Last updated on Apr 10, 2026

Get the free Identity Theft By Known Imposter Package
We are not affiliated with any brand or entity on this form
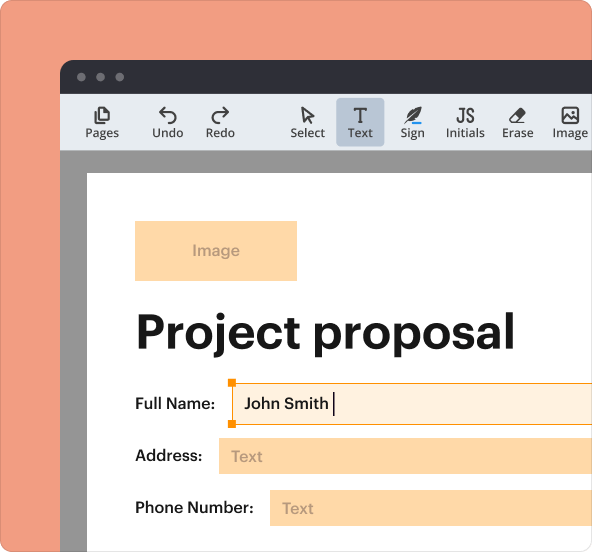
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is identity formft by known
The Identity Theft By Known Imposter Package is a set of legal documents designed for victims of identity theft by known imposters to address and remedy the effects of such theft.
pdfFiller scores top ratings on review platforms




I had a quick need to make some changes to a PDF. I found your application and it worked immediately. I want to learn more about these other features.
It was good but I don't need it any more
Very good experience so far. I've only used this for 1 day. But would like to learn more features.
NOT ALWAYS EASY TO N=KNOW WHAT TO DO NEXT
No issues once I contacted the support department who answered my questions. I understand that you are in business to make money on a service. I just felt it was costly for a piece of paper or two that would cost me 10. Cents at a FedEx or Office Max type business.
I love the ease of typing on the PDF, I'm still learning how to send it to others with fill in blanks. But I like it. Pricey for the redaction ability but I suppose better than Adobe
Who needs identity formft by known?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to identity formft by known
What is the Identity Theft By Known Imposter Package?
The Identity Theft By Known Imposter Package is a comprehensive set of documents tailored to assist individuals in Utah who are victims of identity theft perpetrated by individuals they know. This package encompasses essential forms, including affidavits, letters, and guidelines that facilitate communication with creditors and authorities.
Focused specifically on the circumstances that arise when victims are dealing with known imposters, this package is critical for both the victims seeking redress and the known imposters needing to understand their responsibilities. The intention is to streamline the process of reporting and remedying the effects of identity theft.
Purpose and Benefits of the Identity Theft By Known Imposter Package
This package serves as an invaluable resource for those impacted by identity theft by enabling them to navigate the associated challenges effectively. It aids in repairing the damage caused by identity theft, ultimately helping victims regain control over their personal information.
In addition to practical remedies, the package provides emotional relief and empowerment for victims, allowing them to approach creditors and authorities with well-structured documentation. By having proper records, victims can cooperate more efficiently with involved parties, thereby expediting the resolution of their identity theft issues.
Key Features of the Identity Theft By Known Imposter Package
The Identity Theft By Known Imposter Package is distinguished by several unique aspects that enhance its utility. Key components include essential forms such as affidavits and letters directed to relevant authorities, which are crucial for documenting incidents of identity theft.
The package also offers additional resources such as guides, checklists, and contact tables that provide valuable information for victims navigating this complex process. Furthermore, it simplifies the process of structuring legal documents to ensure effective communication with all stakeholders involved.
Who Needs the Identity Theft By Known Imposter Package?
This package is designed for individuals who find themselves victims of identity theft, particularly in situations involving a known imposter. Several scenarios necessitate the use of this package, such as individuals discovering discrepancies in their credit history that can be traced back to someone they know.
Eligibility criteria are tailored specifically for Utah residents who may benefit from the assistance provided within this package. It is essential that those affected are aware of their rights and the resources available to assist them in reclaiming their identity.
How to Fill Out the Identity Theft By Known Imposter Package
Completing the forms in the Identity Theft By Known Imposter Package involves several key steps that should be undertaken systematically. Start by reviewing all materials included in the package to ensure you understand each document’s purpose and requirements.
-
Gather all necessary personal information and documentation related to your identity theft case.
-
Complete each form accurately, following the field-by-field instructions provided.
-
Review forms for common errors, such as missing signatures or incorrect information, to avoid delays in processing.
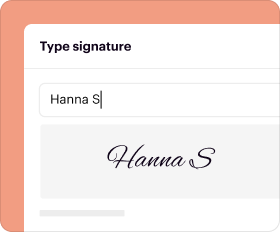
Digital Signature vs. Wet Signature Requirements
Understanding the signing requirements for the Identity Theft By Known Imposter Package is crucial. Generally, signatures are required for certain forms, and it is important to determine if a wet signature is necessary or if a digital signature will suffice for submission.
