Last updated on Apr 5, 2026

Get the free University of Colorado Hospital Computer System Security Statement
We are not affiliated with any brand or entity on this form
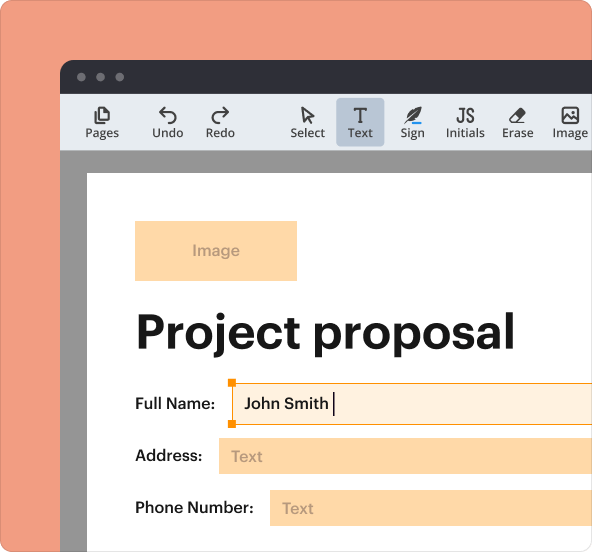
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is university of colorado hospital
The University of Colorado Hospital Computer System Security Statement is a healthcare form used by hospital employees to affirm their understanding and agreement to security policies regarding computer system access and data confidentiality.
pdfFiller scores top ratings on review platforms




Who needs university of colorado hospital?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to university of colorado hospital
What is the University of Colorado Hospital Computer System Security Statement
The University of Colorado Hospital Computer System Security Statement is a vital form designed to ensure the security and confidentiality of computer systems within the hospital setting. Its primary purpose is to inform users about the policies governing access to hospital computer systems, thereby emphasizing the importance of security in healthcare environments.
This statement reinforces the commitment to protecting sensitive information and ensures users understand their responsibilities when using hospital technology. The integrity of healthcare data is paramount, as breaches can have severe consequences for both providers and patients.
Purpose and Benefits of the University of Colorado Hospital Computer System Security Statement
The main objectives of the University of Colorado Hospital Computer System Security Statement include enhancing data security and promoting user accountability. By outlining the expectations for system access, the form helps to mitigate risks associated with unauthorized access to sensitive health data.
Both the hospital and its staff benefit from this document as it not only supports compliance with healthcare regulations but also protects sensitive information from potential breaches. This agreement reinforces the user's responsibility for maintaining data privacy and integrity, ensuring a secure environment for everyone.
Who Needs the University of Colorado Hospital Computer System Security Statement
The target audience for the University of Colorado Hospital Computer System Security Statement includes employees, contractors, and any individuals who require access to hospital computer systems. These roles encompass a wide range of positions, each potentially handling sensitive information and requiring adherence to security protocols.
Various scenarios can necessitate completing this form, such as onboarding new staff or when contractors are brought in to assist with IT services. By identifying who needs to fill out the form, the hospital ensures that all users are properly informed about their responsibilities regarding computer security.
How to Fill Out the University of Colorado Hospital Computer System Security Statement Online (Step-by-Step)
Filling out the University of Colorado Hospital Computer System Security Statement through the pdfFiller platform involves several straightforward steps:
-
Access the form on pdfFiller.
-
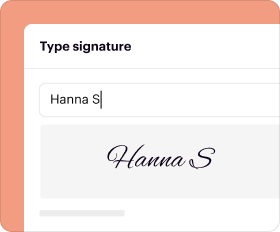
Complete the required fields, such as Name, Employer, Employee #, and Signature.
-
Review all entries for accuracy.
-
Submit the form as instructed.
To ensure compliance, users should verify each field is filled accurately and all required information is included. Following these steps carefully will help avoid submission issues and ensure a smooth form-filling process.
Field-by-Field Instructions for the University of Colorado Hospital Computer System Security Statement
This section provides detailed guidance on each field of the University of Colorado Hospital Computer System Security Statement:
-
Name: Enter your full name as it appears on official documents.
-
Employer: Specify your employer's name, including any applicable affiliations with the hospital.
-
Employee #: Ensure your employee number is correct, as this identifies you within the hospital system.
-
Signature: Sign to affirm your understanding and agreement to the security policies.
Users should avoid common pitfalls, such as leaving any fields blank or filling them in incorrectly. Carefully following these instructions increases the likelihood of a successful submission.
Review and Validation Checklist for the University of Colorado Hospital Computer System Security Statement
Before submitting the University of Colorado Hospital Computer System Security Statement, users should follow this checklist to validate their form:
-
Check that all required fields are completed.
-
Ensure your signature is present and clear.
-
Review the information for accuracy.
-
Confirm that any attachments or additional documents required are included.
