Last updated on Aug 4, 2014

Get the free High-Tech Abuse and Stalking Log
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is High-Tech Stalking Log
The High-Tech Abuse and Stalking Log is a personal legal document used by survivors of high-tech domestic violence and stalking to document incidents for safety planning and legal actions.
pdfFiller scores top ratings on review platforms




Who needs High-Tech Stalking Log?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to High-Tech Stalking Log
What is the High-Tech Abuse and Stalking Log?
The High-Tech Abuse and Stalking Log is a crucial tool designed for victims of high-tech abuse and stalking. It serves as a comprehensive abuse documentation form that allows individuals to record incidents for legal and safety purposes. This log assists in documenting various forms of high-tech abuse, including detailed accounts that can be later referenced in legal contexts.
By maintaining a thorough log, survivors can provide vital information to law enforcement or legal authorities when necessary. This resource is also commonly referred to as a “stalking evidence log” or “domestic violence log,” highlighting its relevance across different abuse scenarios.
Purpose and Benefits of Using the High-Tech Abuse and Stalking Log
Using the High-Tech Abuse and Stalking Log has numerous practical benefits for survivors. Documenting incidents is essential for safety planning and can prove invaluable in potential legal actions. The log acts as an effective communication tool between victims and law enforcement, as well as healthcare providers, ensuring that all pertinent information is readily accessible.
Moreover, maintaining a structured way to document experiences can offer emotional relief and a sense of control for survivors. The act of filling out the log helps victims articulate their situations clearly, providing them with a tangible record of incidents that may otherwise feel overwhelming.
Key Features of the High-Tech Abuse and Stalking Log
The High-Tech Abuse and Stalking Log includes several key features designed to facilitate user experience. It contains fillable fields where users can enter important details such as date, time, and location of incidents, along with descriptions of each event.
-
Fillable fields for logging specific incident details.
-
Checkbox options for responses, such as police involvement or medical visits.
-
User-friendly design for effortless documentation.
These elements ensure that the log is both accessible and effective for users documenting their experiences.
Who Needs the High-Tech Abuse and Stalking Log?
The primary users of the High-Tech Abuse and Stalking Log are victims of high-tech abuse or stalking. This tool is particularly beneficial for individuals facing various forms of domestic violence who require a systematic way to document their experiences.
Contextually, this log can be advantageous for those experiencing harassment via technology, whether through stalking behaviors or direct threats. Its practical application can provide necessary support and may play an essential role in the safety and recovery of victims.
How to Fill Out the High-Tech Abuse and Stalking Log Online (Step-by-Step)
Filling out the High-Tech Abuse and Stalking Log online involves several straightforward steps. Begin by accessing the designated form and following these instructions:
-
Input the date and time of the incident in the specified fields.
-
Enter the location where the incident occurred for accurate documentation.
-
Provide a clear description of the event you wish to document.
-
Select checkboxes relevant to any police reports or medical consultations.
-
Review all entries for accuracy before final submission.
These steps ensure thorough documentation while minimizing common pitfalls, leading to a more effective log completion.
Submission Methods and What Happens After You Submit
Once the High-Tech Abuse and Stalking Log is completed, there are various submission methods available. Users can submit the log online or choose to deliver it in person, depending on their preferences and circumstances.
After submission, individuals can expect updates on the processing timeline. Depending on the authority or organization receiving the log, feedback may be communicated promptly. If applicable, users may have the option to track their submissions to ensure their documentation has been received and is being processed.
Security and Privacy When Using the High-Tech Abuse and Stalking Log
