Last updated on Apr 11, 2026

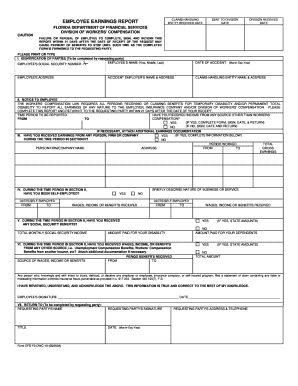
Get the free Cyber Network Security Privacy Application
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is cyber network security privacy
The Cyber Network Security Privacy Application is a business form used by companies to apply for cyber network security and privacy services.
pdfFiller scores top ratings on review platforms




Who needs cyber network security privacy?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to cyber network security privacy
What is the Cyber Network Security Privacy Application?
The Cyber Network Security Privacy Application is essential for businesses seeking to enhance their cyber security measures and ensure privacy policy compliance. This form collects critical information related to data collection practices and security methods, helping organizations address legal and regulatory requirements.
By filling out this privacy policy compliance form, businesses demonstrate their commitment to protecting sensitive information. The application is a vital tool in maintaining transparency and accountability regarding data management practices.
Purpose and Benefits of the Cyber Network Security Privacy Application
Utilizing the Cyber Network Security Privacy Application is crucial for businesses navigating today's complex digital landscape. By securing sensitive information, organizations can mitigate risks associated with data breaches and compliance failures.
Filling out this application illustrates a company's dedication to data security and adherence to privacy regulations. The advantages include enhanced credibility, improved customer trust, and the potential for competitive differentiation in the marketplace.
Who Needs the Cyber Network Security Privacy Application?
This application is relevant for various types of businesses and organizations, particularly those handling sensitive data that must comply with stringent privacy regulations. Industries like healthcare, finance, and retail are significantly impacted by data security and privacy policies.
Professionals responsible for cybersecurity and compliance, including IT managers and legal advisors, should complete this application to ensure their organization's alignment with necessary security standards.
Eligibility Criteria for the Cyber Network Security Privacy Application
To be eligible for the Cyber Network Security Privacy Application, businesses must meet specific criteria. Companies must operate within legal boundaries and adhere to regulatory guidelines that govern data privacy.
The eligibility requirements may also include considerations about the organizational structure and types of personal data handled. Ensuring that your business meets these standards is vital before attempting to fill out the application.
How to Fill Out the Cyber Network Security Privacy Application Online (Step-by-Step)
-
Begin by accessing the form online through a secure portal.
-
Complete each section with accurate details about your organization.
-
Pay special attention to fields requesting data collection methods and security measures.
-
Double-check information to avoid common errors that could delay processing.
-
Submit the form once all sections are filled out thoroughly.
Ensuring you include all required information is crucial for the accuracy of your submission. Commonly overlooked fields can lead to unnecessary processing delays.
Common Errors and How to Avoid Them
Applicants frequently encounter pitfalls during the form-filling process, which can result in incomplete or inaccurate submissions. Common mistakes include omitting essential details or misinterpreting required information.
To avoid these issues, double-check all entries before submission. Verifying compliance with privacy policies prior to submitting the application can also prevent potential problems during review.
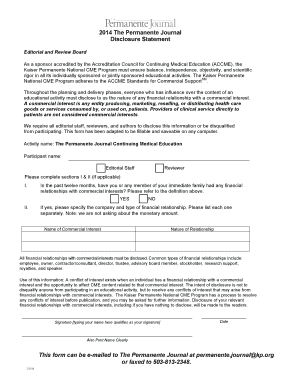
Submission Methods and Delivery
Once the Cyber Network Security Privacy Application is completed, you can submit it through various methods, including online and traditional mail options. Each submission method offers different benefits, such as convenience or confirmation of receipt.
Consider timing when submitting your application; understanding the processing times is essential for planning your next steps. Ensuring successful delivery involves obtaining confirmation of receipt regardless of the submission method chosen.
What Happens After You Submit the Cyber Network Security Privacy Application?
After submitting the Cyber Network Security Privacy Application, businesses can expect a thorough review process. Typically, a timeline is established indicating how long the review will take.
If any issues arise during the review, organizations may receive requests for additional information. Understanding the potential outcomes of a successful application versus a rejected one is critical for effective planning moving forward.
Security and Compliance for the Cyber Network Security Privacy Application
Security plays a vital role in managing the Cyber Network Security Privacy Application and the associated data. Utilizing measures like 256-bit encryption is essential for protecting sensitive information throughout the application process.
Compliance with regulations such as SOC 2 Type II, HIPAA, and GDPR ensures that the application process aligns with industry standards. Users should prioritize data security while handling documents relating to this application to mitigate risks.
Ready to Start? Utilize pdfFiller for Your Cyber Network Security Privacy Application
Utilizing pdfFiller allows you to fill out the Cyber Network Security Privacy Application efficiently and securely. The platform offers features such as secure document storage, eSigning capabilities, and compliance with data security standards.
By choosing pdfFiller, you are simplifying the document management process, ensuring a smooth user experience while maintaining high standards of data protection and regulatory compliance.
How to fill out the cyber network security privacy
-
1.To access the Cyber Network Security Privacy Application on pdfFiller, go to the pdfFiller website and use the search bar to locate the form by its name.
-
2.Once you have opened the form, familiarize yourself with its layout, which includes various fillable fields and checkboxes.
-
3.Before starting, gather all necessary information regarding your company's data collection practices and security measures.
-
4.As you navigate through the form, click on each field to input your details carefully, verifying the accuracy of the data you enter.
-
5.Pay close attention to sections that require specifics about your privacy policy compliance and the types of personal information you handle.
-
6.After completing the form, thoroughly review all entries to ensure that no fields are left unfilled and that all information is accurate.
-
7.When satisfied with your responses, you can save your progress in pdfFiller or download a copy of the completed form for your records.
-
8.To submit the form, follow the submission guidelines provided by the receiving entity, which may include emailing or uploading the document as directed.

What is the eligibility requirement for submitting this form?
Eligibility primarily applies to businesses and organizations that collect and manage personal data and wish to implement robust cybersecurity and privacy measures.
Are there any deadlines associated with this application?
Specific deadlines depend on the intended submission recipient. It’s essential to check with the entity requesting the form to avoid delays.
How should I submit the completed Cyber Network Security Privacy Application?
The submission method will vary based on the requestor's requirements. Typically, you may submit the completed form via email or through an online portal.
What supporting documents are needed with the application?
While the form itself captures essential information, you might need to provide additional documents related to your organization’s data security practices and privacy policies.
What mistakes should I avoid when filling out the form?
Common mistakes include leaving fields blank, misrepresenting data collection practices, and not adhering to the privacy policy guidelines. Thoroughly review your form before submission.
How long does it take to process the application?
Processing times can vary significantly based on the organization reviewing the application. It's advisable to follow up with the entity after submission for updates.
What if I have concerns or questions about the form itself?
If you have specific concerns about the Cyber Network Security Privacy Application, consult the instructions included with the form or contact the entity requesting it for clarification.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.