Last updated on May 8, 2026
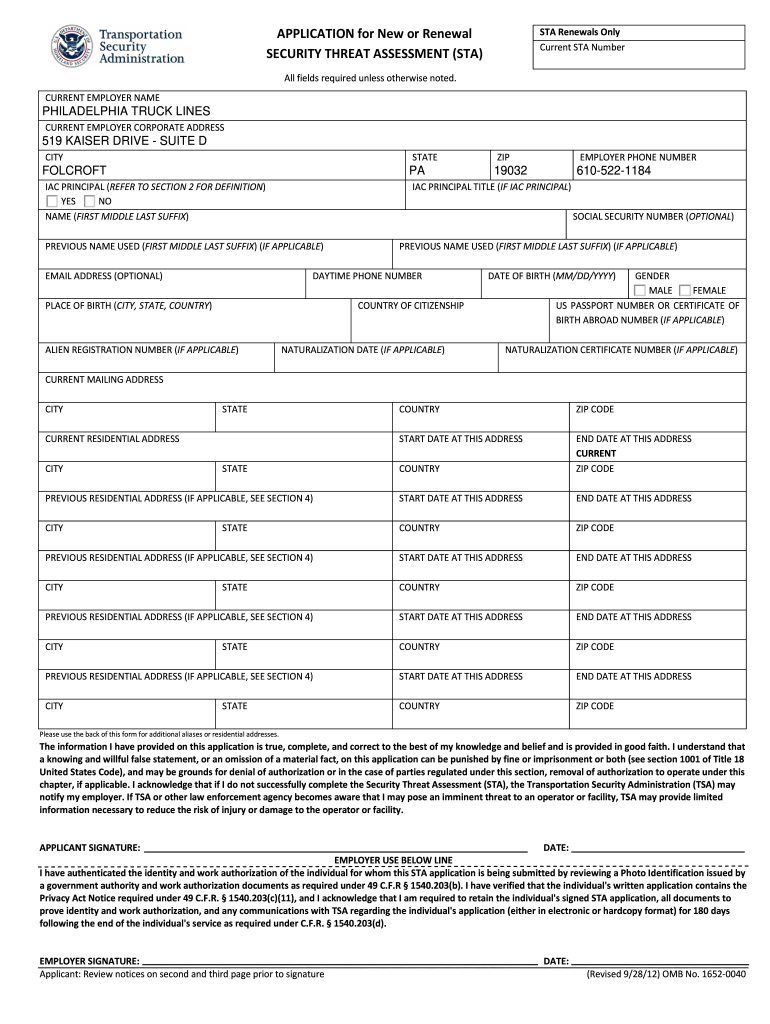
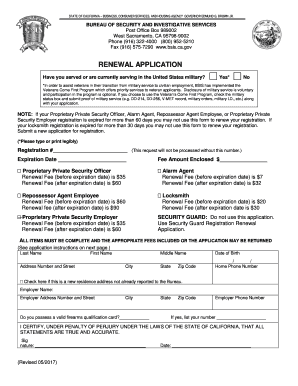
TSA 419F 2012 free printable template
pdfFiller is not affiliated with any government organization
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
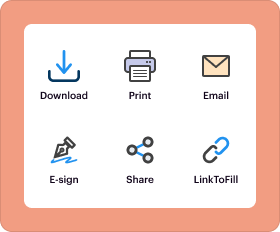
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.
