Last updated on Oct 21, 2014

Get the free Hacker Liability and Loss Application
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

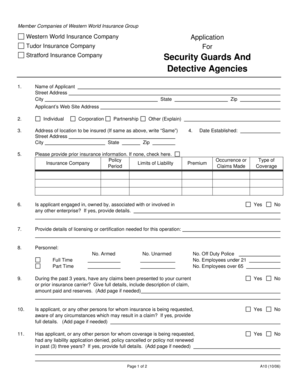
What is Hacker Liability Application
The Hacker Liability and Loss Application is a business form used by organizations to apply for insurance coverage related to hacker liability and loss.
pdfFiller scores top ratings on review platforms




Who needs Hacker Liability Application?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to Hacker Liability Application
What is the Hacker Liability and Loss Application?
The Hacker Liability and Loss Application is a critical form designed for businesses seeking to obtain hacker liability insurance. By completing this application, companies can establish the necessary groundwork for securing protection against risks associated with cyber incidents. This form holds significance for a diverse range of businesses, including tech startups, e-commerce companies, and any organization that relies heavily on digital operations.
Businesses that handle sensitive data or depend on online transactions should consider this hacker liability application to mitigate financial risks. The application details allow insurers to assess potential threats and coverage needs effectively.
Purpose and Benefits of the Hacker Liability and Loss Application
Utilizing the Hacker Liability and Loss Application brings several key advantages. First, it provides essential hacker liability coverage, protecting businesses from substantial financial losses caused by cyber attacks and data breaches. The form facilitates a clear understanding of risks and coverage levels, ensuring that organizations are adequately protected.
Among the benefits of completing this application are enhanced peace of mind, reassurance in the event of a cyber incident, and the ability to respond more effectively to security breaches, ultimately safeguarding the business's financial well-being.
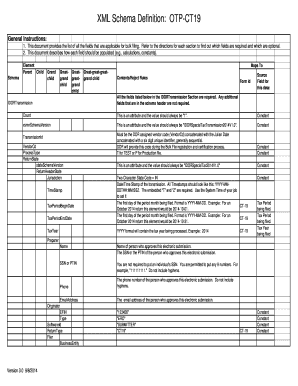
Key Features of the Hacker Liability and Loss Application
The application consists of several important components that need careful attention. Each section plays a vital role in evaluating coverage eligibility:
-
General Information: Provides foundational details about the applicant's business.
-
ECS Operations: Focuses on the electronic communications systems in use, which is crucial for assessing risks.
-
Security Incident History: Outlines any past incidents that may impact insurance coverage.
Understanding these sections helps ensure that businesses submit a comprehensive insurance application form, increasing their chances of receiving the coverage they need.
Who Needs the Hacker Liability and Loss Application?
The Hacker Liability and Loss Application is essential for various organizations, particularly those in industries with heightened vulnerability to cyber threats. Organizations such as financial institutions, healthcare providers, and e-commerce platforms should prioritize submitting this ECS security application to mitigate risks associated with their operations.
Additionally, any business that stores customer data or engages in online transactions could greatly benefit from obtaining cyber security insurance through this application.
How to Fill Out the Hacker Liability and Loss Application Online (Step-by-Step)
Filling out the Hacker Liability and Loss Application online is straightforward. Follow these steps to ensure a complete application:
-
Access the online fillable form template.
-
Enter General Information about your business in the appropriate fields.
-
Provide details regarding your electronic communications systems (ECS).
-
Document any previous security incidents in the designated section.
-
Review the completed application for accuracy before submission.
Pay special attention to specific fields that may require additional clarification to avoid common errors in the application process.
Common Errors and How to Avoid Them in the Hacker Liability and Loss Application
Applicants often encounter several pitfalls when filling out the Hacker Liability and Loss Application. Common mistakes include providing incomplete information, miscommunication of ECS operations, or failing to disclose significant security incidents. To minimize the risk of these errors:
-
Double-check all entries for accuracy and completeness.
-
Ensure clear communication of any past security incidents.
-
Review each section thoroughly before submitting the application.
Taking these proactive steps will help ensure a smoother application process and improve the chances of obtaining the necessary coverage.
Security and Compliance for the Hacker Liability and Loss Application
