Last updated on Aug 30, 2014

Get the free Identity Theft Victim’s Packet
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is identity formft victims packet
The Identity Theft Victim’s Packet is a legal form used by victims in Minnesota to report and address identity theft and fraudulent activities.
pdfFiller scores top ratings on review platforms




Who needs identity formft victims packet?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to identity formft victims packet
What is the Identity Theft Victim’s Packet?
The Identity Theft Victim’s Packet serves as a crucial resource for individuals in Minnesota who have fallen victim to identity theft. This packet helps victims navigate the complicated process of reporting and addressing fraudulent activities. By utilizing the identity theft packet, victims can streamline their efforts to rectify their situation and seek legal recourse.
It is essential for anyone affected by identity theft to understand the value of this packet. It not only offers guidance on actions to take but also provides necessary documentation to report incidents effectively, thus ensuring a more manageable recovery process.
Purpose and Benefits of the Identity Theft Victim’s Packet
The primary purpose of the Identity Theft Victim’s Packet is to provide legal support for victims as they address the consequences of their identity being stolen. The packet offers a comprehensive toolkit that includes various forms and templates necessary for effective communication with the Cloquet Police Department and credit bureaus.
Key benefits of using this packet include:
-
A clear outline for managing the aftermath of identity theft.
-
Access to a fraud alert form to notify creditors.
-
Templates for an identity theft affidavit, which can be crucial for legal processes.
-
Resources for a victim prosecution packet to consider pursuing further legal action.
Key Features of the Identity Theft Victim’s Packet
The Identity Theft Victim’s Packet is designed with several essential components to assist victims effectively. It includes a variety of templates that serve specific purposes in the recovery process.
These key features encompass:
-
Identity Theft Affidavits to formally declare the theft.
-
Letters of Dispute to challenge fraudulent charges.
-
FACTA law information explaining the rights of victims regarding credit reporting.
-
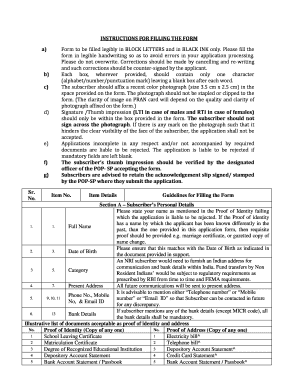
Instructions for filling out necessary forms, including specific fields like the ICR #.
Who Needs the Identity Theft Victim’s Packet?
Determining who would benefit from the Identity Theft Victim’s Packet is vital for effective outreach. Any individual who has experienced identity theft, regardless of the context, qualifies as a victim needing this information. Situations might include unauthorized use of personal information, accounts opened in someone else's name, or compromised financial transactions.
This packet ultimately aims to assist anyone affected by identity theft, providing them with important resources to counteract the effects of this crime.
How to Fill Out the Identity Theft Victim’s Packet Online
Completing the Identity Theft Victim’s Packet can be efficiently done online using pdfFiller. Users can follow these simple steps to ensure completeness and accuracy:
-
Open the pdfFiller platform and access the Identity Theft Packet form.
-
Fill in the required fields, paying close attention to detail.
-
Utilize tools for adding signatures and ensuring all sections are completed.
-
Review your entries to confirm information is correct before submission.
By adhering to these steps, users can navigate the filling process smoothly, minimizing errors during form completion.
Common Errors and How to Avoid Them
When filling out the Identity Theft Victim’s Packet, users often encounter common pitfalls that can delay processing. Understanding these frequent errors is vital to ensure a flawless submission.
Common mistakes include:
-
Leaving blank fields that are required for proper processing.
-
Inaccurately filling out the identity theft affidavit.
-
Underestimating the importance of including all relevant documentation.
Reviewing each form thoroughly before submission can help avoid these mistakes, facilitating a quicker resolution process with creditors and authorities.
Submission Methods and Delivery
Once the Identity Theft Victim’s Packet is completed, it’s essential to submit it correctly. Victims have various methods to choose from depending on their preferences and local guidelines.
Methods of submission include:
-
Submitting online through affiliated services.
-
Mailing a printed version of the packet to the appropriate agencies.
-
Delivering the packet in person at designated offices.