When utilizing electronic signatures, take care to follow secure protocols to ensure the integrity of your submission. In Utah, certain documents may require notarization, so be aware of additional specifics related to your jurisdiction.
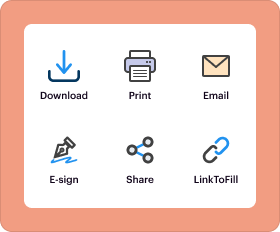
Submission Methods for the Identity Theft By Known Imposter Package
Once you have completed the package, it is essential to know how to submit your forms correctly. Various submission channels are available, including online registration, postal mail, and in-person delivery to specified agencies.
Be sure to check for any associated fees and deadlines that may apply to your submission. Additionally, understanding the confirmation and tracking processes will help you keep tabs on your submission status.
What Happens After You Submit the Identity Theft By Known Imposter Package?
After you submit the Identity Theft By Known Imposter Package, it is important to be prepared for the subsequent processes. Typical response times from authorities or creditors may vary, so patience is required.
If any issues arise post-submission, knowing the steps to take can help mitigate potential complications. It is crucial to retain records of all submitted documents, as they will be essential for any necessary follow-up.
Security and Compliance for Sensitive Documents
When dealing with sensitive documents, security is paramount. The Identity Theft By Known Imposter Package is processed with stringent security protocols that adhere to regulations such as HIPAA and GDPR, ensuring that your information is adequately protected.
Utilizing a trusted platform like pdfFiller for document management not only provides peace of mind but also helps maintain the confidentiality of your sensitive information through robust encryption methods.
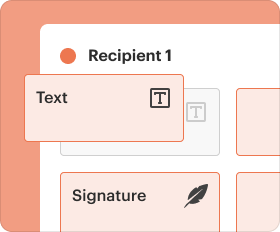
Utilizing pdfFiller to Complete the Identity Theft By Known Imposter Package
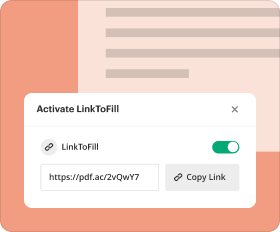
Engaging with pdfFiller provides a smooth experience for completing the Identity Theft By Known Imposter Package. The platform offers a range of features, including editing tools, secure eSigning capabilities, and ample storage options.
Users are encouraged to initiate their process with pdfFiller to enhance efficiency and ease of use. The platform’s accessibility from any device makes it a convenient choice for managing your identity theft documents.
How to fill out the identity formft by known
-
1.To access the form, visit pdfFiller and log in to your account or create a new one if you don't have one.
-
2.Search for 'Identity Theft By Known Imposter Package' in the pdfFiller search bar and select the correct document from the search results.
-
3.Once the form is open, read through the instructions and guidelines provided at the beginning of the document to understand how to fill it out.
-
4.As you fill the form, ensure you have all necessary information at hand, such as details about the impersonator, your identification, and any related correspondence with creditors.
-
5.Use pdfFiller's toolbar to navigate through fields. Click on a field to enter data; use the text box or drop-down menus as appropriate depending on the requirements.
-
6.Complete each section of the form systematically, including affidavits, letters, and checklists. Be sure to furnish all required details accurately to avoid any mistakes.
-
7.After completing the form, utilize the review feature on pdfFiller to check for any missing information or errors.
-
8.Finalize the form by saving your changes. You can download it to your device or submit it directly through pdfFiller’s submission options, depending on the requirements.
-
9.If applicable, utilize pdfFiller's print feature to produce a hard copy for your records or further submission requirements.
Who is eligible to use the Identity Theft By Known Imposter Package?
Any individual identified as a victim of identity theft by a known imposter in Utah can use this package. Additionally, known imposters may use it to respond to allegations against them.
Are there deadlines for submitting this form?
While specific deadlines may vary based on the agency or institution, it is generally advisable to submit documents promptly after discovering identity theft to facilitate quicker resolutions.
What is the procedure for submitting the completed forms?
Once completed, you can submit the forms as directed in the instructions provided within the package. This may involve sending them to creditors, law enforcement, or other relevant agencies.
What supporting documents are required with this form?
Supporting documents may include identification proof, original correspondence with creditors, law enforcement reports, and any other documentation supporting your case of identity theft.
What common mistakes should I avoid when filling out the form?
Be careful to provide accurate information. Common mistakes include missing signature fields, incorrect personal identification details, and failing to attach necessary supporting documents.
How long does it take to process claims for identity theft?
Processing times can vary widely depending on the agency involved. Generally, after submission, you may expect to hear back within 30 to 90 days, but this can differ greatly.
Can I fill out the form online?
Yes, you can complete the Identity Theft By Known Imposter Package online using platforms like pdfFiller, which allow for easy navigation and editing of legal forms.
Related Catalogs
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.