Last updated on Apr 13, 2026
Get the free IT Security Self-Assessment System Questionnaire
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.
What is it security self-assessment system
The IT Security Self-Assessment System Questionnaire is a business form used by IT professionals to evaluate the security controls and risk management of an IT system.
pdfFiller scores top ratings on review platforms




Who needs it security self-assessment system?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to it security self-assessment system
What is the IT Security Self-Assessment System Questionnaire?
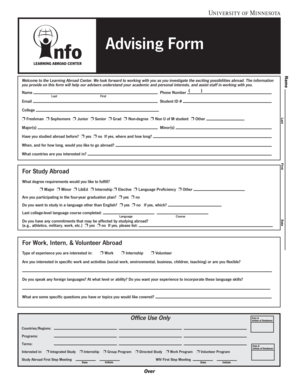
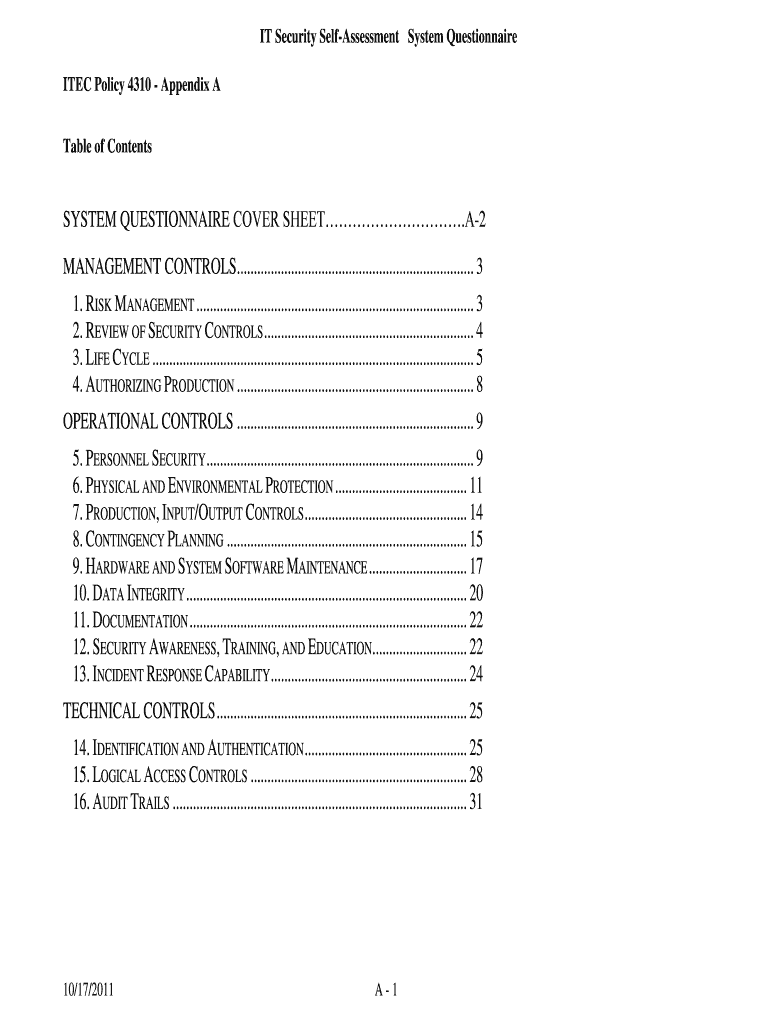
The IT Security Self-Assessment System Questionnaire serves as a vital tool for organizations to evaluate their IT security controls effectively. This form is structured to guide assessors through specific queries related to their system's management, operational, and technical controls, ensuring all critical aspects are addressed. Key components include fields designed for user input, such as 'System Name, Title, and Unique Identifier' alongside areas for assessors to provide their name and other relevant information.
Purpose and Benefits of the IT Security Self-Assessment Questionnaire
Organizations undertake self-assessments using the IT security risk management form to proactively identify vulnerabilities within their IT infrastructure. This assessment not only aids in enhancing compliance with industry standards but also fortifies the overall security posture of the organization. By conducting evaluations provided in the IT security controls evaluation, businesses can detect gaps in their security measures and implement necessary improvements.
Key Features of the IT Security Self-Assessment System Questionnaire
The form encompasses crucial elements that contribute to a comprehensive security evaluation:
-
Management controls that focus on governance and risk management.
-
Operational controls that assess procedures and policies in place.
-
Technical controls that verify the technical implementation of security measures.
Utilizing this IT security life cycle assessment allows organizations to maintain security throughout the life of their IT systems, ensuring that all elements are continuously evaluated and improved as necessary.
