Get the free Ohio OAKS User Security Access Request Form
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is ohio oaks user security
The Ohio OAKS User Security Access Request Form is a government document used by State of Ohio employees and agency authorities to request or modify security access within the OAKS Human Capital Management system.
pdfFiller scores top ratings on review platforms




Who needs ohio oaks user security?
Explore how professionals across industries use pdfFiller.
How to fill out the ohio oaks user security
-
1.To complete the Ohio OAKS User Security Access Request Form on pdfFiller, start by accessing the pdfFiller website and search for the form using its name.
-
2.Once located, click on the form to open it in the pdfFiller editor. This will allow you to view it in an interactive format.
-
3.Before filling out the form, gather all necessary information such as the employee's name, work telephone number, desired access roles, and signatures from both the employee and the agency authority.
-
4.Begin filling the form by entering the ‘Employee Name’ and ‘Work Telephone Number’ in the designated fields. Make sure all information is accurate and complete.
-
5.Next, identify the role access required by using the checkboxes for the roles available in the form. Ensure that the choices align with the needed access within the OAKS system.
-
6.Locate the signature section of the form. The employee must sign in the designated area, and the agency appointing authority or designee should also provide their signature.
-
7.Review all entries on the form for accuracy, ensuring no fields are left blank unless specified. This helps avoid delays in processing.
-
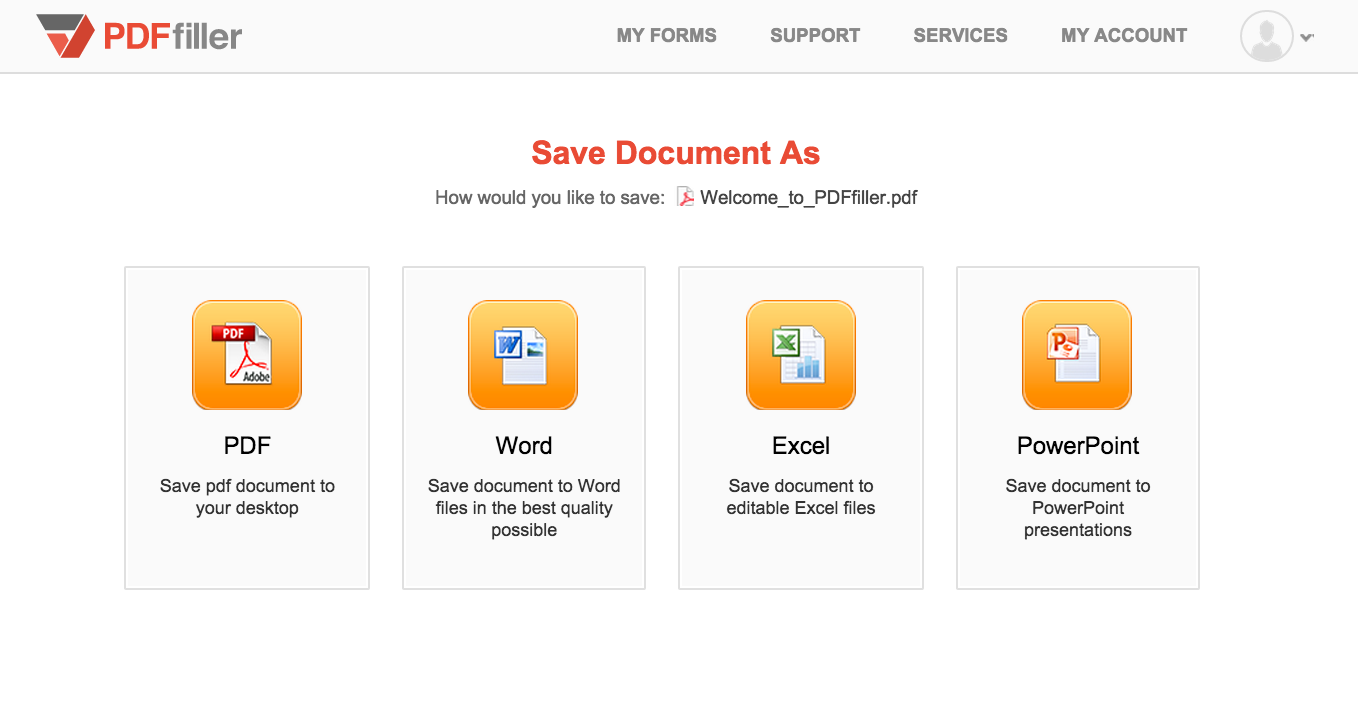
8.Once you are satisfied, navigate to the save options on pdfFiller. From here, you can select to save the form, download it for any necessary physical submission, or choose to submit it directly if that option is available.

Who is eligible to fill out the Ohio OAKS User Security Access Request Form?
The form must be completed by State of Ohio employees requiring access and their agency appointing authorities or designees who need to approve the request.
What are the submission methods for this form?
The completed Ohio OAKS User Security Access Request Form can be submitted electronically through designated channels or printed out for physical submission to the appropriate agency authority.
What information do I need to have before starting this form?
Before starting, ensure you have the employee’s name, work telephone number, required roles for access, and access to both signatures from the employee and agency authority.
Are there any common mistakes to avoid when filling out this form?
Common mistakes include leaving required fields blank, incorrect signature placement, and not double-checking that all necessary approvals are gathered before submission.
What is the processing time for this form?
Processing times can vary, but typically you should allow several business days for the security access request to be reviewed and approved by the respective agency personnel.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.