Last updated on Feb 12, 2015

Get the free Identity Theft Prevention Program Compliance Model
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is Identity Theft Prevention Program
The Identity Theft Prevention Program Compliance Model is a legal document used by U.S. utilities to comply with the FTC's Identity Theft Red Flag Rule and establish policies for preventing identity theft.
pdfFiller scores top ratings on review platforms




Who needs Identity Theft Prevention Program?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to Identity Theft Prevention Program
What is the Identity Theft Prevention Program Compliance Model?
The Identity Theft Prevention Program Compliance Model serves to help water and wastewater utilities adhere to the FTC's Identity Theft Red Flag Rule. This compliance model encompasses essential policies and procedures that facilitate the detection and prevention of identity theft. Understanding this compliance model is vital for enhancing the overall security framework within these utilities.
Its primary role is to define the components necessary for compliance, outlining the scope and significance of identity theft prevention programs. By employing this structured approach, utilities can effectively safeguard against identity theft and mitigate associated risks.
Purpose and Benefits of the Identity Theft Prevention Program Compliance Model
The Identity Theft Prevention Program Compliance Model offers utilities a robust methodology for identifying and reducing identity theft risks. This includes a comprehensive guide on essential policies and procedures needed to both detect potential threats and mitigate their impacts.
Key benefits include:
-
Systematic risk assessment strategies that enhance overall security.
-
Structured approaches to fraud prevention, ensuring utility protection.
-
Improved management of identity theft incidents, reducing financial and reputational damage.
Key Features of the Identity Theft Prevention Program Compliance Model
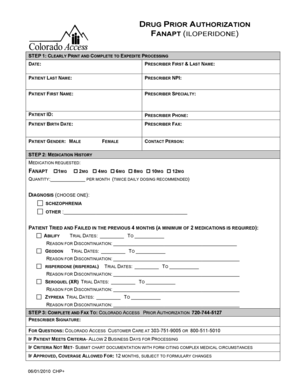
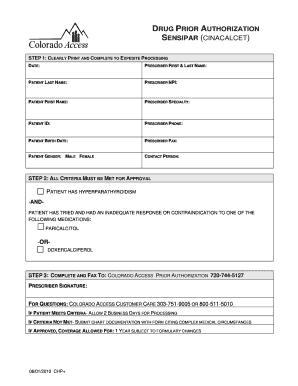
This compliance model includes various components tailored to facilitate user engagement and compliance tracking. Each section of the form is designed to capture critical information, which aids in the effective implementation of identity theft prevention strategies.
Key features include:
-
Sections for contact information and comprehensive risk assessments.
-
Blank fields and checkboxes that guide user input and data collection.
-
Response procedures tailored for flagged identity theft risks.
Who Needs the Identity Theft Prevention Program Compliance Model?
The compliance model is essential for specific roles within water and wastewater utilities, particularly Senior Management and Governing Body Members. These stakeholders are vital in ensuring that the organization's compliance with identity theft prevention measures is upheld.
Utilities across West Virginia and the broader U.S. must prioritize this model to effectively manage and respond to identity theft risks, emphasizing the importance of collaboration and immediate action in compliance efforts.
How to Fill Out the Identity Theft Prevention Program Compliance Model Online
Completing the compliance model requires attention to detail and adherence to specific guidelines. Follow these steps to fill out the form accurately:
-
Input data in the designated fields, ensuring clarity and correctness.
-
Check the appropriate boxes when identifying risk factors.
-
Conduct thorough risk assessments and identify potential detection red flags.
-
Validate all information to ensure accuracy before submission.
Submission and Compliance Requirements for the Identity Theft Prevention Program Compliance Model
After completing the compliance model, users must adhere to submission guidelines to ensure regulatory compliance. This process involves:
-
Identifying the correct submission location for the finished model.
-
Understanding the timelines involved in submission and compliance deadlines.
-
Gathering any required supporting documents that must accompany the submission.
Security Measures for Protecting Identity Theft Prevention Program Compliance Data
Security is paramount when using the compliance model, especially regarding sensitive data. Utilizing platforms such as pdfFiller can significantly enhance data protection.
Security measures include:
-
256-bit encryption for safeguarding confidential information.
-
Adherence to HIPAA and GDPR standards to maintain compliance.
-
