Last updated on Apr 12, 2026

Get the free Bomb Threat Checklist
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is bomb threat checklist
The Bomb Threat Checklist is a government form used by emergency responders to document detailed information about a bomb threat call.
pdfFiller scores top ratings on review platforms




Who needs bomb threat checklist?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to bomb threat checklist
What is the Bomb Threat Checklist?
The Bomb Threat Checklist is an essential tool designed to assist individuals in documenting critical details during bomb threat situations. Its purpose lies in providing a structured approach that emphasizes the importance of capturing immediate and accurate information to aid emergency response teams effectively. The checklist includes key sections focused on caller information, threat language, and background sounds, enabling personnel to gather comprehensive data swiftly.
Its efficient design is crafted for accessibility, ensuring that the form can be easily located near telephones during crisis scenarios. This preparedness is crucial in effectively managing bomb threats and establishes a standard protocol for organizations.
Purpose and Benefits of the Bomb Threat Checklist
The primary function of the Bomb Threat Checklist is to document vital information during threat calls. This documentation can significantly improve response times and the accuracy of reporting threats, as having a structured record allows responders to act with clarity and confidence. The checklist serves organizations by establishing a uniform method for dealing with emergencies.
-
Improves accuracy in threat reporting.
-
Enhances response time during emergencies.
-
Encourages a structured management approach.
-
Facilitates better communication among responders.
Key Features of the Bomb Threat Checklist
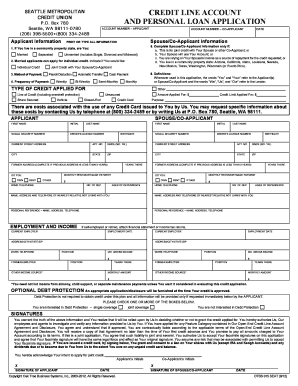
The Bomb Threat Checklist comprises various fillable fields and checkboxes for recording specific details about potential threats. Examples of critical questions to ask callers include inquiries regarding the location of the bomb, the type of threat, and any identifying features of the caller. Each question is designed to capture relevant information essential for assessment by security personnel.
-
Fillable fields for caller information and threat specifics.
-
Useful checkboxes for quick data entry.
-
Guided questions for comprehensive threat documentation.
-
Observations on caller's voice and background sounds.
Who Needs the Bomb Threat Checklist?
The checklist is particularly valuable for security personnel, office managers, and any staff responsible for safety in public spaces. It is most beneficial in settings such as schools, office buildings, and large public venues where the likelihood of encountering bomb threats may be higher. Organizations must proactively prepare for such incidents to ensure safety and to facilitate a unified response approach.
How to Fill Out the Bomb Threat Checklist Online (Step-by-Step)
Filling out the Bomb Threat Checklist online is a straightforward process. Here’s a detailed guide to assist users:
-
Access the checklist via pdfFiller.
-
Fill in the required fields, focusing on clarity and accuracy.
-
Ensure to include observations about the caller’s voice and any background sounds.
-
Review the completed checklist for any errors or omissions.
Using visual aids can also improve the accuracy of information entered in the checklist by providing examples of completed sections.
Reviewing and Validating the Bomb Threat Checklist
Checking the accuracy of the information recorded on the Bomb Threat Checklist is critical for effective response. Common errors can include missing details or incorrect interpretations of the caller's threats. Adhering to best practices for validation helps mitigate these risks.
-
Double-check all fillable fields and entries for completeness.
-
Avoid subjective interpretations by relying on factual data.
-
Follow a systematic process for reviewing the completed checklist to ensure it is ready for submission.
Submission Methods and Delivery of the Bomb Threat Checklist
The checklist can be submitted digitally through platforms like pdfFiller, which offers various options for electronic documentation. For those preferring print methods, physical submission options are also available. Tracking submissions to ensure timely processing is advised.
-
Explore digital submission options for instant delivery.
-
Learn about print options for those who require physical documentation.
-
Understand expected processing times for submitted checklists.
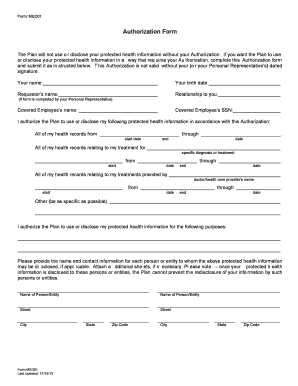
Security and Compliance for the Bomb Threat Checklist
When handling sensitive documents such as the Bomb Threat Checklist, robust security measures are necessary. It is crucial to comply with legal regulations, including GDPR and HIPAA, to protect the privacy of caller information and ensure data security strategies are in place. Organizations must prioritize these compliance aspects to foster trust among stakeholders.
How to Ensure the Effective Use of the Bomb Threat Checklist
Training staff on the effective utilization of the Bomb Threat Checklist is vital for maximizing its potential during emergencies. Proper interpretation of the collected information enables a swift and effective response, while regularly updating both the checklist and the response practices is crucial for maintaining relevance and effectiveness.
-
Provide staff training sessions focused on checklist use.
-
Encourage interpretation of data for informed decision-making.
-
Regularly review and update the checklist to incorporate new protocols.
Experience the Benefits of Using pdfFiller for Your Bomb Threat Checklist
Utilizing pdfFiller simplifies the form-filling process dramatically. Its user-friendly tools enhance the experience by allowing for easy editing, eSigning, and sharing of the Bomb Threat Checklist. Exploring pdfFiller's extensive features can streamline the way organizations manage and respond to bomb threats professionally.
How to fill out the bomb threat checklist
-
1.To access the Bomb Threat Checklist on pdfFiller, visit the official website and use the search bar to locate the form by entering its name.
-
2.Once you find the form, click on it to open it in the pdfFiller editor.
-
3.Before filling out the form, gather necessary information such as the time and date of the call, visible caller characteristics, and any details you may have from the conversation.
-
4.Navigate the pdfFiller interface to locate the fillable fields. Click on each field to enter the required information as prompted.
-
5.Pay close attention to sections requiring specific observations, such as the caller's voice characteristics and the background noise heard during the call.
-
6.Review all filled fields thoroughly, ensuring that all information is accurate and complete before finalizing.
-
7.After completing the form, you can either save it to your pdfFiller account or download it directly to your device.
-
8.If submitting the form electronically or printing it for submission, make sure to follow any specific instructions provided by your organization or local authorities.

Who is eligible to use the Bomb Threat Checklist?
The Bomb Threat Checklist is designed for use by emergency responders, including law enforcement, fire departments, and school safety personnel during bomb threat incidents.
Is there a deadline for completing the checklist?
There is no formal deadline for completing the Bomb Threat Checklist, but it should be filled out immediately after a bomb threat call to ensure accurate and timely information is recorded.
How should I submit the completed form?
Completed forms can be submitted through standard reporting channels as required by your agency or organization. Ensure you follow any specific submission guidelines provided.
What supporting documents are needed for this form?
Generally, no supporting documents are required with the Bomb Threat Checklist, but any additional notes or recordings from the call may be useful for reference.
What common mistakes should I avoid when filling out the form?
Common mistakes include neglecting to fill in all fields, providing inaccurate information, and failing to record the exact time of the call. Review your entries carefully.
How long does it take to process this form?
Processing times vary depending on the agency's procedures, but typically this form is processed quickly due to its urgent nature. Always check with your department for specifics.
What if I have concerns about using the form?
If you have concerns about using the Bomb Threat Checklist, consult with your supervisor or designated safety officer for guidance on filling it out correctly.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.