Last updated on Sep 12, 2014

Get the free EMSTARS End User Security Policy
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is EMSTARS Security Policy
The EMSTARS End User Security Policy is a healthcare form used by EMS providers in Florida to secure and protect patient and provider information.
pdfFiller scores top ratings on review platforms




Who needs EMSTARS Security Policy?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to EMSTARS Security Policy
What is the EMSTARS End User Security Policy?
The EMSTARS End User Security Policy is a crucial document designed to safeguard the integrity of patient and Emergency Medical Services (EMS) provider information. This Florida EMS security policy outlines the necessary guidelines and protocols that ensure the security of sensitive information.
Its significance lies in meeting the demands of healthcare regulations while promoting a secure environment for sharing essential data. Thus, adherence to the EMSTARS security policy not only protects individual patient data but also fosters trust between patients and healthcare providers.
Purpose and Benefits of the EMSTARS End User Security Policy
The EMSTARS End User Security Policy serves multiple purposes that are vital for both end users and agencies. Primarily, it ensures compliance with healthcare regulations, protecting sensitive patient data and agency information.
Additionally, by implementing this patient data security form, EMS providers can establish a trustworthy relationship with their clients. This mutual trust is fundamental for effective healthcare delivery and reinforces the importance of the EMS end user agreement.
Key Features of the EMSTARS End User Security Policy
This form contains several essential components that must be completed accurately. Required fields include the end user's name, signature, date, agency details, and other relevant identifying information.
It is important for both end users and agency key users to provide accurate information, as discrepancies could lead to compliance issues. Understanding the signature requirements ensures that the EMSTARS end user agreement is valid and recognized.
Who Needs to Complete the EMSTARS End User Security Policy?
The responsibility of completing the EMSTARS End User Security Policy falls on specific roles within the agency. The following individuals must sign the form:
-
End User
-
Agency Key User
Each role carries unique responsibilities, crucial for maintaining compliance with the policy. End users engage directly with the information, while agency key users oversee the proper submission and management of security protocols.
How to Fill Out the EMSTARS End User Security Policy Online (Step-by-Step)
Filling out the EMSTARS End User Security Policy online is a straightforward process when using platforms like pdfFiller. Follow these steps for seamless completion:
-
Access the form through pdfFiller.
-
Complete the required fields accurately.
-
Validate the information provided before submission.
-
Utilize pdfFiller’s features for editing and eSigning.
Proactive validation ensures that all details are correct, minimizing the risk of errors before submission.
Submitting the EMSTARS End User Security Policy
After completing the form, it is essential to understand the submission process. Users must submit the finished document to the Bureau of EMS Data Unit through appropriate channels.
Submission methods include both digital options and traditional mail. Once submitted, users should keep track of their submission status to confirm receipt by the Bureau.
Security and Compliance Considerations for the EMSTARS End User Security Policy
Ensuring security and compliance is critical when dealing with sensitive information contained in the EMSTARS End User Security Policy. The form utilizes advanced security features, such as encryption, to protect data integrity.
This policy complies with established regulations like HIPAA and GDPR, which is essential for safeguarding patient information. Utilizing pdfFiller facilitates secure document handling, ensuring that all submissions adhere to compliance standards.
Getting Help with the EMSTARS End User Security Policy
Users who need assistance can greatly benefit from the customer support options available through pdfFiller. The platform offers tools that facilitate the editing and eSigning of the EMSTARS End User Security Policy.
Accessibility to these resources emphasizes the ease of use and encourages users to fully leverage the capabilities of pdfFiller for their document needs.
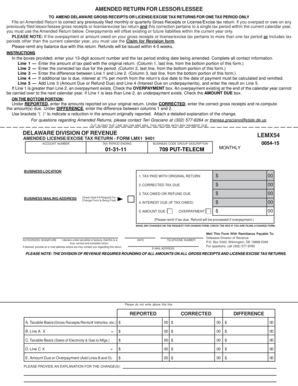
Sample of a Completed EMSTARS End User Security Policy
Providing a visual reference can significantly aid users in completing their forms accurately. A correctly filled out EMSTARS End User Security Policy showcases the essential fields and required signatures.
Additionally, it is beneficial to highlight common errors to avoid during completion, ensuring the submission meets all required standards.
Your Next Steps with pdfFiller
Engaging with pdfFiller to fill out the EMSTARS End User Security Policy opens the door to a more efficient document management experience. This platform offers numerous benefits, including secure document handling and tools for editing and eSigning.
Start utilizing pdfFiller’s comprehensive features to streamline your form filling needs effectively.
How to fill out the EMSTARS Security Policy
-
1.To begin, access pdfFiller and search for 'EMSTARS End User Security Policy' to locate the form.
-
2.Once opened, review the instruction and fillable fields present in the document on your screen.
-
3.Prepare the required information: end user's name, signature, date, EMSTARS user name, agency name, and agency ID.
-
4.Click on each field to enter the necessary details, ensuring accuracy as you proceed.
-
5.Both the end user and agency key user must sign. Utilize the signature tool to electronically sign in the designated areas.
-
6.After completing all fields, take a moment to review the entire form for any errors or missing information.
-
7.Once satisfied with the entries, make use of the options to save, download, or submit the form via pdfFiller.

Who is eligible to fill out the EMSTARS End User Security Policy?
Eligible individuals include EMS end users and agency key users who are responsible for ensuring data security within their organization.
Is there a deadline for submitting this security policy form?
While specific deadlines may vary, it's recommended to submit the form as soon as possible to maintain compliance with EMS data security requirements.
How do I submit the completed EMSTARS form?
After filling out the EMSTARS form on pdfFiller, you can submit it electronically through the platform, or download it to submit via mail or email if required.
What supporting documents are needed with this form?
Typically, no additional supporting documents are required with the EMSTARS form, but ensure all required fields are completed accurately.
What are common mistakes to avoid when filling out the form?
Common mistakes include forgetting to sign, leaving mandatory fields blank, or entering incorrect agency information. Double-check all entries for accuracy.
How long does the processing of this form take?
Processing times vary by agency; however, it’s advisable to allow a few days for any internal approvals or confirmations post-submission.
What happens if I do not comply with the security policy requirements?
Failure to comply with the security policy can result in penalties, regulatory actions, or denial of access to EMS data systems.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.