Last updated on Aug 12, 2014
Get the free Risk Assessment Form
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.
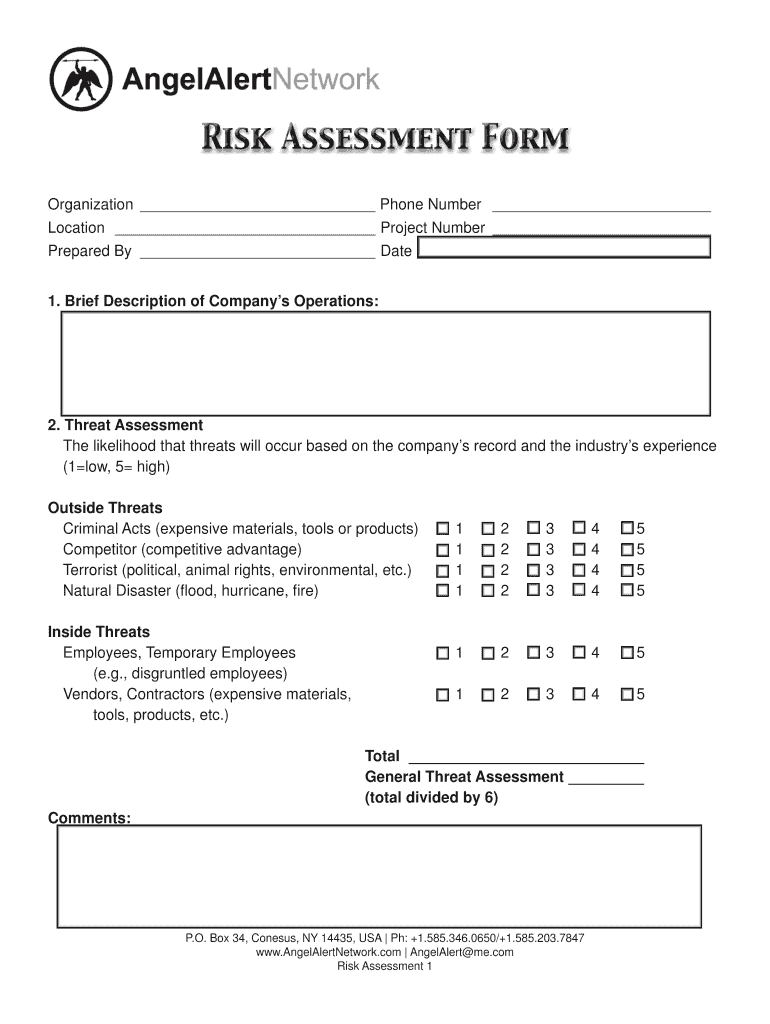
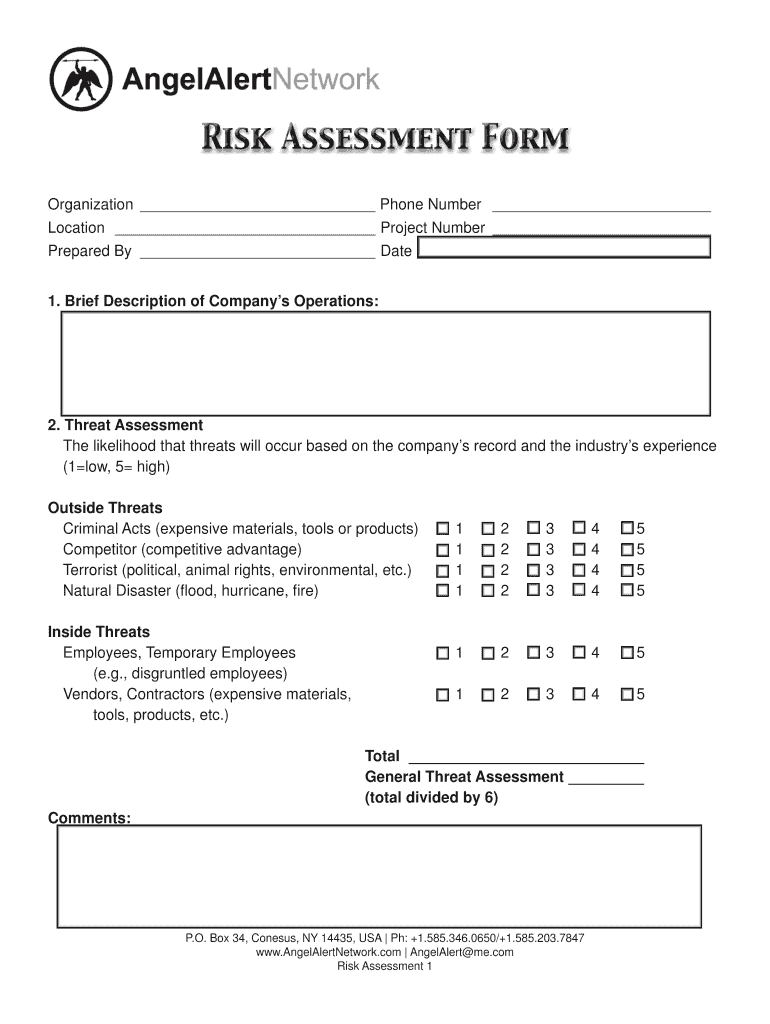
What is risk assessment form
The Risk Assessment Form is a business document used by organizations to evaluate potential threats and assess losses related to their operational security.
pdfFiller scores top ratings on review platforms




Who needs risk assessment form?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to risk assessment form
Understanding the Risk Assessment Form
The Risk Assessment Form is a critical tool used by organizations to evaluate potential threats and assess possible losses that may impact their operations. This form plays an important role in helping businesses understand their risk landscape, enabling them to implement security measures effectively. By methodically evaluating various threats and the potential financial impact, organizations can prioritize their response strategies to enhance overall security.
Additionally, the security measures evaluation process outlined in the form helps align business objectives with practical safeguards, ensuring comprehensive protection against identified risks.
Benefits of Using the Risk Assessment Form
Completing the Risk Assessment Form offers numerous advantages for improving organizational operations. It facilitates informed decision-making by providing essential data to assess security measures in place. This process not only identifies vulnerabilities and risks but also enhances the organization’s security strategy by pinpointing areas that require intervention.
-
Improved awareness of potential threats
-
Clear identification of mitigation strategies
-
Informed allocation of security resources
