Last updated on Apr 5, 2026

Get the free State Monitoring Protocol
We are not affiliated with any brand or entity on this form
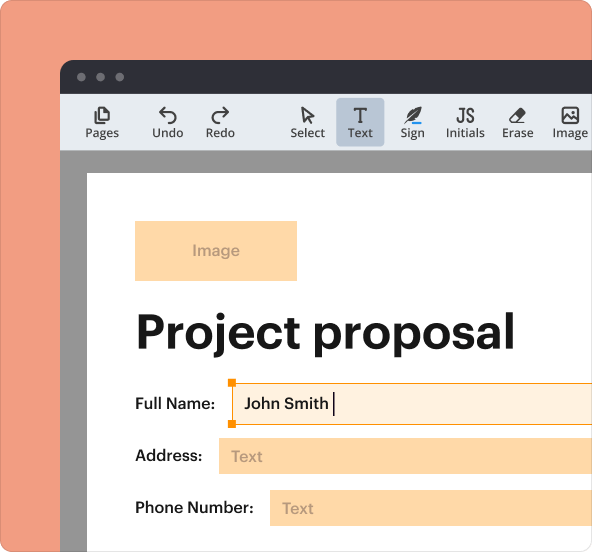
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is state monitoring protocol
The State Monitoring Protocol is a government form used by state and department representatives to monitor the allocation and application procedures for the State Fiscal Stabilization Fund Program.
pdfFiller scores top ratings on review platforms




Who needs state monitoring protocol?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to state monitoring protocol
What is the State Monitoring Protocol?
The State Monitoring Protocol serves as a vital framework within the education funding system, focusing on the allocation and application procedures for the State Fiscal Stabilization Fund Program. This comprehensive protocol is designed to ensure transparency and compliance among key stakeholders, including state representatives, department officials, local educational agencies (LEAs), and public institutions of higher education (IHEs).
This protocol not only defines the standards set forth for monitoring but also emphasizes the importance of accurate allocation of education stabilization funds. By facilitating thorough reviews of funding applications, the protocol plays an essential role in reinforcing the integrity of the education funding review process.
Purpose and Benefits of the State Monitoring Protocol
The primary purpose of the State Monitoring Protocol is to uphold compliance with statutory requirements, thus safeguarding the interests of stakeholders involved in education funding. For state and department representatives, the protocol streamlines the process of reviewing applications for state funding allocation, saving time and resources.
Public IHEs particularly benefit from this protocol as it ensures equitable distribution of educational resources. By adhering to the established guidelines, stakeholders can effectively contribute to a more structured and accountable funding allocation framework.
Key Features of the State Monitoring Protocol Form
The State Monitoring Protocol form is equipped with various essential features that enhance its effectiveness. These include:
-
Fillable fields that allow users to input relevant data seamlessly.
-
Guiding questions aimed at aiding users in completing the form accurately.
-
Sections dedicated to evidence and documentation to support compliance efforts.
-
A user-friendly format that ensures accessibility for all stakeholders.
These features collectively guarantee thoroughness and adherence to compliance standards, making the form an important tool in the education funding process.
Who Needs to Use the State Monitoring Protocol?
The primary users of the State Monitoring Protocol encompass a diverse group of stakeholders. Key participants include:
-
State representatives responsible for oversight of funding allocations.
-
Department representatives who facilitate the application review process.
-
Local educational agencies (LEAs) that submit applications for funding.
-
Public institutions of higher education (IHEs) that receive allocated funds.
These stakeholders play a crucial role in ensuring that the protocol is utilized effectively across various applications.
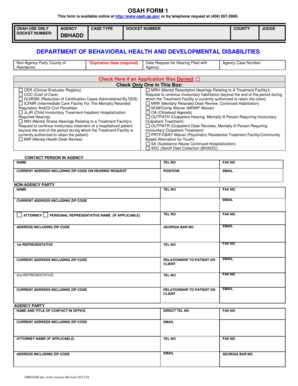
How to Fill Out the State Monitoring Protocol Online
Completing the State Monitoring Protocol online requires careful preparation. Begin with a pre-filing checklist that includes the following:
-
Gather all necessary information and documents required for submission.
-
Follow detailed, field-by-field instructions to ensure accuracy.
-
Be mindful of common errors to avoid pitfalls during completion.
This structured approach guarantees a smooth process and minimizes any potential delays in application review.