Who Needs the IT Security Self-Assessment System Questionnaire?
This questionnaire is essential for a variety of professionals, including IT managers, compliance officers, and security assessors. Its relevance spans across organizations of all sizes, from small businesses to large enterprises, emphasizing the importance of IT security management controls and operational controls in protecting sensitive information.
How to Fill Out the IT Security Self-Assessment System Questionnaire Online (Step-by-Step)
Follow this step-by-step guide to complete the IT Security Self-Assessment System Questionnaire using pdfFiller:
-
Access the IT security questionnaire PDF through pdfFiller.
-
Fill in the basic fields, including 'System Name, Title, and Unique Identifier.'
-
Provide information regarding the assessors in the designated sections.
-
Review your answers for completeness and accuracy.
-
Submit the form electronically through the platform.
Common Errors and How to Avoid Them
Users frequently encounter mistakes when completing the questionnaire. Common errors include:
-
Failing to provide complete information for all required fields.
-
Inaccurate entries that do not reflect the actual security posture.
To ensure a valid and effective assessment, adhere to best practices such as double-checking entries and utilizing clear, precise language throughout the form.
How to Submit the IT Security Self-Assessment System Questionnaire
Once the form is completed, there are multiple submission methods available:
-
Submit via email directly from pdfFiller.
-
Upload the completed form to a secure portal if required.
Ensure that you receive confirmation of your submission and track its status as needed to maintain a clear record of compliance.
Security and Compliance Considerations for the IT Security Self-Assessment System Questionnaire
When handling sensitive documents, the importance of data security and compliance cannot be overstated. Adhering to security requirements is critical, especially when utilizing platforms like pdfFiller, which complies with regulations such as HIPAA and GDPR. Additionally, the use of data encryption measures guarantees that the information submitted remains protected.
Utilize pdfFiller to Streamline Your IT Security Self-Assessment
By choosing to use pdfFiller, you can significantly enhance the process of filling out and managing the IT Security Self-Assessment System Questionnaire. The platform provides valuable features such as editing, eSigning, and sharing capabilities, which simplify the overall experience. Explore how pdfFiller can streamline your form requirements and improve your workflow efficiency.
How to fill out the it security self-assessment system
-
1.Access the form on pdfFiller by searching for 'IT Security Self-Assessment System Questionnaire' in the search bar.
-
2.Open the form by clicking on the appropriate link to load it into the editor.
-
3.Familiarize yourself with all sections of the form including management, operational, and technical controls.
-
4.Before starting, gather necessary information such as system details, assessor names, and relevant IT security policies.
-
5.Use the editing tools to fill in the required fields. Click on each blank field to type in your answers or select checkboxes where applicable.
-
6.Be thorough in providing specific details about the system, including its name, unique identifier, and security features.
-
7.Once completed, review all entries for accuracy, ensuring that all required sections are filled out.
-
8.If needed, utilize pdfFiller's collaboration features to share with colleagues for feedback before finalizing.
-
9.Save your document by clicking the save icon or selecting 'Download' to export it as a PDF.
-
10.You can submit the form electronically if applicable by following the submission procedures outlined by your organization or regulatory body.

Who is eligible to use the IT Security Self-Assessment System Questionnaire?
Any organization or individual responsible for IT system management and security can use this questionnaire. IT managers, cybersecurity personnel, compliance officers, and consultants should find it particularly beneficial.
What are the key sections included in the questionnaire?
The questionnaire includes sections on management controls, operational controls, and technical controls. Each section consists of specific questions designed to evaluate the security posture of IT systems.
Are there any deadlines for submitting the completed form?
Deadlines for submitting the IT Security Self-Assessment System Questionnaire typically depend on internal policies or regulatory requirements. Ensure you check with your organization for any specific timelines.
Can I save my progress while filling out the form on pdfFiller?
Yes, pdfFiller allows you to save your progress at any time. Use the save function to ensure all your inputs are retained before you continue editing or finalizing the document.
What common mistakes should I avoid when completing this form?
Common mistakes include leaving sections blank, providing inaccurate system details, and failing to review for errors. Ensure all fields are filled out accurately and double-check your entries before finalizing.
How can I submit the form after completing it?
After completing the questionnaire, you can submit it electronically if required, or print it for manual submission. Follow your organization's protocols for submitting the completed form.
What supporting documents might be required with this form?
While the IT Security Self-Assessment System Questionnaire itself may not require additional documents, relevant supporting documentation could include security policies, previous assessments, and compliance reports. Check with your organization for specifics.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.