Who Should Complete the Risk Assessment Form
The Risk Assessment Form is essential for various key audiences. Businesses of all sizes in New York, as well as organizations assessing their security protocols and operations, should prioritize its completion. Specific roles, such as security officers and risk managers, are particularly well-suited for preparing the form to ensure thorough and accurate assessments.
How to Fill Out the Risk Assessment Form Online
To effectively complete the Risk Assessment Form using pdfFiller, follow these steps:
-
Access the form on the pdfFiller platform.
-
Fill out each section, paying attention to all required fields.
-
Review your inputs for consistency and accuracy.
-
Save your progress frequently.
-
Download and share the completed form as needed.
These steps ensure that the form is filled accurately and submitted without errors.
Key Features of the Risk Assessment Form
The Risk Assessment Form includes several important components and features that enhance its usability. It contains multiple fillable fields and checkboxes, allowing for a customizable approach to risk assessment. Additionally, it emphasizes the importance of signing the form prepared by the responsible party, which ensures accountability.
-
Clear instructions for completing each section
-
Ratings for threat and loss assessments
-
Space for notes and additional comments
Common Mistakes When Completing the Risk Assessment Form
While filling out the Risk Assessment Form, users should be aware of common pitfalls that can occur. Frequently overlooked fields or the inclusion of inconsistent information can lead to inaccurate assessments. Additionally, misunderstandings surrounding the rating system for threats and losses can compromise the assessment's reliability.