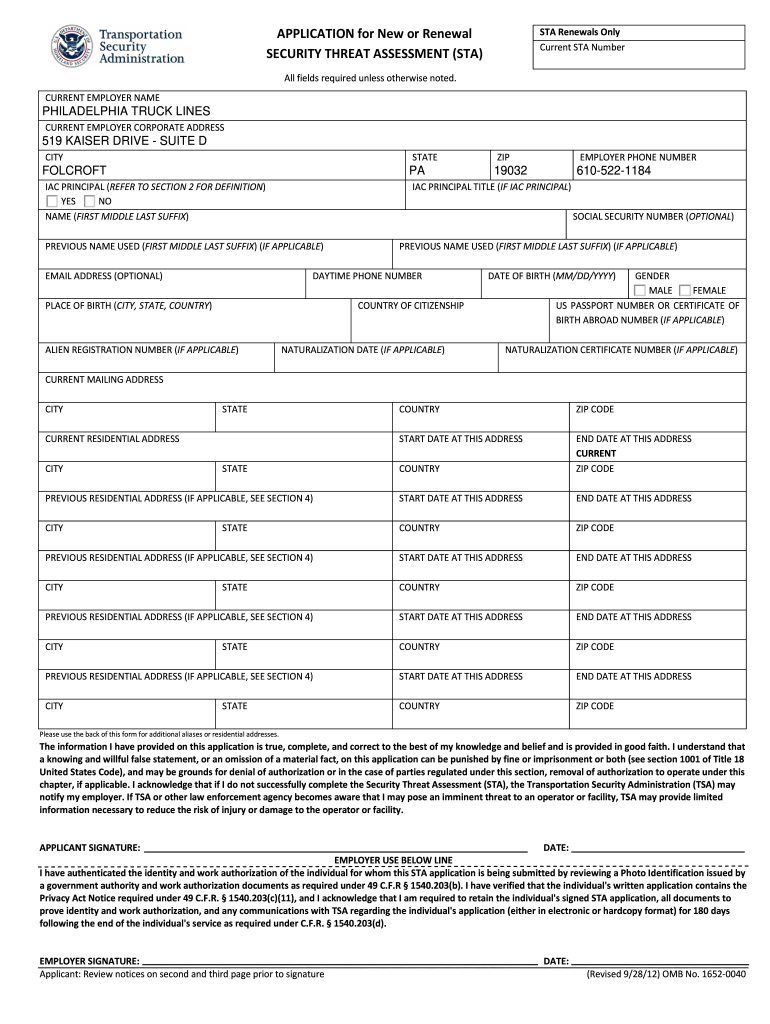
What is TSA 419F
The Security Threat Assessment Application is a government form used by applicants and employers to assess security threats for unescorted access to air cargo.
pdfFiller scores top ratings on review platforms




Who needs TSA 419F?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to TSA 419F
Understanding the Security Threat Assessment Application
The Security Threat Assessment Application is a critical document that aligns with TSA regulations to ensure secure access to air cargo. Designed to assess potential security threats, this application serves a pivotal role in aviation security. It is essential for those seeking unescorted access to air cargo and must be filled out with precision.
Individuals and organizations utilizing this form include airport personnel and employers who require the assessment for their employees. Accurate completion of the form is vital to avoid delays or complications in the approval process.
Benefits of the Security Threat Assessment Application
Using the Security Threat Assessment Application offers several advantages for both applicants and employers. One significant benefit is the ability to gain unescorted access to air cargo facilities, which streamlines operations for companies involved in air transport.
Furthermore, compliance with TSA regulations is imperative for maintaining operational legality. The application also enhances job security for employees by ensuring that they meet the necessary background checks and qualifications for their roles.
Who Should Complete the Security Threat Assessment Application?
The Security Threat Assessment Application should be completed by individuals who require authorization to access air cargo. Employers also play a vital role in this process, as they must verify the qualifications of their employees seeking access.
Understanding the responsibilities of both applicants and employers in the submission process ensures that all necessary information is provided, facilitating a smoother assessment outcome.
Eligibility Criteria for the Security Threat Assessment Application
To successfully complete the Security Threat Assessment Application, applicants must meet specific eligibility criteria. These requirements include providing personal information, such as name and social security number, and ensuring employment verification from their employer.
Moreover, applicants must satisfy citizenship and residency conditions, which are crucial to determine suitability for air cargo access.
Step-by-Step Guide to Completing the Security Threat Assessment Application
Completing the Security Threat Assessment Application online involves a clear and structured approach. First, it’s essential to have access to online tools like pdfFiller, which simplifies the editing and submission process.
-
Access the Security Threat Assessment Application form via pdfFiller.
-
Fill out each field carefully, noting required and optional sections.
-
Avoid common pitfalls, such as forgetting to sign or providing incorrect information.
How to Submit the Security Threat Assessment Application
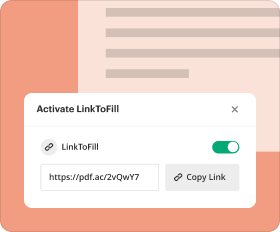
Once the Security Threat Assessment Application is completed, it is important to submit it correctly. There are various submission methods available, including online options and traditional mail.
