdfFiller to complete the System Authorization Access Request Form offers significant advantages. The platform is designed for ease of use and helps streamline the process of filling out this important document. Additionally, the security and compliance measures in place ensure that your sensitive information is well-protected.
With pdfFiller, you can not only fill out the form but also eSign, edit, and manage your documents seamlessly, making your experience both efficient and secure.
How to fill out the system authorization access request
-
1.To begin, access pdfFiller and search for the 'System Authorization Access Request Form'. Open the form using the available editing tools.
-
2.Familiarize yourself with the form’s layout. Identify required fields including personal details, organizational information, and justifications for access.
-
3.Gather necessary information beforehand. This includes your name, departmental affiliation, access justification, and any relevant background details.
-
4.Fill in your personal details in the designated fields such as 'NAME (Last, First, Middle Initial)', ensuring accuracy and clarity.
-
5.Proceed to complete sections requiring your supervisor's input. This may involve checking relevant boxes and filling in their details as indicated.
-
6.Continue with the fields designated for the Information Owner, IAO, and Security Manager by entering their names and signatures as required.
-
7.Make sure to review all filled areas for accuracy and completeness before finalizing the document.
-
8.Once completed, save your changes. Utilize pdfFiller’s save options to either download your form or submit it directly via the application.
Who needs to fill out the System Authorization Access Request Form?
The form is required to be completed by DoD personnel, including requestors, supervisors, information owners, IAOs, and security managers who oversee access to DoD systems.
Are there any specific deadlines for submitting this form?
While there are no strict deadlines mentioned, it is advisable to submit the form as soon as access is needed. Allow time for approval from all required signatories.
How should I submit the completed form?
Once you have completed the form on pdfFiller, you can either download it for personal records or submit directly through the platform if your organization allows.
What supporting documents are needed with this form?
While the form itself requires no supporting documents, having identification and justification information ready is beneficial. Check with your superior for any additional documentation requirements.
What are common mistakes to avoid when filling out this form?
Common mistakes include missing signatures, entering incorrect personal details, or leaving required fields blank. Review all sections carefully before submission.
How long does it take to process this form?
Processing time can vary, dependent on each organization’s internal procedures. It is advisable to check with your supervisor for typical turnaround times.
Do I need to notarize the System Authorization Access Request Form?
No, notarization is not required for this form. Ensure all relevant parties sign the document as instructed.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.