Ensuring the security and privacy of sensitive information is paramount when using the High-Tech Abuse and Stalking Log. Various security measures, including encryption protocols, are in place to protect data entered into the log.
Moreover, the log adheres to privacy standards such as HIPAA and GDPR, reinforcing the importance of confidentiality for those documenting their experiences of abuse. Users can feel secure knowing that their information is handled with the utmost care and consideration.
How pdfFiller Helps You Fill Out the High-Tech Abuse and Stalking Log
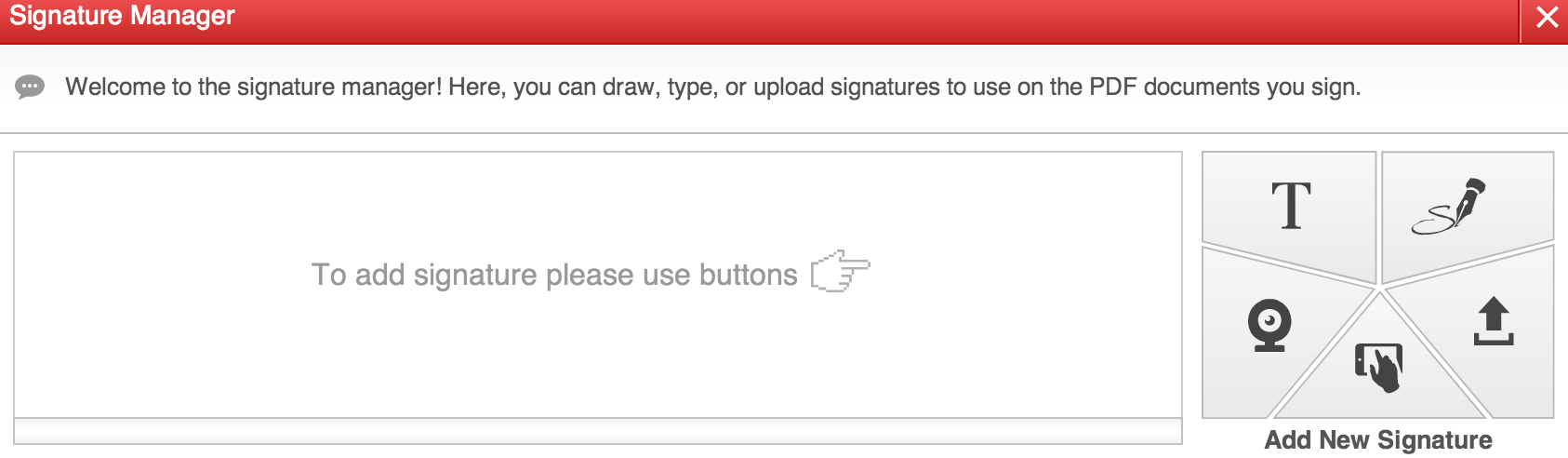
pdfFiller enhances the experience of filling out the High-Tech Abuse and Stalking Log through its user-friendly platform. Users can easily fill, sign, and submit the log without needing to download any software.
Key features of pdfFiller include the ability to edit, save, and securely share documents. These functionalities streamline the documentation process, allowing victims to leverage pdfFiller as a supportive tool in addressing their situations and effectively documenting their experiences.
Example or Sample of a Completed High-Tech Abuse and Stalking Log
Providing a sample of a completed High-Tech Abuse and Stalking Log can significantly assist users in understanding how to accurately fill out the form. A filled-out log can include annotations that guide individuals in documenting their experiences properly.
In this example, various scenarios related to high-tech abuse are depicted, allowing users to relate the entries to their own situations. Each entry serves as a reference point, demonstrating how to correlate personal experiences with specific fields in the log.
How to fill out the High-Tech Stalking Log
-
1.Access the High-Tech Abuse and Stalking Log by visiting pdfFiller and searching for the form by its name.
-
2.Open the form in the pdfFiller interface to begin filling it out. Familiarize yourself with the layout and features available for editing.
-
3.Before starting, gather all necessary information such as dates, times, locations, descriptions of incidents, and any evidence you have that supports your documentation.
-
4.Begin filling out the top section of the form with your personal information, ensuring accuracy in names and contact details.
-
5.Move to the incident logging sections. Use the fillable fields to input details about each incident, including the date, time, location, and descriptions.
-
6.Utilize any checkboxes provided to mark specific incidents or evidence that may be relevant for legal actions or safety planning.
-
7.Review the information filled in to ensure completeness and clarity, correcting any incorrect details or typos.
-
8.Once you are satisfied with the entries, finalize the form by saving your progress within pdfFiller.
-
9.To save, download, or share your completed form, use the available options in the pdfFiller menu, selecting your preferred method for submission or storage.

Who can utilize the High-Tech Abuse and Stalking Log?
This form is specifically designed for survivors of high-tech domestic violence and stalking, along with legal advocates and professionals who support these individuals.
Are there any deadlines for completing the form?
There are no specific deadlines for filling out the High-Tech Abuse and Stalking Log. It should be completed whenever incidents occur, particularly if legal actions are being considered.
How do I submit the High-Tech Abuse and Stalking Log once completed?
You can submit the High-Tech Abuse and Stalking Log electronically through pdfFiller or download it for printing. Ensure to follow submission guidelines required by any legal bodies involved.
What supporting documents do I need to accompany the form?
While not mandatory, accompanying evidence such as police reports, medical documents, or witness statements can enhance the validity of your report and should be submitted when relevant.
What common mistakes should I avoid when filling out this form?
Ensure that all fields are accurately filled and double-check dates and incident details. Common mistakes include leaving fields blank or providing unclear descriptions.
What is the typical processing time for this type of documentation?
The processing time can vary depending on the legal actions pursued. Keeping thorough records using this log can expedite any investigations or legal proceedings.
Can someone else fill out the form on my behalf?
Yes, someone can assist in completing your High-Tech Abuse and Stalking Log; however, it is crucial that all information provided is accurate and true to your experiences.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.