Get the free cracking the code third edition
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

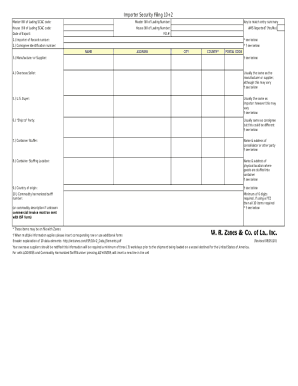
What is cracking form code third
The Cracking Form Code Third is a digital document used by individuals and organizations to outline protocols for secure coding practices in software development.
pdfFiller scores top ratings on review platforms




Love it, saves time makes my life a heck of a lot easie
Of all of the online PDF Editors, yours is, by far, the best! Such a joy! Thank you!
Who needs cracking form code third?
Explore how professionals across industries use pdfFiller.
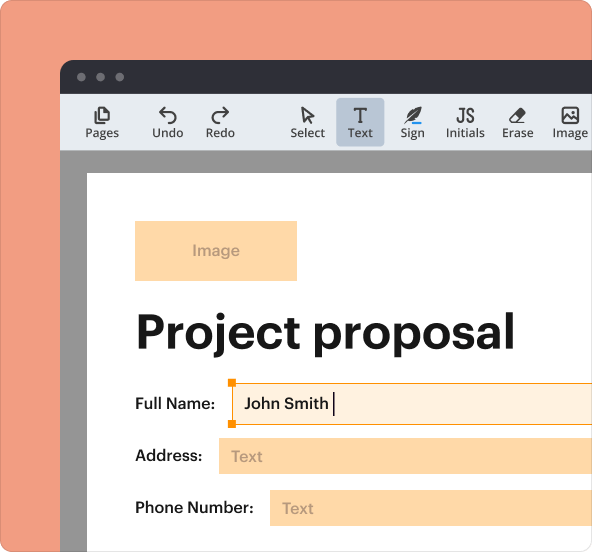
How to fill out the cracking form code third
-
1.To start, access pdfFiller and create an account or log in if you already have one. Search for 'Cracking Form Code Third' in the templates.
-
2.Once you locate the form, click on it to open. Familiarize yourself with the interface, noting available tools.
-
3.Before filling out the form, gather all necessary information, including security protocols, team roles, and any relevant project documentation.
-
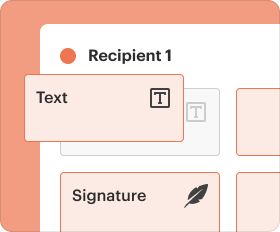
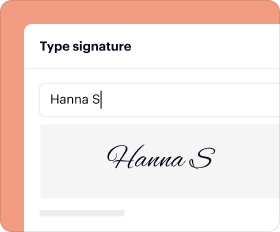
4.Begin completing the form by clicking on the fields and entering your information. Use the text tools to edit, adjust, and format your answers as needed.
-
5.Make sure all required fields are complete to avoid submission issues; take your time to ensure accuracy.
-
6.After filling in all necessary information, review your entries carefully. Check for clarity and completeness to avoid common mistakes.
-
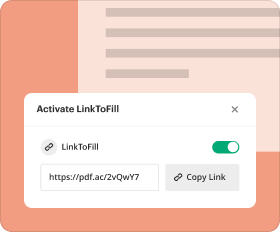
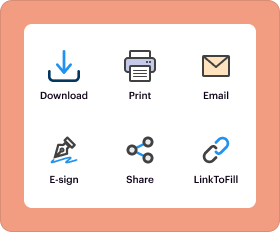
7.Finally, once you're satisfied with the content, save your work on pdfFiller, and download or directly submit the form through the platform’s submission options.
Who is eligible to use the Cracking Form Code Third?
Eligibility to use the Cracking Form Code Third generally includes software developers, IT professionals, and organizations interested in enhancing their coding security practices.
Are there deadlines for submitting the Cracking Form Code Third?
While specific deadlines may not apply to this form, timely completion is recommended to ensure up-to-date security measures in software development.
How can I submit the Cracking Form Code Third?
You can submit the Cracking Form Code Third by saving your completed document and emailing it to the relevant department or uploading it directly through your organization's internal system.
What supporting documents are required with the Cracking Form Code Third?
Typically, supporting documents might include a project plan, security policy statements, and prior assessment reports relevant to the organization's coding practices.
What are common mistakes to avoid when completing the form?
Common mistakes include omitting critical security measures, using outdated coding practices, and not aligning with industry standards outlined in the form.
What is the processing time for the Cracking Form Code Third?
Processing time may vary; however, it’s advisable to allow several business days for review and approval, especially if submitted to multiple stakeholders.
What should I do if I have concerns about the form's content?
If you have concerns about the content of the Cracking Form Code Third, consult with your team lead or a security expert before submission to ensure all protocols are accurately represented.
Related Catalogs
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.