Get the free nentwork protocols
Show details
Network Communication Protocols Sun NFS Applejack IS Storage Area Network (SAN) Network File System WM9V Port Mapper MOUNT Server SIP-Info ICC Extended Gateway Control Protocol MTP3 SIP SGC Simple
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign nentwork protocols
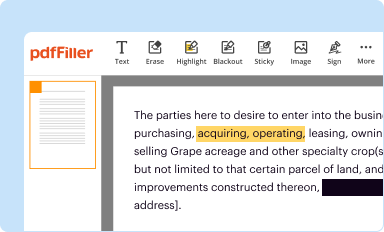
Edit your nentwork protocols form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
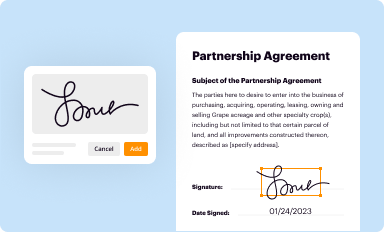
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
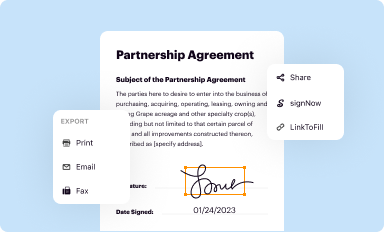
Share your form instantly
Email, fax, or share your nentwork protocols form via URL. You can also download, print, or export forms to your preferred cloud storage service.
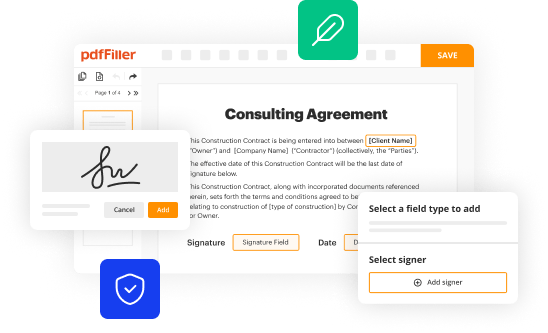
How to edit nentwork protocols online
Here are the steps you need to follow to get started with our professional PDF editor:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit nentwork protocols. Rearrange and rotate pages, add new and changed texts, add new objects, and use other useful tools. When you're done, click Done. You can use the Documents tab to merge, split, lock, or unlock your files.
4
Save your file. Choose it from the list of records. Then, shift the pointer to the right toolbar and select one of the several exporting methods: save it in multiple formats, download it as a PDF, email it, or save it to the cloud.
With pdfFiller, dealing with documents is always straightforward.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out nentwork protocols
How to fill out network protocols:
01
Understand the purpose of the network protocols. Familiarize yourself with the specific protocols you are working with and their intended functions.
02
Determine the required information. Identify the necessary details that need to be included in the network protocols, such as IP addresses, port numbers, and encryption settings.
03
Consult relevant documentation. Review any guidelines, manuals, or technical specifications provided by the network protocol's creators or industry standards organizations.
04
Follow the correct format. Ensure that you adhere to the specific formatting guidelines for the network protocols you are filling out. This may include using a certain syntax or structure.
05
Provide accurate information. Enter the requested details accurately and precisely to avoid any potential errors or complications in the networking environment.
Who needs network protocols:
01
Network administrators: Network protocols are essential for network administrators as they enable them to establish and manage network connections, configure security settings, and optimize network performance.
02
Software developers: For developers creating network-based applications, knowledge of network protocols is crucial. They need to understand how protocols like HTTP, TCP/IP, or FTP work to ensure their applications can communicate effectively over the network.
03
IT professionals: Network protocols are essential knowledge for IT professionals responsible for troubleshooting network issues, diagnosing problems, and ensuring network connectivity within an organization.
04
System administrators: System administrators depend on network protocols to maintain and monitor network infrastructure, ensuring smooth communication between devices and systems.
05
Businesses and organizations: In today's interconnected world, almost every business or organization relies on network protocols to enable data sharing, communication, and collaboration among employees, departments, and external entities. Without network protocols, organizations would struggle to function efficiently in a networked environment.
Fill
form
: Try Risk Free






People Also Ask about
What is the network protocols?
A network protocol is an established set of rules that determine how data is transmitted between different devices in the same network. Essentially, it allows connected devices to communicate with each other, regardless of any differences in their internal processes, structure or design.
What are network protocols written in?
Network programming is the process of writing code that enables computers to communicate over a network. This code must be written in a language that is compatible with the network protocol being used. Common languages for network programming include C, C++, Java, and Python.
What are the 4 types of networking protocols?
Transmission Control Protocol (TCP) Internet Protocol (IP) User Datagram Protocol (UDP) Post office Protocol (POP)
What are the different types of Internet Protocol forms?
Types of Internet Protocols File retrieval protocols. This type of service was one of the earliest ways of retrieving information from computers connected to the Internet. FTP (File Transfer Protocol) Gopher. Telnet. FTP. Gopher. telnet.
What is the most common network protocol?
Transmission Control Protocol (TCP) Through this process, the TCP/IP suite controls communication across the internet.
What are the 3 main protocols?
There are three main types of network protocols, including network management protocols, network communication protocols and network security protocols.
For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I send nentwork protocols for eSignature?
When your nentwork protocols is finished, send it to recipients securely and gather eSignatures with pdfFiller. You may email, text, fax, mail, or notarize a PDF straight from your account. Create an account today to test it.
How can I get nentwork protocols?
The premium subscription for pdfFiller provides you with access to an extensive library of fillable forms (over 25M fillable templates) that you can download, fill out, print, and sign. You won’t have any trouble finding state-specific nentwork protocols and other forms in the library. Find the template you need and customize it using advanced editing functionalities.
How do I edit nentwork protocols in Chrome?
Install the pdfFiller Google Chrome Extension to edit nentwork protocols and other documents straight from Google search results. When reading documents in Chrome, you may edit them. Create fillable PDFs and update existing PDFs using pdfFiller.
What is nentwork protocols?
Nentwork protocols are a set of rules and conventions that dictate how devices in a computer network communicate and exchange data.
Who is required to file nentwork protocols?
There is no specific requirement to file nentwork protocols as they are not typically filed. However, network administrators or IT professionals are responsible for implementing and managing network protocols.
How to fill out nentwork protocols?
Nentwork protocols are not filled out like forms. They are implemented and configured in network devices such as routers, switches, and firewalls according to the protocol specifications and requirements.
What is the purpose of nentwork protocols?
The purpose of network protocols is to enable communication between devices in a network by defining how data is formatted, transmitted, received, and acknowledged. They ensure that data is transferred reliably and efficiently.
What information must be reported on nentwork protocols?
Nentwork protocols do not typically require reporting. However, network logs and monitoring systems may capture information such as source and destination IP addresses, ports, protocol types, and timestamps for troubleshooting and security purposes.
Fill out your nentwork protocols online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Nentwork Protocols is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.