Get the free keys log
Get, Create, Make and Sign keys log



How to edit keys log online
Uncompromising security for your PDF editing and eSignature needs
How to fill out keys log

To fill out a keys log, follow these steps:
Who needs keys log?
Instructions and Help about keys log
Thanks to audible for keeping legal eagle in the air oh my gosh I have so much work to do today well let me read one more article by the mainstream media fake news before I get started testimony torpedoes Republican defenses of Trump's defenses are almost entirely gone Trump has no defense after sun land testimony that can't be right can it Music hey legal eagles it's time to think like a lawyer because Republican and Democratic positions on this whole impeachment hearing have been changing over time and I think it's worthwhile going over the Republican impeachment defenses to see if they hold any legal water quick disclaimer of course the facts are fluid, and they are changing multiple witnesses are testifying every week so some factual issues here that I'm going to discuss I'm sure are going to change, but I wanted to take some time to focus on some of the legal issues that are implicated by these impeachment hearings I'm going to try to do my best to steal man these arguments in other words I'm going to try to give the Republican defenses in the best light possible to avoid attacking trauma and dealing with the best possible version of those particular defenses some of these defenses are better than others it's a bit of a moving target though because different Republicans have focused on different defenses there isn't exactly a unified front on this but that being said let's dig into the main defenses that the Republicans are using in this impeachment inquiry, so the first impeachment defense probably boils down to no quid pro quo or in other words the call was perfect there's a rumor out they want the first conversation it was beautiful it was just a perfect conversation this is largely the preferred defense of President Trump and that he tends to tweet this out with some frequency this also appeared to be the early favored defense of the Republicans that has largely evaporated you still see it a little but it's not the favored defense at the time the argument is that as a factual matter there was no quid pro quo between the United States and Ukraine I didn't do it there was no quid pro quo senators and all of these other people have actually done what they're accusing me of doing which I didn't do as the president often tweets and says and public read the transcript whether you believe that the transcript is sufficient to show a quid pro quo evidencing solicitation of a bribe or whether you believe that the transcript demonstrates that the call was in fact perfect as the president says is a factual matter for you to decide in a variation of this argument was used in the questioning of lieutenant-colonel VIN Minh by representative Radcliffe who pointed out that no witness in the depositions as part of the impeachment inquiry had ever used the word bribery in an impeachment inquiry that the Speaker of the House says is all about bribery where bribery is the impeachable offense no witness has used the word bribery to describe president...






People Also Ask about
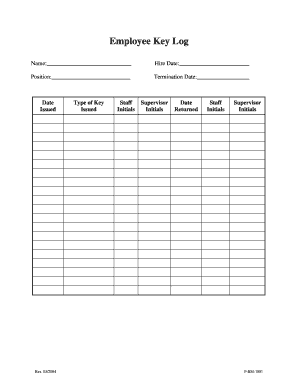
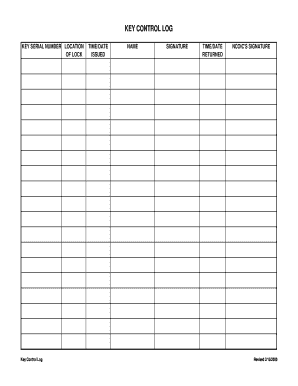
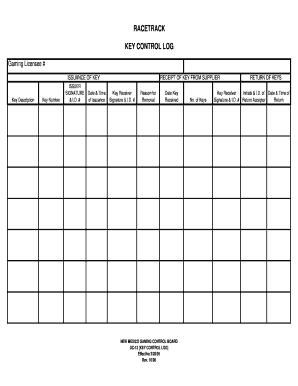
How do you create a key log?
What are the key control procedures?
For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I modify my keys log in Gmail?
Can I create an electronic signature for signing my keys log in Gmail?
Can I edit keys log on an iOS device?
What is keys log?
Who is required to file keys log?
How to fill out keys log?
What is the purpose of keys log?
What information must be reported on keys log?
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.