It's crucial to review the completed form thoroughly before submission to avoid such mistakes and ensure a comprehensive evaluation.
Submission Process for the Risk Assessment Form
Once the Risk Assessment Form is filled out, there are several submission methods available. Users can choose to submit the form online or via conventional mail. Each submission method may have specific requirements, so it's beneficial to check the guidelines provided by the intended recipient.
-
Ensure all required fields are completed before submission.
-
Keep records of the submission for tracking purposes.
-
Consider sending via a tracked postal method if submitting by mail.
Security and Compliance Considerations for the Risk Assessment Form
When handling the Risk Assessment Form, organizations must prioritize security and compliance. pdfFiller implements robust security measures, such as 256-bit encryption and adherence to SOC 2 Type II, HIPAA, and GDPR regulations, to protect sensitive information. Users are encouraged to follow best practices to maintain document integrity.
Proper handling of data ensures compliance with privacy standards and protects the organization from potential breaches.
Real-World Applications of the Risk Assessment Form
The Risk Assessment Form has versatile applications across various industries, showcasing its effectiveness in diverse settings. Case studies and feedback from organizations reveal the form's capability to enhance risk management practices strategically. These real-world examples demonstrate how businesses can modify the form to meet their unique needs while better identifying and mitigating risks.
Maximize Your Efficiency with pdfFiller
Utilizing pdfFiller for your risk assessment needs can significantly enhance your efficiency. The platform provides user-friendly features for editing and eSigning, making it easier to manage documents in a cloud-based environment. Many satisfied users have shared positive testimonials about how pdfFiller helped streamline their risk assessment processes and improve data management.
How to fill out the risk assessment form
-
1.To access the Risk Assessment Form on pdfFiller, navigate to the platform's website and use the search bar to locate the form by entering its name.
-
2.Once you find the form, click on it to open the document in pdfFiller's editing interface, where you will see fillable fields and checkboxes.
-
3.Before starting, gather all necessary information such as company operations, potential threats, risk ratings, loss assessments, and current security measures to ensure a complete and accurate form.
-
4.You can fill in the form by clicking on each field and typing the required information or marking checkboxes as needed. Use pdfFiller tools to add comments or notes if necessary.
-
5.As you complete the form, regularly review the entered information for accuracy and completeness to ensure that all details are correct before final submission.
-
6.Once the form is filled out, preview it to check for any errors, making adjustments if needed. This ensures everything is accurate and ready for submission.
-
7.When satisfied with the form, utilize the save feature in pdfFiller to store the document, or choose to download it to your device. You can also submit it directly through pdfFiller if there’s an option for that.

Who is eligible to use the Risk Assessment Form?
Any organization or business that requires an assessment of potential risks and security measures can utilize the Risk Assessment Form. This includes companies of all sizes, from small businesses to large enterprises.
What is the process for submitting the Risk Assessment Form?
After filling out the Risk Assessment Form on pdfFiller, you may have options to save it for your records, download it, or submit it via email. Follow the instructions provided on the platform for seamless submission.
Are there deadlines for completing the Risk Assessment Form?
While there are typically no fixed deadlines for filling out the Risk Assessment Form, it is recommended to complete it promptly to ensure corrective measures can be taken in a timely manner.
What supporting documents may be required with this form?
Supporting documents may include previous risk assessments, incident reports, and any other relevant security audits. Collect these documents to provide a comprehensive overview when completing the form.
What are common mistakes to avoid when filling out this form?
Common mistakes include omitting important details, failing to provide accurate ratings, and neglecting to review the form for errors. Always double-check your entries and ensure all fields are completed as instructed.
How long does it take to process the Risk Assessment Form?
Processing times can vary based on the organization reviewing the form. Typically, you should expect feedback within a few days to weeks, depending on the complexity of the assessment.
Is notarization required for the Risk Assessment Form?
No, notarizing the Risk Assessment Form is not required, but it must be signed by the individual who prepared it, ensuring accountability and accuracy in the assessment provided.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.