Last updated on Sep 20, 2014

Get the free Computer Security Self-Assessment Checklist
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is Security Self-Assessment Checklist
The Computer Security Self-Assessment Checklist is a business form used by organizations to evaluate the security of their computer systems.
pdfFiller scores top ratings on review platforms




Who needs Security Self-Assessment Checklist?
Explore how professionals across industries use pdfFiller.
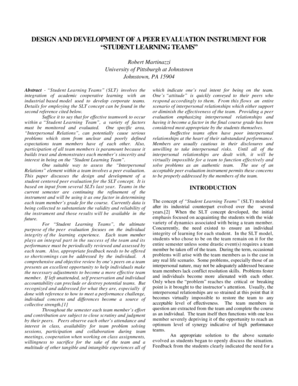
Comprehensive Guide to Security Self-Assessment Checklist
What is the Computer Security Self-Assessment Checklist
The Computer Security Self-Assessment Checklist is a valuable tool for evaluating the security of computer systems. It serves the essential purpose of identifying vulnerabilities and assessing various security aspects. By using a YES/NO format, users can score their responses and gain insights into their security posture.
-
The checklist focuses on key areas such as physical security and disaster recovery.
-
It helps organizations enhance security awareness and implement proactive measures.
Purpose and Benefits of the Computer Security Self-Assessment Checklist
This checklist is crucial for proactive security assessment, especially for businesses. It allows users to pinpoint vulnerabilities and significantly enhance their overall security posture.
-
Regular assessments lead to improved disaster recovery strategies.
-
It identifies weaknesses before they can be exploited.
Key Features of the Computer Security Self-Assessment Checklist
Designed with user-friendliness in mind, the checklist encompasses detailed sections covering numerous security areas such as confidentiality and virus protection.
-
The format provides clear instructions to aid users in completing the assessment accurately.
-
An effective scoring mechanism enables quick evaluations and guidance on necessary actions.
Who Needs the Computer Security Self-Assessment Checklist
The checklist is beneficial for a variety of users, including businesses, IT departments, and freelancers. Each group can leverage this tool to conduct valuable security self-assessments.
-
Organizations can use it for compliance and risk management.
-
Freelancers benefit from understanding security needs specific to their operations.
How to Fill Out the Computer Security Self-Assessment Checklist Online
Completing the checklist online is a straightforward process. First, users need to access the form through pdfFiller’s platform.
-
Follow the guidelines for filling out each field accurately.
-
Use examples provided to ensure clarity in responses.
-
Check for accurate scoring to enhance the effectiveness of your assessment.
Submission and Filing Instructions for the Computer Security Self-Assessment Checklist
After completing the checklist, users have multiple submission options. They can choose between electronic submission and traditional paper submission based on convenience.
-
Important deadlines and tracking methods for submitted forms help ensure compliance.
-
Users can save, download, and print the checklist easily from pdfFiller.
Common Mistakes to Avoid When Using the Computer Security Self-Assessment Checklist
While using the checklist, users should be mindful of common errors that can undermine their assessments. Frequent inaccuracies in responses can lead to misleading scores.
-
Double-checking for accuracy in responses is crucial.
-
Regularly updating the checklist helps maintain ongoing evaluations.
How pdfFiller Enhances Your Experience with the Computer Security Self-Assessment Checklist
pdfFiller provides key advantages for users completing the Computer Security Self-Assessment Checklist. Its features streamline form completion effectively.
-
eSigning and editing capabilities enhance the user experience.
-
Strong security measures ensure confidentiality throughout the process.
Ensuring Compliance and Security with the Computer Security Self-Assessment Checklist
Data protection and compliance are paramount when using the checklist. It is essential to consider the implications of regulations such as HIPAA and GDPR regarding data security.
-
Best practices for maintaining data integrity must be followed during assessments.
-
Keeping records of completed assessments aids in compliance verification.
Get Started Today with the Computer Security Self-Assessment Checklist
Users are encouraged to access the checklist through pdfFiller’s platform to begin their security evaluations. Proactive assessment plays a critical role in enhancing and maintaining computer security.
-
Resources for further support in completing the assessment are available.
How to fill out the Security Self-Assessment Checklist
-
1.Access the Computer Security Self-Assessment Checklist on pdfFiller by searching for the form in the platform’s search bar or browsing the business forms category.
-
2.Open the form in pdfFiller’s editing interface for easy navigation.
-
3.Read through the provided instructions to familiarize yourself with the YES/NO questions and sections before you start filling it out.
-
4.Gather all necessary information regarding your current security measures, including physical security, disaster recovery plans, and virus protection strategies.
-
5.Begin answering each question, selecting YES or NO based on your assessment of the system's strengths and weaknesses.
-
6.As you complete each section, check your answers for accuracy and completeness.
-
7.Once all questions are answered, review the checklist to ensure you have considered all aspects of your computer security.
-
8.Refer to the provided recommendations for each section on scoring and potential improvements.
-
9.Finalize the form by saving your progress regularly to avoid data loss.
-
10.To save or download the completed checklist, click on the 'Save' or 'Download' options in the pdfFiller toolbar.
-
11.If you intend to submit the form electronically, follow the submission process provided through pdfFiller, ensuring you have included all required information.

Who should fill out the Computer Security Self-Assessment Checklist?
The Computer Security Self-Assessment Checklist is ideal for businesses, IT professionals, and compliance officers. Anyone responsible for assessing or improving an organization's computer security measures can benefit from using this form.
Is there a specific deadline for completing the checklist?
There is no fixed deadline for the Computer Security Self-Assessment Checklist. However, regular assessments are recommended, especially before audits or security reviews.
How do I submit the completed checklist?
Upon completing the checklist on pdfFiller, you can either download it for your records or submit it electronically. Follow the submission prompts in pdfFiller to share the form with relevant stakeholders.
What supporting documents do I need to complete the checklist?
No specific supporting documents are required to complete the Computer Security Self-Assessment Checklist. However, having information about your current security measures and policies will assist you in providing accurate responses.
What are common mistakes to avoid when filling out this checklist?
Common mistakes include overlooking important security aspects or rushing through the YES/NO questions. Make sure to review each section thoroughly to ensure all areas are assessed accurately.
How long does it take to complete the Computer Security Self-Assessment Checklist?
The completion time can vary based on the organization's size and the complexity of its security measures. On average, expect to spend at least 30 minutes to thoroughly evaluate all sections.
Can this form be notarized?
No, the Computer Security Self-Assessment Checklist does not require notarization as it is used primarily for internal evaluations of security practices.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.