Last updated on May 25, 2014

Get the free Access Security Requirements Agreement
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

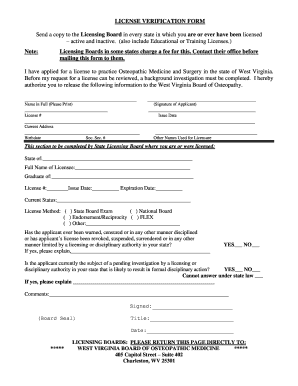
What is access security requirements agreement
The Access Security Requirements Agreement is a business document used by companies to ensure the privacy protection of consumer credit reports and outline security measures.
pdfFiller scores top ratings on review platforms




Who needs access security requirements agreement?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to access security requirements agreement
What is the Access Security Requirements Agreement?
The Access Security Requirements Agreement serves as a vital tool for organizations aiming to protect consumer credit data. This document defines the essential protocols and responsibilities involved in safeguarding consumer credit reports, ensuring user data privacy and security. It emphasizes the significance of a confidentiality agreement in preventing unauthorized access and misuse of sensitive information. A critical component of this agreement is the requirement for an Authorized Officer to sign, confirming organizational commitment to maintaining stringent security measures.
Purpose and Benefits of the Access Security Requirements Agreement
The agreement is pivotal in reinforcing the importance of securing sensitive data found in consumer reports against potential threats. By implementing this form, companies can experience various benefits, such as enhanced credit information security and adherence to relevant regulations. The Access Security Requirements Agreement also significantly contributes to preventing unauthorized access, ensuring that personal information remains confidential and protected from misuse.
Key Features of the Access Security Requirements Agreement
This agreement outlines essential measures that organizations must follow to uphold data protection standards. Key features include:
-
Specific protocols for securing sensitive consumer account information.
-
Access restrictions limiting exposure to key personnel only.
-
Record retention requirements aligning with the Federal Equal Opportunities Act.
These provisions collectively enhance the overall security landscape of organizations handling consumer credit data.
Who Needs the Access Security Requirements Agreement?
The Access Security Requirements Agreement is essential for various entities, particularly those managing consumer credit reports. Businesses such as financial institutions, credit bureaus, and any organization involved in credit reporting should utilize this form. An Authorized Officer plays a vital role in executing the agreement, ensuring compliance and accountability. Scenarios where this agreement is critical include handling sensitive credit information during sharing or storage processes.
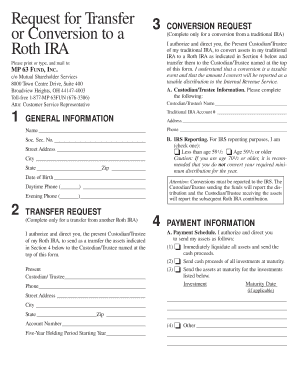
How to Fill Out the Access Security Requirements Agreement Online (Step-by-Step)
Filling out the Access Security Requirements Agreement online can be straightforward with the right steps. Follow this step-by-step guide:
-
Access the form on a secure platform like pdfFiller.
-
Gather all necessary information, including company details and Authorized Officer credentials.
-
Fill in the blank fields, ensuring accuracy in details entered.
-
Utilize fillable fields for seamless data entry.
-
Apply e-signature features to sign the document digitally.
By preparing in advance, the process becomes efficient and error-free.
Common Errors When Filling Out the Access Security Requirements Agreement
When completing the Access Security Requirements Agreement, users often encounter specific mistakes. Common errors include:
-
Omitting required fields, leading to incomplete forms.
-
Incorrectly entering the Authorized Officer's title or details.
To ensure a smooth process, it is advisable to follow a checklist that validates all fields and confirms the completeness of the submitted information.
How to Sign the Access Security Requirements Agreement
Understanding the signing process for the Access Security Requirements Agreement is essential. Notably, there are differences between traditional wet signatures and digital signatures. pdfFiller streamlines the eSigning process, incorporating robust security features for document integrity. Users should be aware of the procedures for submitting the signed agreement, whether electronically or through traditional methods.
Security and Compliance for the Access Security Requirements Agreement
Maintaining compliance with data protection regulations is crucial when handling the Access Security Requirements Agreement. Key aspects include:
-
Understanding the importance of adhering to legal standards for data security.
-
Overview of security features available through pdfFiller to ensure proper document handling.
-
Recognizing record retention and privacy protections enforced by this agreement.
These measures ensure ongoing compliance and heightened security for sensitive credit information.
Next Steps After Completing the Access Security Requirements Agreement
Once the Access Security Requirements Agreement is completed, users should consider the following next steps:
-
Select a submission method: electronic or mail, evaluating their respective implications.
-
Prepare for confirmation and tracking post-submission, understanding the follow-up processes.
-
Plan for potential amendments or renewals of the agreement as needed.
Understanding these processes aids in maintaining organizational compliance and data security moving forward.
Empower Your Business with pdfFiller for the Access Security Requirements Agreement
Leveraging pdfFiller for the Access Security Requirements Agreement enhances business efficiency. This platform offers user-friendly features that simplify the filling process, including editing capabilities and secure eSigning options. Users are encouraged to explore the robust functionalities of pdfFiller, ensuring effective document management while prioritizing security in handling sensitive agreements.
How to fill out the access security requirements agreement
-
1.Visit pdfFiller and search for the Access Security Requirements Agreement form in the template library.
-
2.Open the form and familiarize yourself with the layout, identifying sections for completion.
-
3.Before starting, gather required information such as the company name, authorized officer details, and any relevant access policies.
-
4.Begin filling out the form by entering your company name and the contact information of the authorized officer.
-
5.Proceed to input details in the fields provided for signature, print name, title, and date where required.
-
6.Double-check that all blank fields are appropriately filled, particularly sections outlining security measures and privacy policies.
-
7.Use pdfFiller's review feature to preview the form for any errors or missing entries.
-
8.Once the form is completed and verified, save your changes to preserve the entered information.
-
9.Choose to download the form in your preferred format for printing or electronic submission or follow any specific submission instructions provided within pdfFiller.

Who needs to sign the Access Security Requirements Agreement?
The agreement must be signed by an authorized officer of the company, as they are responsible for ensuring compliance with the outlined security measures.
Are there any eligibility requirements for this form?
Generally, any company handling consumer credit reports that needs to outline security requirements can use this form. Ensure you have an authorized officer ready to sign.
What is the process for submitting this form?
Once completed, the Access Security Requirements Agreement can be printed for physical submission or saved digitally for electronic record-keeping. Ensure all parties review before signing.
What common mistakes should be avoided when filling out this form?
Common mistakes include leaving blank fields, incorrect signature placements, and failing to enter the correct company information. Double-check all entries for accuracy.
How long should records of this form be kept?
Records should be maintained in accordance with the Federal Equal Opportunities Act, which may require retention for a defined period. Familiarize yourself with specific duration recommendations.
What information is needed before starting to fill out the form?
Gather your company name, contact information for the authorized officer, and detailed knowledge of your organization’s privacy protection policies before beginning.
Is notarization required for this agreement?
No, notarization is not required for the Access Security Requirements Agreement, but ensure that an authorized officer signs it to validate the content.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.