Completing this checklist can prevent potential delays or issues with compliance and submission, ensuring that the form meets hospital policies. A thorough review increases the chances that the submitted document will be processed smoothly.
Submission Methods and Delivery for the University of Colorado Hospital Computer System Security Statement
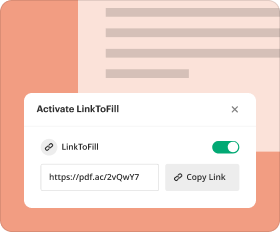
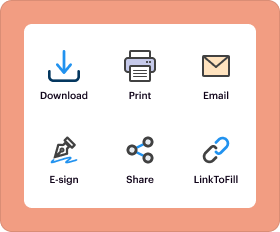
Upon completion, users can submit the University of Colorado Hospital Computer System Security Statement through various methods, including online submissions and in-person delivery at designated hospital locations. Each method has its specific procedures that users should follow to ensure proper handling of the document.
Processing times may vary depending on the submission method chosen, so users should be aware of what to expect after their form is submitted. Understanding these details can help facilitate a smooth document workflow.
Security and Compliance for the University of Colorado Hospital Computer System Security Statement
Maintaining security is crucial when handling the University of Colorado Hospital Computer System Security Statement. Users must be aware of compliance standards, such as HIPAA, that govern the handling and sharing of sensitive information. Compliance ensures that both the hospital and its users adhere to legal and best practice standards.
Additionally, pdfFiller implements robust security measures, including 256-bit encryption, to protect users' data during the form-filling process. Users can confidently complete their forms, knowing their information is secure throughout its lifecycle.
How to Correct or Amend the University of Colorado Hospital Computer System Security Statement
If errors are detected after submission of the University of Colorado Hospital Computer System Security Statement, users should follow a specific process to amend the document. This involves reaching out to the designated hospital department responsible for handling such corrections.
The steps to submit amendments may include notifying the department of the error, providing the corrected information, and potentially re-signing the document. Users are encouraged to regularly review their submissions to maintain accuracy and uphold compliance.
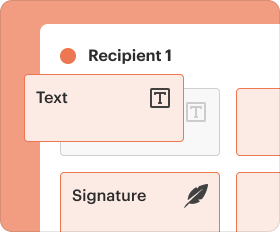
Empower Your Form-Filling Experience with pdfFiller
Users are encouraged to take advantage of pdfFiller's features for an efficient form-filling experience. The platform offers online editing, secure document management, and eSigning, allowing users to complete their tasks with ease.
With tools designed to streamline the process, pdfFiller empowers users to efficiently navigate the requirements for filling out the University of Colorado Hospital Computer System Security Statement and manage their documents securely.
How to fill out the university of colorado hospital
-
1.Start by accessing pdfFiller and searching for the University of Colorado Hospital Computer System Security Statement form.
-
2.Select the form from the search results to open it in the editor.
-
3.Review the form layout and familiarize yourself with required fields, which include Name, Employer, Employee Number, and Signature.
-
4.Before filling in the form, gather necessary information such as your employment details and unique sign-on code provided by your department.
-
5.Begin completing the fillable fields by clicking on each box. Enter your information accurately, ensuring no spelling errors.
-
6.If you encounter instructions or notes, read them carefully to understand any specific requirements related to terms of use or agreements.
-
7.Once all fields are filled, review the entire form for accuracy and completeness, checking that your signature is included.
-
8.After finalizing, save your progress by clicking the 'Save' option on pdfFiller. You can also download a copy of the completed document.
-
9.To submit the form, look for submission options provided by your hospital, or print it out and deliver it as instructed by your department.
Who needs to fill out the University of Colorado Hospital Computer System Security Statement?
All users accessing the hospital's computer systems, including staff, administrative personnel, and IT members, are required to complete and sign this form to acknowledge the security policies.
Are there any deadlines for submitting this form?
It's important to submit the University of Colorado Hospital Computer System Security Statement promptly, ideally during your onboarding process or before accessing sensitive computer systems.
How do I submit the completed form?
After filling out the form in pdfFiller, you can either download it and submit it physically or use the electronic submission options provided by your hospital's IT department.
What should I include in the supporting documents for this form?
Typically, you might need to present identification or an employee number to verify your role. Check with your administration for any specific documentation required.
What are common mistakes to avoid while filling out this form?
Ensure that all required fields are completed accurately, especially your unique sign-on code. Avoid skipping sections and double-check your signature, as incomplete forms may be rejected.
How long does it take to process this form?
Processing times for the University of Colorado Hospital Computer System Security Statement can vary, but typically it should be reviewed within a few business days after submission.
Can I edit the form once I've saved it?
Yes, in pdfFiller, you can reopen your saved form at any time to make edits before final submission. Just ensure all changes are updated before sending it.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.