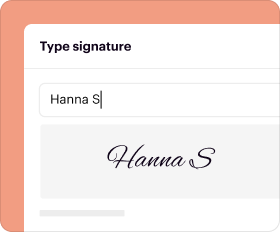
Both applicants and employers are required to provide signatures on the form, affirming the authenticity of the information provided. Late submissions can lead to penalties, making timely submission vital.
Processing and Tracking Your Security Threat Assessment Application
After submission, applicants can expect certain processing timelines for the Security Threat Assessment. Tracking the status of the application is feasible, allowing applicants to stay informed on their assessment status.
Common outcomes include approval or rejection, with potential steps outlined for either scenario, helping applicants to be prepared for any eventuality.
Security and Compliance for the Security Threat Assessment Process
Maintaining security throughout the application process is essential, especially when handling sensitive personal information. Utilizing services like pdfFiller ensures a secure experience, bolstered by features such as 256-bit encryption.
Compliance with regulatory standards, including HIPAA and GDPR, is also a significant consideration during the application process, ensuring that data protection best practices are followed.
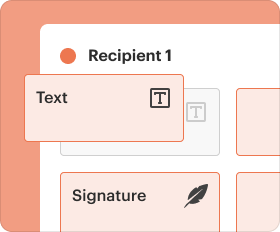
Using pdfFiller to Complete the Security Threat Assessment Application
pdfFiller offers numerous benefits for filling out the Security Threat Assessment Application efficiently. By leveraging pdfFiller’s editing and signing tools, applicants can streamline their form completion process significantly.
Accessing the Security Threat Assessment Application is straightforward on pdfFiller's platform. Many users have successfully navigated the application process using these services, making it a reliable choice for applicants.
Final Thoughts on the Security Threat Assessment Application
Understanding the components of the Security Threat Assessment Application is key to ensuring a smooth process. Utilizing resources like pdfFiller can enhance user confidence throughout the application journey.
Exploring additional tools and resources on pdfFiller may further assist applicants in fulfilling their security assessment needs effectively.
How to fill out the TSA 419F
-
1.Access the Security Threat Assessment Application on pdfFiller by searching for the form in the document library or using a direct link provided by your employer.
-
2.Open the form in pdfFiller's editing interface to view the various fields and instructions required for completion.
-
3.Before starting, gather necessary information such as your full name, address, social security number, citizenship details, and employment verification from your employer.
-
4.Begin filling out the form by entering your personal information in the designated fields. Ensure that all required fields are completed, as indicated by asterisks or notes in the form.
-
5.Use the checkboxes provided to indicate your consent and understanding of the form's terms, following the on-screen instructions carefully.
-
6.After completing all sections, thoroughly review your entries for accuracy, ensuring that all information aligns with supporting documents and requirements.
-
7.Once you've confirmed the information is correct, save the form to your pdfFiller account or download it for submission. You can also opt to submit the completed form directly through pdfFiller if applicable.
Who is eligible to apply for the Security Threat Assessment?
The Security Threat Assessment Application is available to individuals seeking unescorted access to air cargo, requiring verification from their employers. Eligibility includes providing necessary personal identification and employment details.
What is the deadline for submitting the Security Threat Assessment Application?
While specific deadlines can vary, applicants should submit the form as soon as possible prior to needing unescorted access to ensure timely processing. Check TSA guidelines for any specific deadlines.
How do I submit the completed form?
After filling out the Security Threat Assessment Application in pdfFiller, you can submit it directly through the platform or download it for mailing or electronic submission to TSA. Follow the specified submission guidelines on the form.
What supporting documents are required?
Supporting documents typically include proof of identity, citizenship verification, and any employment-related materials necessary for verification. Make sure to refer to TSA requirements for complete details.
What are common mistakes to avoid when filling out the form?
Avoid incomplete sections, mismatched information between the form and supporting documents, and ignoring any specific instructions indicated in the application. Always double-check your entries for clarity and accuracy.
What is the processing time for the Security Threat Assessment Application?
Processing times can vary based on volume and individual circumstances, but applicants should allow several weeks for their applications to be reviewed. Check with TSA for any updates on current processing times.
Is notarization required for the Security Threat Assessment Application?
No, notarization is not required for the Security Threat Assessment Application; however, both the applicant and employer must sign the form to verify the information provided.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.