Tracking submissions can also provide peace of mind, so it's advisable to note confirmation details or expected processing times upon submission.
What Happens After You Submit the Identity Theft Victim’s Packet?
After submitting the Identity Theft Victim’s Packet, several processes will follow as authorities begin to review the submitted documentation. Victims can expect communication regarding their filing status shortly.
Possible outcomes after submission may include:
-
Notifications of any additional steps needed for resolution.
-
Updates on the progress of identity theft cases.
-
Opportunities to appeal decisions if submissions are initially rejected.
Being aware of these processes can help victims navigate the next steps with clarity and confidence.
Security and Compliance When Using the Identity Theft Victim’s Packet
When dealing with sensitive personal information, security is paramount. Using pdfFiller to fill out and submit the Identity Theft Victim’s Packet ensures that user data remains protected throughout the process.
pdfFiller employs strong security measures, including:
-
256-bit encryption to safeguard information.
-
SOC 2 Type II compliance for data handling protocols.
-
Compliance with HIPAA and GDPR regulations for user privacy.
This commitment to security helps victims feel confident that their information is safe and compliant with legal requirements as they navigate their recovery.
Your Next Steps with pdfFiller
For those ready to take action, utilizing pdfFiller for completing the Identity Theft Victim’s Packet can streamline the process. The platform features an array of tools specifically designed to assist users in managing their documentation efficiently.
Users can take advantage of pdfFiller’s functionalities, such as:
-
Creating fillable forms suited to individual needs.
-
Organizing and managing documents in one secure location.
-
eSigning documents for quicker processing times.
With pdfFiller, users can ensure that they are well-prepared to tackle the challenges that come with identity theft.
How to fill out the identity formft victims packet
-
1.Access and open the Identity Theft Victim’s Packet on pdfFiller by searching for the form name in the search bar.
-
2.Once the form is open, familiarize yourself with the layout, which includes sections for personal information and applicable templates.
-
3.Refer to the instructions included in the packet to gather necessary documentation, such as police reports, identification, and details of fraudulent activity.
-
4.Complete the blank fields in the form, including your personal information and specific details related to the identity theft incident.
-
5.Utilize pdfFiller’s editing tools to fill out checkboxes and other sections, ensuring all required information is accurately provided.
-
6.After completing all fields, review the entire form for accuracy and completeness before moving to the submission phase.
-
7.Once satisfied, save your work using the 'Save' feature, ensuring you have a secure copy of your completed form.
-
8.To submit the form, download it to your device or use pdfFiller’s submission options to send it directly to the intended recipient.

Who is eligible to use the Identity Theft Victim’s Packet?
Any individual who has experienced identity theft in Minnesota can utilize the Identity Theft Victim’s Packet to report incidents and seek resolution.
Are there any deadlines for submitting this form?
While the packet itself does not have a strict deadline, it's recommended that victims report identity theft as soon as possible to prevent further fraudulent activities.
What methods are available for submitting the completed form?
The completed Identity Theft Victim’s Packet can be submitted directly to the Cloquet Police Department or relevant credit bureaus, depending on the nature of the identity theft.
What supporting documents are needed to complete the packet?
You'll need identification, any relevant police reports, and details regarding the fraudulent activities, such as account statements and correspondence with creditors.
What common mistakes should I avoid when filling out the packet?
Ensure all information is accurate, double-check for missing fields, and avoid providing incomplete or vague descriptions of the fraudulent activities.
How long does it take to process identity theft claims with this form?
Processing times can vary depending on the agency handling your claim, but most authorities aim to address reports within a few weeks.
Is notarization required for the Identity Theft Victim’s Packet?
No, notarization is not required for this packet, but make sure to check for any additional requirements from the entities receiving your report.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.