Last updated on Mar 27, 2026

Get the free Lab - Troubleshooting ACL Configuration and Placement
We are not affiliated with any brand or entity on this form
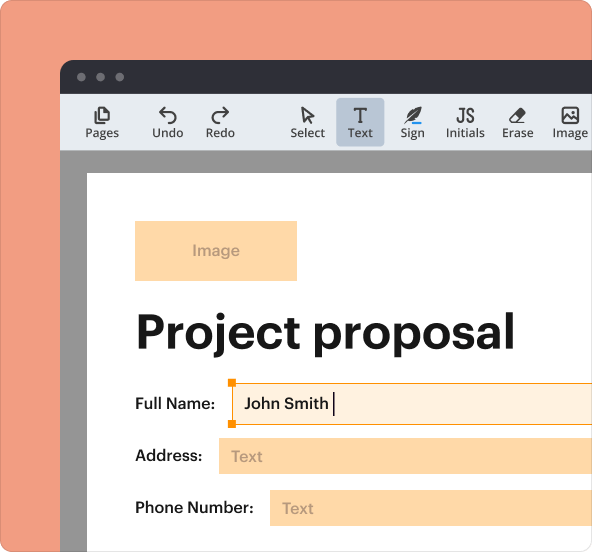
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is lab - troubleshooting acl
The Lab - Troubleshooting ACL Configuration and Placement is a lab guide used by network administrators to troubleshoot ACL (Access Control List) configuration and placement on Cisco routers.
pdfFiller scores top ratings on review platforms




Who needs lab - troubleshooting acl?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to lab - troubleshooting acl
What is the Lab - Troubleshooting ACL Configuration and Placement?
This lab guide is designed to help users troubleshoot ACL (Access Control List) configuration and placement on Cisco routers. The purpose of the lab is to enhance users' skills in managing network security by effectively configuring and troubleshooting ACLs. Key concepts related to ACL configuration and troubleshooting are explored, with a focus on Cisco routers.
Purpose and Benefits of the Lab - Troubleshooting ACL Configuration and Placement
This lab guide is essential for users looking to improve their network security knowledge. By mastering ACL management through this lab, users can significantly enhance their practical skills in troubleshooting and configuring ACLs, ultimately leading to a more secure network environment.
Benefits of this lab include:
-
Improved understanding of ACLs
-
Hands-on experience with troubleshooting techniques
-
Enhanced network security through effective management
Key Features of the Lab - Troubleshooting ACL Configuration and Placement
Users will find numerous features included in the lab guide, such as a comprehensive topology, addressing table, and detailed step-by-step instructions. The guide emphasizes both corporate networks and DMZ configurations, catering to various networking scenarios.
Key features include:
-
In-depth ACL configuration steps
-
Visual topology representation
-
Instructions suited for both novice and experienced users
Who Needs the Lab - Troubleshooting ACL Configuration and Placement?
This lab guide is tailored for network administrators, IT professionals, and anyone involved in network security management. Industries such as healthcare, finance, and technology can greatly benefit from solid ACL management practices.
How to Use the Lab - Troubleshooting ACL Configuration and Placement Online
To effectively navigate and utilize the lab, users should follow these steps:
-
Access the lab guide online.
-
Review the provided topology and addressing table.
-
Follow the step-by-step instructions for ACL configuration.
-
Implement the configurations in a controlled environment.
-
Refer to the troubleshooting tips as needed.
Common Challenges in ACL Configuration and How to Overcome Them
Some common mistakes users may encounter during ACL configuration include misconfigured rules and understanding the implications of ACL placement. To avoid such errors, users should adhere to best practices and utilize the resources available within the lab guide. Practical exercises can enhance learning outcomes and reinforce concepts.
