Last updated on Apr 10, 2026

Get the free Security Checklist Form
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is security checklist form
The Security Checklist Form is a type of document used by government agencies to conduct security inspections of work areas.
pdfFiller scores top ratings on review platforms




Who needs security checklist form?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to security checklist form
What is the Security Checklist Form?
The Security Checklist Form is a vital tool used in conducting security inspections, ensuring that work areas adhere to safety standards. This government security form, prescribed by the GSA/ISOO, serves a specific purpose by outlining necessary checks that need to be performed in various environments.
Purpose and Benefits of Using the Security Checklist Form
Organizations utilize the Security Checklist Form for work area inspections, aimed at identifying potential security issues before they escalate. By implementing this security inspection template, companies can enhance their security measures while ensuring compliance with established regulations.
-
Increased security awareness among employees.
-
Compliance with industry-specific regulations.
-
Thorough assessment of current security practices.
Key Features of the Security Checklist Form
This security checklist form contains several key components designed to facilitate effective inspections. It includes checkboxes and fields that require input, allowing for thorough documentation of security features.
-
Checkboxes for items like locked containers and security alarms.
-
Fields for comments and additional observations.
-
Sections dedicated to specific security protocols.
Who Should Use the Security Checklist Form?
The Security Checklist Form is beneficial for various roles across organizations, including government agencies and private businesses. By utilizing this form, individuals can uphold workplace safety and security standards effectively.
-
Government agencies tasked with security oversight.
-
Private sector businesses conducting regular inspections.
-
Facility managers responsible for maintaining security protocols.
How to Fill Out the Security Checklist Form Online (Step-by-Step)
Filling out the Security Checklist Form online using pdfFiller is a straightforward process. Follow these steps for an efficient experience:
-
Access the Security Checklist Form on pdfFiller’s platform.
-
Fill in the required fields with accurate information.
-
Check applicable items in the checklist to ensure nothing is overlooked.
-
Review the completed form for any errors or omissions.
-
Save your changes and prepare for submission.
Common Errors to Avoid While Filling Out the Security Checklist Form
When completing the Security Checklist Form, users often make common mistakes that can lead to inaccuracies. To prevent these issues, consider the following tips:
-
Ensure all required fields are completed.
-
Double-check checkbox items to confirm they are accurately marked.
-
Review your entries for typos before submitting.
How to Submit the Security Checklist Form
The submission process for the Security Checklist Form is simple yet crucial for compliance. Users should follow these guidelines:
-
Submit the completed form through the designated channel specified by your organization.
-
Keep a copy for your records and as proof of submission.
-
Utilize tracking options if available to confirm receipt.
Benefits of Using pdfFiller for Your Security Checklist Form
Using pdfFiller to manage your Security Checklist Form enhances the overall efficiency of the form-filling process. Key features of pdfFiller that streamline this process include:
-
eSigning capability for quick approvals.
-
Document editing tools allowing for quick amendments.
-
Secure handling of sensitive information to protect user data.
Security and Compliance Considerations for the Security Checklist Form
Data protection is paramount when filling out the Security Checklist Form. Compliance with regulations such as HIPAA and GDPR is crucial in safeguarding user information. pdfFiller employs robust security features that ensure the safety of your submitted data.
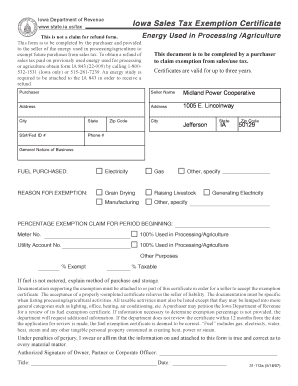
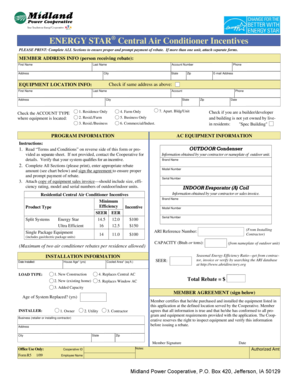
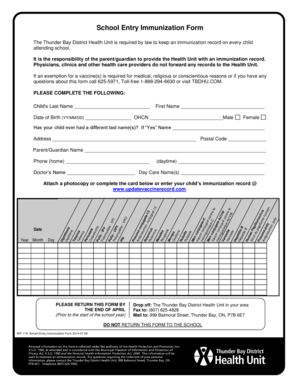
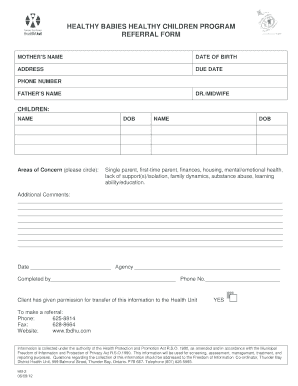
Visual Guide: Sample or Example of a Completed Security Checklist Form
Providing a visualization of a filled-out Security Checklist Form can greatly assist users in understanding how to accurately complete their own forms. Each section of the form typically contains specific information that needs to be filled.
-
General information section detailing the inspection date and location.
-
Safety measures indicating whether all security features are operational.
Start Your Security Checklist Form Today with pdfFiller
Experience the ease of using pdfFiller to complete your Security Checklist Form. With user-friendly features and secure processing, you can efficiently manage your forms and enhance your organization’s security protocols.
How to fill out the security checklist form
-
1.Access pdfFiller and search for the 'Security Checklist Form' in the template library.
-
2.Open the form by clicking on it, which will load the form into the pdfFiller interface.
-
3.Before you start filling out the form, gather necessary information such as details on locked security containers and alarm status.
-
4.Navigate through the form to find checkboxes and fields. Click on each checkbox to select items that meet security standards.
-
5.Complete each required field with accurate and up-to-date information concerning the work area.
-
6.Review your entries for completeness and correctness, ensuring all sections of the form are accurately filled.
-
7.Once you are satisfied with your responses, use the options in pdfFiller to save your progress.
-
8.You can also download the completed form to your device or submit it directly through pdfFiller’s submission options.

What are the eligibility requirements to use the Security Checklist Form?
There are no specific eligibility requirements to use the Security Checklist Form; however, it is intended for use by government agencies and their contractors conducting security inspections.
Are there deadlines for submitting the completed Security Checklist Form?
Typically, there are no strict deadlines for submitting the Security Checklist Form; however, it should be completed in a timely manner following security protocols to ensure compliance.
How can I submit the Security Checklist Form once completed?
You can submit the Security Checklist Form directly through pdfFiller by following the submission prompts, or you can download it and submit it via your agency’s preferred submission method.
What supporting documents are needed when completing the form?
Generally, supporting documents such as security logs, inspection records, and facility access information may be required to fill out the Security Checklist Form accurately.
What common mistakes should I avoid when filling out the form?
Common mistakes include not checking all required items, missing entries in the fields, and failing to review the completed form for accuracy before submission.
How long does it take to process the Security Checklist Form?
Processing times may vary depending on the agency's response protocols. However, once submitted, it typically takes a few days for review and feedback.
What specific concerns should I address when using the Security Checklist Form?
Ensure that all security-related items listed on the form are properly checked. Pay particular attention to compliance with 32 CFR 2003 regulations as prescribed.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
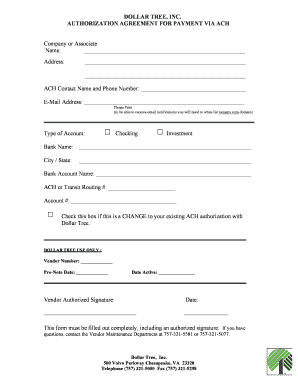
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.