
Get the free Information Security Policy Exception Request Form - University ... - usg
Show details
Information Security Policy Exception Request Form The purpose of the Information Security Policy/Standard Exception Request Form is to allow University System of Georgia system owners or their approved
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign information security policy exception
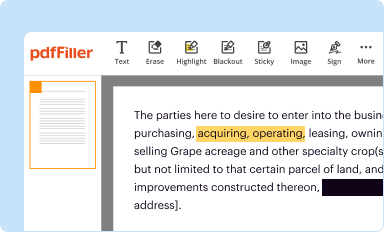
Edit your information security policy exception form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
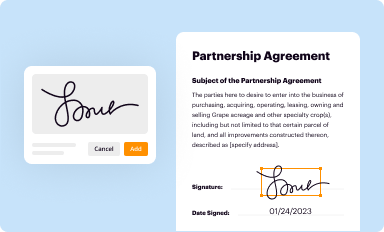
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
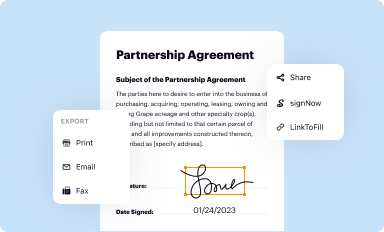
Share your form instantly
Email, fax, or share your information security policy exception form via URL. You can also download, print, or export forms to your preferred cloud storage service.
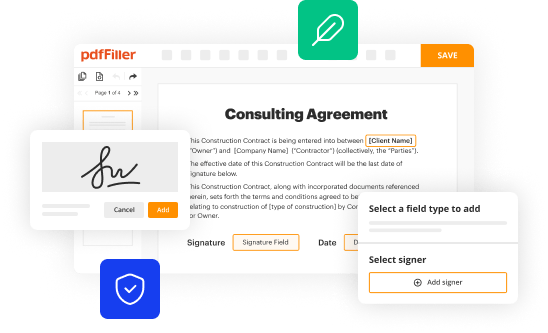
How to edit information security policy exception online
To use our professional PDF editor, follow these steps:
1
Register the account. Begin by clicking Start Free Trial and create a profile if you are a new user.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit information security policy exception. Replace text, adding objects, rearranging pages, and more. Then select the Documents tab to combine, divide, lock or unlock the file.
4
Save your file. Choose it from the list of records. Then, shift the pointer to the right toolbar and select one of the several exporting methods: save it in multiple formats, download it as a PDF, email it, or save it to the cloud.
Dealing with documents is simple using pdfFiller.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out information security policy exception
How to fill out information security policy exception:
01
Obtain the necessary forms: Contact the appropriate department or team responsible for managing information security policies and request the forms required to fill out an exception.
02
Understand the policy: Review the information security policy thoroughly to understand the specific requirements and guidelines that need to be followed. This will help in determining if an exception is truly necessary.
03
Identify the reason for the exception: Clearly articulate the reason for needing an exception to the information security policy. This could be due to technical limitations, business needs, or any other justifiable reason. It is important to provide a detailed explanation to support the exception request.
04
Gather supporting evidence: Collect any relevant documentation or evidence that supports the need for the exception. This could include technical specifications, risk assessments, cost-benefit analysis, or any other relevant information that strengthens the case for the exception.
05
Consult with experts: If needed, consult with experts or professionals who are knowledgeable about information security policies to ensure that the exception request is appropriately framed and supported.
06
Submit the request: Complete the exception request form accurately and provide all the necessary information, documentation, and justifications. Make sure to follow any specific instructions provided by the department or team responsible for processing exception requests.
Who needs information security policy exception:
01
Individuals or teams facing technical limitations: If certain technical constraints prevent the strict adherence to the information security policy, an exception may be needed. This could include cases where implementing a security measure would interfere with critical functionality or result in significant technical hurdles.
02
Business units with specific needs: In some instances, certain business requirements may justify the need for an exception. For example, if a particular process or system is essential for the smooth functioning of the organization but fails to comply with a specific security requirement, an exception might be necessary.
03
Unique circumstances: Occasionally, exceptional circumstances may arise that necessitate an exception to the information security policy. These could include emergencies, unforeseen events, or situations where strict adherence to the policy would cause more harm than good.
It is crucial to note that the granting of an information security policy exception is typically subject to review and approval by the appropriate authority or governing body responsible for overseeing the organization's information security practices.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I modify information security policy exception without leaving Google Drive?
By combining pdfFiller with Google Docs, you can generate fillable forms directly in Google Drive. No need to leave Google Drive to make edits or sign documents, including information security policy exception. Use pdfFiller's features in Google Drive to handle documents on any internet-connected device.
How do I make changes in information security policy exception?
pdfFiller allows you to edit not only the content of your files, but also the quantity and sequence of the pages. Upload your information security policy exception to the editor and make adjustments in a matter of seconds. Text in PDFs may be blacked out, typed in, and erased using the editor. You may also include photos, sticky notes, and text boxes, among other things.
How do I make edits in information security policy exception without leaving Chrome?
information security policy exception can be edited, filled out, and signed with the pdfFiller Google Chrome Extension. You can open the editor right from a Google search page with just one click. Fillable documents can be done on any web-connected device without leaving Chrome.
What is information security policy exception?
An information security policy exception is a formal request to deviate from established information security policies and procedures, usually due to specific circumstances that prevent compliance.
Who is required to file information security policy exception?
Any employee or department that cannot comply with existing information security policies must file an information security policy exception to seek approval for non-compliance.
How to fill out information security policy exception?
To fill out an information security policy exception, you need to provide details such as the specific policy being violated, the reason for the exception, duration of the exception, and any mitigating controls in place to manage the risk.
What is the purpose of information security policy exception?
The purpose of an information security policy exception is to allow flexibility in compliance while ensuring that risks are understood, managed, and documented to maintain overall security.
What information must be reported on information security policy exception?
The information that must be reported includes the nature of the exception, justification for the exception, effects on security posture, duration of the exception, and any risk management strategies implemented.
Fill out your information security policy exception online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Information Security Policy Exception is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.





















