Last updated on Apr 10, 2026

Get the free Network Data and Security Supplemental Application
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is network data and security
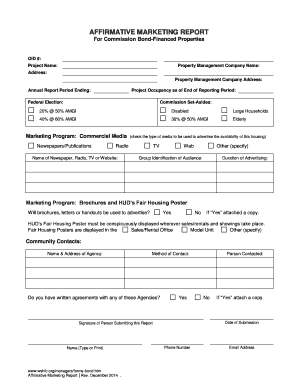
The Network Data and Security Supplemental Application is a business form used by companies to apply for network security coverage.
pdfFiller scores top ratings on review platforms




Who needs network data and security?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to network data and security
What is the Network Data and Security Supplemental Application?
The Network Data and Security Supplemental Application serves as a crucial tool for companies seeking network security coverage. This data security application facilitates the assessment of risks associated with data protection, including aspects like cyber-extortion.
Typically utilized by a range of industries, this form is aimed at organizations that require detailed evaluation across various coverage areas, including business interruption and privacy liability. Key users encompass IT firms, healthcare providers, financial institutions, and any organization handling sensitive information.
Purpose and Benefits of the Network Data and Security Supplemental Application
This supplemental insurance form plays a vital role in helping businesses secure adequate coverage against evolving network threats. With data protection becoming increasingly critical, insurance coverage offers essential safeguards for operations and reputation.
By completing the form, companies can access comprehensive cyber insurance, thus minimizing their risks during incidents of security breaches. Without sufficient coverage, organizations might face severe repercussions, including financial losses and reputational damage, stemming from data breaches or business interruptions.
Key Features of the Network Data and Security Supplemental Application
The network data security form comprises several key sections that ensure thorough evaluation of security practices. Among its core components are data handling practices, compliance checks, and specific security measures utilized by the organization.
An authorized representative must provide their signature, validating the information presented in the application. The design of the online form is user-friendly, allowing for easy navigation and completion.
Who Needs the Network Data and Security Supplemental Application?
This form targets a diverse range of businesses that handle sensitive information and are thus at risk for network security breaches. Industries such as healthcare, finance, e-commerce, and technology are prime candidates for this application.
Roles such as IT managers, compliance officers, and risk management personnel are typically responsible for completing the application to ensure that their organizations are adequately protected.
How to Fill Out the Network Data and Security Supplemental Application Online (Step-by-Step)
Completing the application through pdfFiller involves a straightforward process:
-
Access the form through the pdfFiller platform.
-
Gather essential information about your organization's data handling practices.
-
Complete each section of the application, paying attention to detailed requirements.
-
Add the necessary signature from an authorized representative.
-
Review the completed application for accuracy before submission.
This data security application not only facilitates a comprehensive submission but also ensures that all fields are addressed correctly.
Common Errors and How to Avoid Them
When filling out the network data security form, applicants often encounter several common pitfalls. Frequent mistakes include incomplete sections, inaccurate data entry, and neglecting to ensure compliance with mandatory requirements.
To promote accuracy in completion, applicants should adhere to the following best practices:
-
Thoroughly read each section's instructions.
-
Double-check all entries before finalizing the application.
-
Utilize validation features available in pdfFiller to minimize mistakes.
Submission Methods and Delivery Options for the Network Data and Security Supplemental Application
Once the application is completed, users have multiple submission methods at their disposal. These include online submission through a secure portal, email, or traditional postal mail.
Applicants are encouraged to verify the submission process and track the application's status for peace of mind. Emphasizing the importance of confidentiality, users can rest assured that sensitive data is handled securely throughout the submission process.
Security and Compliance for the Network Data and Security Supplemental Application
When completing the Network Data and Security Supplemental Application, compliance with local and international security regulations is paramount. This includes adherence to standards like HIPAA and GDPR.
Utilizing pdfFiller ensures that data protection measures are in place during the application process, thereby safeguarding sensitive information. It is crucial for all organizations to prioritize the secure handling of their data throughout this process.
How pdfFiller Helps You Complete the Network Data and Security Supplemental Application
pdfFiller enhances the experience of completing the network data security application by offering robust features. These include text editing capabilities, eSigning options, and secure cloud storage.
The fillable form template significantly aids in ensuring accuracy and efficiency, contributing to a smooth document management experience. By leveraging these features, users can manage their applications effectively.
Get Started with Your Network Data and Security Supplemental Application Today!
Completing the Network Data and Security Supplemental Application is essential for obtaining quality coverage. Engaging with pdfFiller simplifies this process, providing users the tools necessary for efficient form filling.
Explore other features of pdfFiller to address a variety of documentation needs as you begin your journey toward enhanced network security insurance.
How to fill out the network data and security
-
1.To access the Network Data and Security Supplemental Application on pdfFiller, visit the pdfFiller website and use the search function to locate the specific form.
-
2.Once you find the form, click on it to open it in the editing interface provided by pdfFiller.
-
3.Begin completing the form by filling in the required fields such as the full name of the applicant and other pertinent information about your company’s data handling practices.
-
4.Take your time to review any checkboxes and accompanying instructions to ensure all necessary details are gathered before submission.
-
5.Consider gathering supporting documentation related to your company’s security measures and compliance with relevant standards to have on hand while filling out the form.
-
6.As you complete the fields, utilize the tools provided by pdfFiller, such as text editing and form navigation options, to make the process smooth and efficient.
-
7.After completing the information, carefully review all entries to make sure no fields are left blank and all information is accurate.
-
8.Once you are satisfied with the completed application, save your changes within pdfFiller.
-
9.You may download a copy of the completed form for your records or directly submit it to the appropriate insurer using the submission options available through pdfFiller.

Who is eligible to complete the Network Data and Security Supplemental Application?
The form must be completed by an authorized representative of the company seeking network security coverage. This representative should have knowledge of the company's data handling practices and security measures.
What types of coverage does this application apply for?
This application is specifically for network security coverage, including Network Security and Privacy Liability, Business Interruption, Information Asset Protection, and Cyber-Extortion coverage.
Are there any supporting documents required with this form?
While the application itself does not mandate specific documents, it is advisable to have supporting documentation regarding the company’s security measures and data handling practices available for reference during completion.
What is the best way to submit the completed application?
You can submit the completed application through pdfFiller directly to the relevant insurance provider, ensuring to follow any specific submission instructions they may have.
Can I make changes to the form after submission?
Generally, once the application is submitted, changes cannot be made without contacting the insurance provider directly. It is crucial to review the form thoroughly before submission to avoid errors.
How long does it take to process the application?
Processing times can vary by provider, but it is typical to expect a response within several business days of submitting the form. Check with your provider for more specific timelines.
What are common mistakes to avoid when filling out the form?
Common mistakes include leaving fields blank, providing inaccurate or outdated information, and missing the signature of the authorized representative. Always double-check all entries before submission.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
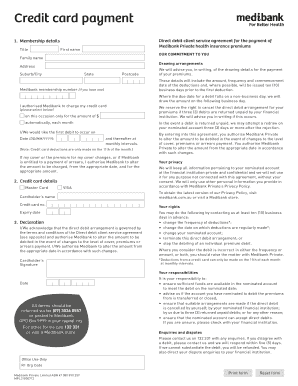
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.