Submission Methods for the State Monitoring Protocol
Upon completion, the State Monitoring Protocol can be submitted through various methods. The options include:
-
Online submission via official state agency portals.
-
Mailing the completed form to designated educational departments.
Users should be aware of any associated fees, submission deadlines, and processing times to ensure a timely and successful application experience.
What Happens After You Submit the State Monitoring Protocol?
After submitting the State Monitoring Protocol, users can expect a confirmation process, which facilitates tracking the status of their application. It's important to be aware of common reasons for application rejection, such as incomplete information. Understanding these factors can help in preparing a stronger application in the future.
Additionally, if amendments or corrections are necessary post-submission, users can follow outlined procedures to rectify any issues effectively.
Security and Compliance Considerations
Users can rest assured that the State Monitoring Protocol adheres to stringent security measures. Document security is reinforced through features such as encryption and compliance with relevant legal standards. Protecting user privacy and data during submission is paramount, ensuring that sensitive documents remain confidential throughout the process.
Furthermore, there are clear record retention requirements regarding submitted documents, which further bolster security and compliance assurance.
Completing the Process with pdfFiller
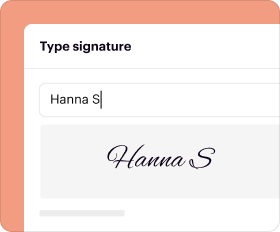
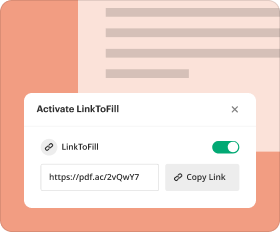
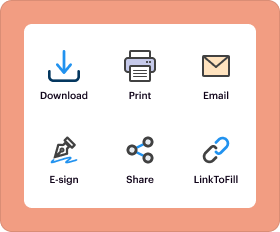
Utilizing pdfFiller facilitates an enhanced experience when filling out the State Monitoring Protocol. Users can benefit from features that allow for easy editing, filling, and signing of the form.
Moreover, pdfFiller ensures document security and compliance, providing peace of mind when handling sensitive information. Users are encouraged to start their filling process online to take advantage of these capabilities.
How to fill out the state monitoring protocol
-
1.To access the State Monitoring Protocol form, go to pdfFiller and use the search bar to locate the form by name.
-
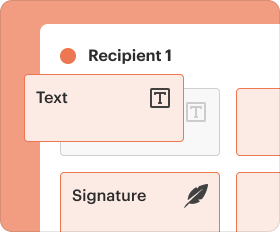
2.Once you open the form, use the drag-and-drop feature to add text and fillable fields, allowing easy navigation throughout the document.
-
3.Before beginning, gather the necessary information such as LEA application details and evidence for compliance to streamline the filling process.
-
4.Navigate through each section by clicking on the fields to complete them; use the guiding questions to ensure all information is relevant and complete.
-
5.Special attention should be given to the evidence/documentation sections; scan or upload required documents directly to pdfFiller.
-
6.After filling in all relevant sections, review the entire form carefully for any omissions or errors; ensure that all evidence is attached.
-
7.Finalizing the form can be done by saving it in pdfFiller or choosing to download it in your preferred format.
-
8.When you're ready to submit, check if there are specific submission methods indicated in your guidelines, following them closely.
Who is eligible to use the State Monitoring Protocol?
Eligibility to use the State Monitoring Protocol typically includes state education officials, department representatives, and LEAs who are involved in the allocation process of the State Fiscal Stabilization Fund.
What supporting documents are required for this form?
Supporting documents include evidence detailing LEA applications, fiscal allocations, and compliance documentation. It is important to ensure that all evidence aligns with the form's guiding questions.
How do I submit the completed State Monitoring Protocol?
Submitting the completed form can often be done online, but check specific guidelines related to submissions through pdfFiller or your state education department’s portal for precise instructions.
What common mistakes should I avoid while filling out this form?
Common mistakes include missing required fields, not providing sufficient evidence, or failing to adhere to the guiding questions. Double-checking for completeness can help prevent these errors.
Are there any deadlines I should be aware of?
Typically, there are deadlines associated with fund allocations and annual reporting. Always check with your state department for specific timelines related to the State Monitoring Protocol.
How long does processing take after submission?
Processing times for the State Monitoring Protocol can vary widely based on the state’s review process. It's advisable to reach out directly to your state department for estimated time frames.
Is notarization required for this form?
No, notarization is not required for the State Monitoring Protocol form, simplifying the submission process for eligible users.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.