Last updated on Apr 11, 2026

Get the free Request for ELM Security Access
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is request for elm security
The Request for ELM Security Access is a government form used by employees of Minnesota Management & Budget to request access to the ELM system.
pdfFiller scores top ratings on review platforms




Who needs request for elm security?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to request for elm security
What is the Request for ELM Security Access?
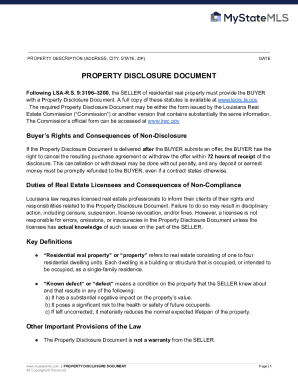
The Request for ELM Security Access form is essential for employees of the Minnesota Management & Budget to gain access to the ELM (Employee Learning Management) system. This system plays a crucial role in facilitating ongoing professional development and training opportunities for users.
The form requests vital information, including personal details and the type of access required, which helps streamline the process for all involved. Key data to be filled in includes User Last Name, Employee ID, Email, and other personal identifiers.
In essence, the ELM security access form serves as a vital link between employees and essential resources for skill enhancement and training.
Purpose and Benefits of the Request for ELM Security Access
Completing the Request for ELM Security Access is critical for users looking to expand their professional horizons. Securing ELM access enables individuals to take advantage of extensive training programs, ensuring they are equipped with the necessary skills to excel in their roles.
-
Enhances training opportunities, facilitating continuous learning.
-
Supports users in developing new skills and improving current competencies.
-
Streamlines processes for supervisors and agencies, enhancing compliance efforts.
Overall, this request contributes to a more qualified workforce and promotes effective management practices across agencies.
Key Features of the Request for ELM Security Access
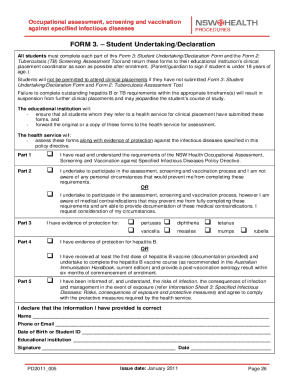
The Request for ELM Security Access form contains several key features that users must be aware of. Each section is designed to capture essential information efficiently.
-
Essential fields include User Last Name, Employee ID, and Email.
-
Required signatures from the user, supervisor, and agency ELM key administrator ensure accountability.
-
Available options include checkboxes for 'New Access' and 'Change Access'.
Understanding these features will make the process smoother and more efficient for everyone involved.
Who Needs the Request for ELM Security Access?
This form is intended for a diverse group of roles within Minnesota state agencies. Key participants include users seeking access, supervisors who supervise those users, and agency administrators overseeing ELM access.
Eligibility to submit this request generally encompasses any employee or supervisor who interacts with the Employee Learning Management system. Each role has specific responsibilities in ensuring the form is correctly completed and submitted.
How to Fill Out the Request for ELM Security Access Online (Step-by-Step)
To complete the Request for ELM Security Access form online, follow these step-by-step instructions:
-
Access the digital form through pdfFiller or the designated platform.
-
Fill in required fields such as User Last Name and Employee ID.
-
Select the appropriate access type and role based on your needs.
-
Review all entries to ensure accuracy before submitting the form.
Taking time to verify your entries is crucial to avoid delays in processing your request.
Submission Methods and What Happens After You Submit
Once the Request for ELM Security Access form is completed, there are multiple submission methods available:
-
Submitting the form online through a secure portal.
-
Emailing the completed form to the appropriate agency contact.
-
Delivering the form in person at specified agency offices.
After submission, users can expect a set processing timeframe and confirmation of their access request. Tracking the status helps ensure that no steps are overlooked during the processing period.
Security and Compliance for the Request for ELM Security Access
Security and compliance are paramount when handling the Request for ELM Security Access form. The platform, pdfFiller, ensures that all document processes are secure through robust encryption and compliance with federal standards.
This approach guarantees that sensitive information provided in the form is handled with care, adhering to privacy protocols aligned with legislation like HIPAA and GDPR, thus giving users peace of mind during the submission process.
How pdfFiller Helps You with the Request for ELM Security Access
pdfFiller is an excellent resource for users completing the Request for ELM Security Access form. With its cloud-based capabilities, users can easily edit the form, add digital signatures, and submit it all from their browser without needing additional downloads.
Specific features that improve the user experience include fillable fields, document organization options, and a secure eSigning process, making the entire experience seamless and efficient.
Take the Next Step with Your ELM Security Access Request!
Using pdfFiller for your Request for ELM Security Access form transforms the experience into a user-friendly process. The service’s emphasis on security, convenience, and efficient form management encourages users to complete their requests without hassle.
Embrace the advantages of digital form management to ensure a swift and organized approach to securing your ELM access!
How to fill out the request for elm security
-
1.Access and open the Request for ELM Security Access form on pdfFiller by searching for the form title in the search bar or navigating through the government forms section.
-
2.Once the form is open in pdfFiller, familiarize yourself with the interface. Utilize the toolbars to highlight, insert text, or add checkmarks where necessary.
-
3.Before starting, gather necessary information including your personal details, Employee ID, email, Agency Number, and specifics concerning the access requested.
-
4.Begin filling out the form by entering your Last Name and other personal information in the designated fields. Use the fillable fields to record the purpose for your access and the type of access needed.
-
5.Indicate your role by checking the appropriate options for 'New Access' or 'Change Access,' ensuring all relevant sections are completed accurately.
-
6.Sign the form electronically where required, which includes your signature and the signatures of your supervisor and the agency ELM key administrator.
-
7.Review the entire form to verify all information is complete and accurate before finalizing your submission.
-
8.Once you are satisfied, use pdfFiller’s options to save the form, download it to your device, or submit it directly through designated submission pathways set by your agency.

Who is eligible to request ELM Security Access?
Eligibility to request ELM Security Access includes employees of Minnesota Management & Budget who require access to the Employee Learning Management system, as well as their supervisors and designated agency administrators.
Is there a deadline for submitting the access request?
There are typically no strict deadlines for submitting the Request for ELM Security Access. However, timely submissions are encouraged to ensure uninterrupted access, especially for new hires or department changes.
What are the submission methods for this form?
The Request for ELM Security Access form can be submitted electronically via pdfFiller, downloaded for manual submissions, or sent through email as directed by your agency’s specific procedures for document handling.
What supporting documents do I need to include?
Generally, you’ll need to include your personal identification information like your Employee ID and other relevant credentials to support your request for access. Additional documentation may vary based on agency policies.
What common mistakes should be avoided when filling out this form?
To avoid delays, ensure that all required fields are completed accurately and that all necessary signatures are obtained before submission. Double-check that the correct type of access is selected.
How long does it take to process the access request?
Processing times for the Request for ELM Security Access can vary but are generally completed within a week. Always follow up with your administrator for specific timelines.
What if I need to change my access after it has been granted?
If you need to change your access, you must complete a new Request for ELM Security Access and indicate the necessary changes. Ensure that all required signatures are collected.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.