Last updated on Apr 6, 2026

Get the free HIPAA PHI De-Identification Checklist
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
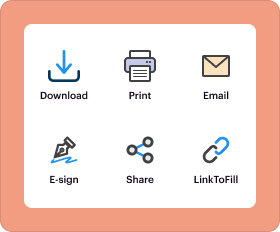
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

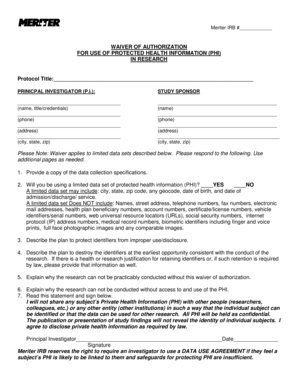
What is hipaa phi de-identification checklist
The HIPAA PHI De-Identification Checklist is a healthcare form used by organizations to ensure the removal of specific identifiers from protected health information (PHI) to comply with HIPAA regulations.
pdfFiller scores top ratings on review platforms




Who needs hipaa phi de-identification checklist?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to hipaa phi de-identification checklist
What is the HIPAA PHI De-Identification Checklist?
The HIPAA PHI De-Identification Checklist is a crucial tool designed to assist organizations in achieving compliance with HIPAA regulations. The checklist serves to ensure the removal of specific identifiers from protected health information (PHI), thereby safeguarding patient privacy. De-identifying PHI is essential in healthcare to protect individuals' sensitive data while allowing for data use in research and analysis.
As healthcare providers and organizations handle vast amounts of patient information, the importance of adhering to HIPAA standards cannot be overstated. The checklist functions as a structured guide, streamlining the compliance process for entities managing PHI.
Purpose and Benefits of the HIPAA PHI De-Identification Checklist
The primary purpose of the HIPAA PHI De-Identification Checklist is to support healthcare providers in implementing effective measures for safeguarding patient information. By following this checklist, organizations can ensure they adhere to legal requirements and avoid the penalties associated with non-compliance.
This checklist not only helps in the de-identification process but also promotes trust between healthcare providers and patients. Victims of data breaches may face significant legal repercussions, making compliance a top priority.
Key Features of the HIPAA PHI De-Identification Checklist
The checklist includes 18 specific identifiers that must be meticulously removed to comply with HIPAA regulations. These identifiers range from names and geographic subdivisions to dates and unique identifying numbers.
Structured for user-friendliness, the checklist features checkboxes that enhance the de-identification process. This layout allows users to easily verify the completion of each step, facilitating a straightforward approach to handling sensitive data.
Who Needs the HIPAA PHI De-Identification Checklist?
This HIPAA compliance checklist is essential for a variety of users, including healthcare providers, organizations, and any stakeholders handling PHI. It is vital for all entities to maintain compliance with HIPAA, thereby protecting patient confidentiality and ensuring appropriate data management.
Regardless of size or type, any organization that deals with PHI must utilize this checklist to navigate the complexities of compliance and safeguard well-being.
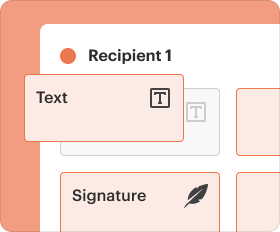
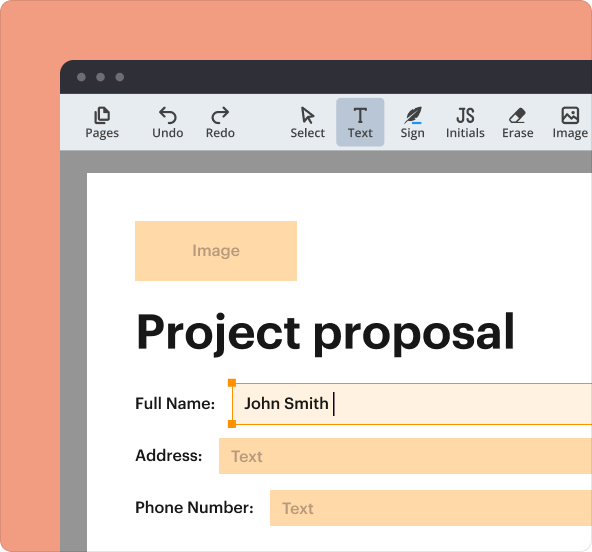
How to Fill Out the HIPAA PHI De-Identification Checklist Online
To effectively fill out the HIPAA PHI De-Identification Checklist online using pdfFiller, follow these steps:
-
Open the pdfFiller interface and select the HIPAA checklist form.
-
Fill in the required fields by checking off each identifier removed from the PHI.
-
Ensure accuracy in each section to guarantee compliance with HIPAA.
-
Review the form for any errors or omissions before finalizing.
Users should pay extra attention when completing each section to maintain compliance with security standards.
Common Errors and How to Avoid Them
When filling out the checklist, users often make several common errors that can compromise compliance. Here are practical tips to ensure accuracy:
-
Double-check all identifiers to confirm they are appropriately removed.
-
Ensure that all relevant sections of the form are filled out completely.
-
Avoid assumptions; verify each entry to maintain compliance.
By paying close attention to detail, users can avoid pitfalls that lead to non-compliance.
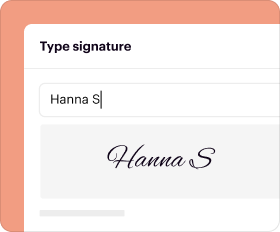
How to Sign and Submit the HIPAA PHI De-Identification Checklist
Signature requirements for submitting the HIPAA PHI De-Identification Checklist include options for both digital and wet signatures. Depending on organizational policies, users may utilize either method.