Data protection is paramount when submitting the Hacker Liability and Loss Application. pdfFiller employs robust security measures, including 256-bit encryption and compliance with regulations like HIPAA and GDPR. These features ensure that sensitive information, such as security incident history and other details, is safeguarded against unauthorized access.
Businesses can trust that their applications are secure when using pdfFiller for the process, allowing them to focus on their operations without the worry of data breaches.
How to Download and Submit the Hacker Liability and Loss Application
After completing the Hacker Liability and Loss Application, it is important to know how to submit the form. The submission can be done through various methods:
-
Online submission via the pdfFiller platform.
-
Mail the application to the designated insurance provider address.
Be mindful of any relevant deadlines or processing times to ensure timely coverage and responsiveness from insurers.
What Happens After You Submit the Hacker Liability and Loss Application?
Upon submission of the Hacker Liability and Loss Application, businesses can expect a standard processing timeline. Typically, applicants should allow for several days to weeks for the application to be reviewed. After submission, tracking the application status is crucial; this may involve contacting the insurance provider for updates or potential follow-ups required to finalize the coverage.
Understanding what to expect during this phase helps businesses remain informed and prepared as they navigate the insurance process.
Engage with pdfFiller for Your Hacker Liability and Loss Application Needs
Utilizing pdfFiller's cloud-based solution makes filling out, signing, and storing the Hacker Liability and Loss Application easy and efficient. The platform's editing and document management tools provide a seamless experience, enabling users to handle sensitive documents securely.
With the added benefits of a secure, cloud-based environment, pdfFiller is equipped to meet your needs for managing important insurance applications effectively.
How to fill out the Hacker Liability Application
-
1.To begin, access the Hacker Liability and Loss Application on pdfFiller by searching for the form in the template library or following a direct link provided by your insurer.
-
2.Once the form is open, you will see various sections for your information. Use the pdfFiller interface to navigate through the document, clicking on each field to enter your responses.
-
3.Before filling out the form, gather necessary information such as your business operations details, ECS functionality, and your security incident history for accurate data entry.
-
4.Carefully fill in all required fields, ensuring to provide complete and truthful information. Utilize the checkboxes and comment sections where applicable to clarify your responses.
-
5.After completing the form, review your entries for accuracy. Use pdfFiller’s editing tools to make any necessary changes before finalizing the document.
-
6.Once you are satisfied with the completed application, save your work to prevent data loss. You can also download the form or submit it directly from pdfFiller based on your insurer’s submission guidelines.

Who is eligible to apply using the Hacker Liability and Loss Application?
Any business that utilizes electronic communications and seeks insurance coverage for hacker-related incidents is eligible to apply. Ensure you meet your insurer's requirements before proceeding.
What supporting documents must I include with my application?
Typically, you are required to provide documentation related to your business operations and previous security incidents. Check with your insurer for specific requirements.
How should I submit the completed form?
The completed Hacker Liability and Loss Application can usually be submitted electronically via your insurer's portal or by email. Consult the submission guidelines given by your insurance provider.
Are there any common mistakes to avoid while filling out this application?
Ensure all fields are accurately completed and check for spelling errors. Missing information or unchecked boxes can delay the processing of your application.
What is the processing time for the Hacker Liability and Loss Application?
Processing times can vary, but generally, you can expect feedback within a few weeks after submission. Always confirm with your insurer for exact timelines.
Do I need to notarize this application?
No, notarization is generally not required for the Hacker Liability and Loss Application. However, verify with your insurer to confirm their specific requirements.
What if I need to make changes after submitting the form?
If you need to make changes after submission, contact your insurer immediately to discuss the procedures for amending your application.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.