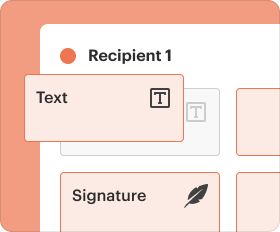
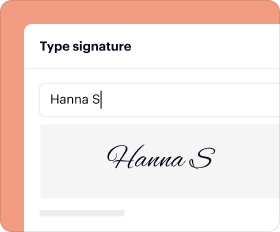
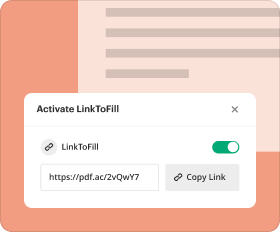
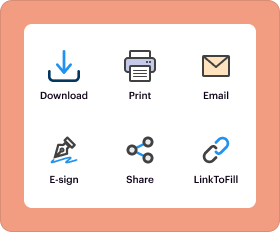
How pdfFiller Supports Your Lab Experience
pdfFiller can greatly enhance your experience with the lab guide by providing advanced document management solutions. Features such as document editing, secure sharing, and eSigning allow users to manage sensitive documents effectively during the troubleshooting process.
Security and Compliance in Network Management
Security in ACL configuration is paramount. Compliance standards such as HIPAA and GDPR are integral to network security professionals. Choosing to utilize pdfFiller ensures that users' sensitive documents are handled with appropriate security measures, including 256-bit encryption.
Next Steps After Completing the Lab - Troubleshooting ACL Configuration and Placement
After finishing the lab guide, users are encouraged to share their experiences and consider seeking additional training to deepen their understanding. Revisiting the guide periodically can help reinforce knowledge as network systems evolve and change.
Enhance Your Skills with Additional Resources
To further enhance learning on network management and ACL configurations, users are encouraged to explore related resources. These may include links to other tutorials, courses, or informative articles. Continuous learning is crucial in the ever-evolving field of network security.
How to fill out the lab - troubleshooting acl
-
1.Access pdfFiller and log in to your account. If you do not have an account, create one using your email address.
-
2.Once logged in, search for the Lab - Troubleshooting ACL Configuration and Placement form in the search bar or browse through available business forms.
-
3.Open the form by clicking on its title to load it into the pdfFiller editor.
-
4.Prior to filling out the form, gather essential information such as your network topology and any existing ACL configurations you already have.
-
5.Use the pdfFiller editing tools to navigate through each section of the lab guide. Read the instructions carefully before performing configurations or troubleshooting steps.
-
6.You can add notes or highlight sections within the guide as needed for clarification during the troubleshooting process.
-
7.As you complete each step, verify your configurations and ensure that they align with the provided instructions. Use the ‘Preview’ feature to check your work.
-
8.Once all sections are completed, thoroughly review the entire document to ensure all steps were followed correctly and that configurations are accurate.
-
9.To save your work, click the save icon. You can also download the file in your preferred format by selecting the download option from the toolbar.
-
10.Finally, if you wish to print the form, use the print option available, or submit it electronically if needed.
Who can benefit from the Lab - Troubleshooting ACL Configuration and Placement?
This lab guide is beneficial for network engineers, IT professionals, students, and anyone managing or learning about Cisco router configurations and ACL troubleshooting.
Are there any prerequisites for using this lab guide?
Basic knowledge of networking and Cisco routers is recommended. Familiarity with Access Control Lists (ACLs) will help in effectively using the guide.
Can this lab guide be used for training purposes?
Yes, the lab guide serves as an excellent training resource for individuals and teams looking to enhance their skills in network security and ACL management.
Is there a submission process after completing the guide?
There is no formal submission process for the lab guide, as it is designed for self-study and practical application. You may want to document your results for your records.
What common mistakes should I avoid while using this lab guide?
Ensure to double-check configuration steps and verify settings before applying changes. Skipping steps might lead to improper ACL configurations and security issues.
How long does it take to complete the lab guide?
Completion time varies depending on your familiarity with ACL configurations and network troubleshooting, but expect to spend a few hours on thorough practice.
What type of support is available if I have questions while using the guide?
While there is no direct support for the lab guide itself, you may refer to Cisco documentation or seek help from networking forums and communities for assistance.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.