Upon completion and signature, the checklist can be submitted through designated channels specified by the healthcare provider. After submission, organizations should monitor the status of their compliance and any expected outcomes.
Security and Compliance Considerations for the HIPAA PHI De-Identification Checklist
When handling PHI, implementing robust security measures is paramount. Healthcare providers must ensure that the methods used for data de-identification meet HIPAA standards.
pdfFiller offers specific measures for protecting sensitive data, including compliance with HIPAA through 256-bit encryption and adherence to SOC 2 Type II requirements. These features help maintain the confidentiality and integrity of patient information during the de-identification process.
Next Steps After Completing the HIPAA PHI De-Identification Checklist
After completing the HIPAA PHI De-Identification Checklist, organizations must undertake follow-up actions to ensure compliance is maintained. These include tracking submissions and understanding any outcomes from the de-identification process.
Staying vigilant post-submission allows organizations to address any compliance issues proactively and reinforces their commitment to patient data security.
Maximize Your HIPAA Compliance with pdfFiller
Using pdfFiller empowers users to streamline the process of filling out the HIPAA PHI De-Identification Checklist, ensuring efficient management of sensitive documents. The platform’s capabilities support healthcare entities in achieving compliance while maintaining robust security protocols.
Embracing digital tools not only simplifies the completion process but also reinforces organizational commitment to patient privacy and legal requirements.
How to fill out the hipaa phi de-identification checklist
-
1.Access pdfFiller and search for the HIPAA PHI De-Identification Checklist template. Click on the form to open it in the editor.
-
2.Once the form is open, familiarize yourself with the fields you need to fill out. Use the navigation tools to move through the checklist.
-
3.Before filling out the form, gather your necessary information, including a list of identifiers that need to be removed, such as names, dates, and locations.
-
4.Begin completing the checklist by marking each identifier as removed or not applicable using the checkboxes provided within pdfFiller.
-
5.Carefully read the de-identification instructions included in the form to ensure you understand the requirements for each identifier.
-
6.Once you’ve marked the checkboxes, review your entries for accuracy. Ensure that all required items have been addressed.
-
7.Finalizing the form can be done once all fields are completed. Review the checklist again to confirm no identifiers were missed.
-
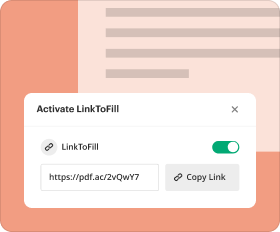
8.To save your completed form, click on the save option. You can choose to download it for your records or submit it online as instructed.
Who is eligible to use the HIPAA PHI De-Identification Checklist?
Any healthcare providers, organizations handling PHI, and personnel responsible for data compliance can use this checklist to ensure HIPAA compliance.
Are there deadlines for using the HIPAA PHI De-Identification Checklist?
While there are no strict deadlines for submitting this checklist, it should be completed prior to using or sharing any de-identified data to comply with HIPAA regulations.
How can I submit the HIPAA PHI De-Identification Checklist?
You can submit the completed checklist electronically through pdfFiller or print it out and provide a hard copy to relevant authorities as required.
What supporting documents do I need for the checklist?
You will need to reference previous documents containing PHI that require de-identification. No additional supporting documents are specifically required.
What common mistakes should I avoid when using this checklist?
Be cautious not to miss any identifiers that need to be removed. Ensure that all required sections are filled out completely to avoid compliance issues.
How long does it take to process the HIPAA PHI De-Identification Checklist?
The processing time typically depends on the specific organization’s review policies and procedures. Ensure you complete it as soon as possible to facilitate timely data use.
What should I do if I have specific concerns about the form?
If you have specific concerns, consult your organization’s compliance officer or legal counsel familiar with HIPAA regulations for guidance.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.