Last updated on Dec 5, 2014

Get the free Suspicious Activity Report Narrative Outline
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is SAR Narrative Outline
The Suspicious Activity Report Narrative Outline is a template used by financial institutions to report suspicious activities to law enforcement efficiently.
pdfFiller scores top ratings on review platforms




Who needs SAR Narrative Outline?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to SAR Narrative Outline
What is the Suspicious Activity Report Narrative Outline?
The Suspicious Activity Report (SAR) Narrative Outline is a crucial tool employed by financial institutions to document and report suspected illegal activities. Understanding the SAR narrative structure is vital for compliance with financial regulations and assisting law enforcement agencies in investigations.
The SAR Narrative Outline consists of distinct sections designed to guide users in providing comprehensive information. It highlights the importance of accurately describing various aspects of suspicious activities while ensuring adherence to filing guidelines.
Purpose and Benefits of the Suspicious Activity Report Narrative Outline
The SAR Narrative Outline serves several important purposes for financial institutions and law enforcement. Primarily, it ensures compliance with financial regulations, which is essential in the fight against financial crime.
Utilizing this outline facilitates effective communication with law enforcement, making it easier to share vital information efficiently. It also aids institutions in identifying and mitigating potential financial crimes, thereby reinforcing their commitment to regulatory compliance and safeguarding the financial system.
Key Features of the Suspicious Activity Report Narrative Outline
The SAR Narrative Outline includes several key components that enhance the reporting process. Users will find blank fields designed for thorough information gathering, encouraging comprehensive details across various sections.
-
Sections to detail previous SARs and any associations with sanctioned entities.
-
Areas to document critical red flags detected during transactions.
-
Fields for recording cash transaction details essential to the report.
Who Needs the Suspicious Activity Report Narrative Outline?
The primary audience for the SAR Narrative Outline includes financial institutions that are mandated to report suspicious activities to the appropriate authorities. These institutions are crucial in maintaining the integrity of the financial system.
Additionally, law enforcement agencies rely on these detailed reports to conduct investigations effectively. Other stakeholders involved may include compliance officers and legal teams who play roles in ensuring accurate reporting and adherence to regulatory requirements.
When and How to File the Suspicious Activity Report Narrative Outline
Filing the SAR Narrative Outline requires an understanding of eligibility criteria. Institutions must determine the circumstances under which they are obliged to submit a report.
Once the decision to file is made, it is essential to follow a structured process. The following steps outline how to fill out the form completely online:
-
Access the SAR Narrative Outline template through your filing platform.
-
Complete each section with accurate and thorough information.
-
Review the completed form for any errors or omissions.
-
Submit the form electronically through the designated channel.
Common Errors and How to Avoid Them
Recognizing common errors when filling out the SAR Narrative Outline can prevent submission delays and compliance issues. Frequent mistakes include incomplete data entry and misunderstandings regarding the form's requirements.
To ensure successful filings, it is important to implement a review process. Thoroughly validating the submission before filing can significantly reduce the likelihood of errors and improve the accuracy of the information provided.
Submission Methods and Confirmation
There are various methods available for submitting the SAR Narrative Outline, including e-filing and postal options. Each method offers different levels of tracking and confirmation for the submitted reports.
After submission, it is crucial to understand what happens next. Institutions should expect confirmation of receipt and, if applicable, guidance on any further actions required.
Security and Compliance for the Suspicious Activity Report Narrative Outline
Handling sensitive information in the SAR requires strict security measures due to the associated risks. Financial institutions must prioritize data protection and adhere to relevant privacy regulations.
Utilizing tools with robust security features can help safeguard filed SARs. Recommendations include implementing secure storage solutions and ensuring compliance with security standards to prevent unauthorized access.
How pdfFiller Can Help You with the Suspicious Activity Report Narrative Outline
pdfFiller provides a user-friendly platform for completing and managing the SAR form effectively. With features tailored for filling out, editing, and eSigning, pdfFiller simplifies the reporting process.
Moreover, pdfFiller's security certifications ensure that sensitive financial documents are handled safely, giving users peace of mind throughout the reporting process.
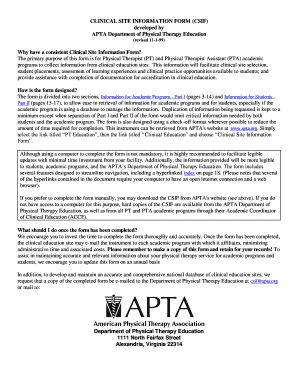
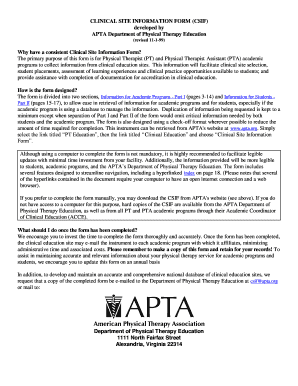
Sample of a Completed Suspicious Activity Report Narrative Outline
Providing users with a sample of a completed SAR Narrative Outline can serve as a valuable reference. The sample includes a visual representation of a filled form and highlights key sections with example entries.
Users are encouraged to use this template as a guide, ensuring their submissions are detailed and accurate by following best practices in documenting suspicious activities.
How to fill out the SAR Narrative Outline
-
1.To begin, access pdfFiller and log in to your account. Use the search bar to locate the 'Suspicious Activity Report Narrative Outline' form and click on it to open.
-
2.Once the form is open, familiarize yourself with its structure. The fillable fields will guide you through the necessary information sections.
-
3.Gather all required information before starting. This includes previous SAR details, entity associations, transaction specifics, and any red flags pertaining to the activity.
-
4.Start filling in the first section by providing a clear purpose of the SAR. Make sure to describe the known or alleged violation thoroughly.
-
5.Continue through the form, entering information in each required field. Use the clear instructions provided within the form sections to assist your responses.
-
6.Pay attention to the guidance notes on the form that indicate crucial data points, such as dates of prior SARs and relevant entity affiliations.
-
7.Review your information to ensure accuracy. Double-check entries for errors or incomplete sections.
-
8.Once satisfied with the information entered, navigate to the 'Save' option. Decide whether to download the completed form as a PDF or submit it directly through pdfFiller.
-
9.If choosing to submit, follow the prompts for electronic filing, ensuring that all required sections are filled correctly before hitting 'Submit'.

Who is eligible to use the Suspicious Activity Report Narrative Outline?
Financial institutions, compliance officers, and law enforcement agencies are eligible to use this form for documenting suspicious activities per regulatory requirements.
What is the deadline for submitting a Suspicious Activity Report?
While there is no universal deadline, SARs should be filed promptly upon identifying suspicious activities to comply with the regulations.
How should I submit the filled-out Suspicious Activity Report?
You can submit the completed form electronically through pdfFiller or print and mail it as required by your institution or the governing agency.
What supporting documents are required with the SAR Narrative Outline?
Typically, supporting documents may include transaction records, identification information of involved parties, and prior SARs related to the case in question.
What common mistakes should I avoid while filling out the form?
Common mistakes include providing incomplete information, failing to review for accuracy, and neglecting to document all suspicious behaviors.
How long does it take to process a Suspicious Activity Report?
Processing times can vary depending on the jurisdiction and complexity of the case but expect a timeframe of several days to weeks for feedback.
What if I have concerns about the information I need to report?
If you have concerns regarding what to include, consult with your compliance department or legal advisors for guidance to ensure accurate reporting.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.