Regular audits and security assessments to ensure ongoing protection.
Common Errors and How to Avoid Them While Filling Out the Compliance Model
While filling out the compliance model, users often encounter common pitfalls. Being aware of these can reduce errors and streamline the process.
To minimize mistakes, consider the following tips:
-
Review the form multiple times to catch missed information.
-
Ensure all required fields are completed accurately.
-
Double-check specific details like contact information to prevent discrepancies.
Explore pdfFiller's Tools for Efficiently Completing the Identity Theft Prevention Program Compliance Model
pdfFiller offers numerous tools that streamline the completion of the compliance model, thus enhancing the user experience. Features include:
-
Text and image editing capabilities that simplify content updates.
-
eSigning functionalities for quick approvals and confirmations.
-
Document management tools that enhance overall efficiency in handling forms.
Get Started with the Identity Theft Prevention Program Compliance Model Today
Users are encouraged to utilize pdfFiller to access and complete the Identity Theft Prevention Program Compliance Model. This platform not only simplifies the document completion process but also emphasizes the importance of proactive measures against identity theft.
Embrace a structured approach today to ensure compliance and protect sensitive information effectively.
How to fill out the Identity Theft Prevention Program
-
1.Access pdfFiller and search for 'Identity Theft Prevention Program Compliance Model' to open the form.
-
2.Once open, review the document layout to familiarize yourself with the sections and fields that require your input.
-
3.Before you fill out any fields, gather necessary information such as your utility’s contact details, risk assessment data, and any existing identity theft policies.
-
4.Begin filling in the form by entering your name, title, and phone number in the designated fields as specified.
-
5.Pay attention to the checkboxes for risk assessment and detection red flags. Select or deselect items based on your utility's specific situation.
-
6.Continue by completing the risk assessment section, ensuring that you accurately assess and document potential identity theft risks your utility faces.
-
7.Follow up with the detection red flags section, where you should highlight any specific indicators that might suggest fraudulent activity.
-
8.Complete the response procedures section by clearly outlining how your utility will respond to detected identity theft scenarios.
-
9.Review the filled form thoroughly, checking for any missing information or errors.
-
10.Once satisfied with the completed form, use pdfFiller’s save function to store a copy on your device.
-
11.Download the form in your preferred format or directly submit it through pdfFiller if that option is available.

Who is eligible to use the Identity Theft Prevention Program Compliance Model?
This compliance model is designed for all water and wastewater utilities across the United States that are required to comply with the FTC's Identity Theft Red Flag Rule.
What happens if I miss the compliance deadline?
While the formal compliance deadline was November 1, 2008, utilities should still establish a compliance program to minimize legal risks and ensure best practices for identity theft prevention.
How do I submit the completed form?
You can submit the completed form through pdfFiller’s submission features, or print it and send it to relevant governing bodies as guided within the document.
What supporting documents do I need?
While the form itself does not require additional documents, completing it may necessitate references to existing policies, risk assessments, and potential fraud detection measures already implemented.
What common mistakes should I avoid while filling out the form?
Ensure all fields are completed accurately, particularly the risk assessment sections, as incomplete forms may not meet compliance standards, potentially jeopardizing your utility's protections.
How long does it take to process the completed compliance model?
Processing times can vary based on the reviewing body but completing the form itself should take approximately 1-2 hours, depending on the complexity of your utility's practices.
Are there fees associated with using this form?
There are typically no fees for completing the form itself, but any associated legal or consultation fees should be considered when ensuring comprehensive compliance.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.