Last updated on Mar 29, 2026
DHS Ransomware Self-Assessment Tool free printable template
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
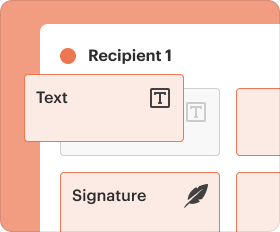
End-to-end document management
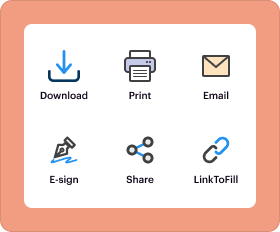
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
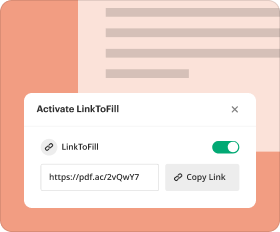
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.
What is DHS Ransomware Self-Assessment Tool
The Ransomware Self-Assessment Tool is a service agreement document used by financial institutions to evaluate their ransomware preparedness and cybersecurity measures.
pdfFiller scores top ratings on review platforms




Who needs DHS Ransomware Self-Assessment Tool?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to DHS Ransomware Self-Assessment Tool
Understanding the Ransomware Self-Assessment Tool (R-SAT)
The Ransomware Self-Assessment Tool (R-SAT) is designed specifically for financial institutions to evaluate their readiness against ransomware threats. This tool plays a crucial role in helping banks assess cybersecurity measures essential for safeguarding sensitive data. By utilizing the R-SAT, institutions can gain insights into their ransomware preparedness and identify areas requiring improvement.
Evaluating cybersecurity measures through the R-SAT allows organizations to establish a baseline for their security posture. As ransomware attacks become increasingly prevalent, understanding the threats and being prepared can significantly enhance a financial institution's defenses.
Purpose and Benefits of the Ransomware Self-Assessment Tool
This tool is specifically designed for executive management and board evaluations, providing numerous benefits that can enhance security measures across financial institutions. Utilizing the R-SAT allows organizations to identify weaknesses and strategize on protecting, detecting, responding to, and recovering from potential cyber attacks.
The benefits of conducting a ransomware risk assessment include improved compliance with regulations and a more robust cybersecurity framework. Engaging with the tool enables organizations to proactively mitigate risks associated with ransomware threats.
Key Features of the Ransomware Self-Assessment Tool
-
Main components such as checkboxes and fields for information entry
-
Sections dedicated to identifying critical data and evaluating vendor risks
-
Guidance on institutional self-assessment to fortify defenses against ransomware
The tool’s structured format ensures that financial institutions have a comprehensive approach to cybersecurity, enhancing their resilience against ransomware attacks.
Who Should Use the Ransomware Self-Assessment Tool
The R-SAT is targeted at financial executives and board members who play a pivotal role in cybersecurity strategies. Each group benefits from engaging with the tool as it provides tailored insights into their organization's security measures.
It becomes essential for executives when there are regulatory updates or evolving cyber threats, allowing for timely assessments that ensure the institution is prepared for any potential ransomware incidents.
How to Complete the Ransomware Self-Assessment Tool Online
-
Access the R-SAT using pdfFiller.
-
Fill out the required fields, ensuring accuracy in your responses.
-
Utilize thorough risk assessment methods to compile necessary information.
Following these steps ensures a comprehensive approach to assessing risks, vital for enhancing cybersecurity preparedness across financial institutions.
Review and Validation Checklist for the Ransomware Self-Assessment Tool
Reviewing completed assessments is critical for accuracy and effectiveness. Utilize the following checklist to validate your assessment:
-
Ensure all necessary fields are filled out completely.
-
Cross-check data entries for accuracy.
-
Avoid common errors, such as omitting critical information.
This thorough review process can identify potential weaknesses before submission, ensuring a reliable and actionable assessment.
Submitting the Ransomware Self-Assessment Tool
To submit your completed R-SAT, follow these guidelines:
-
Choose one of the available submission methods, such as via email or an online portal.
-
Track the submission to maintain compliance and ensure timely review.
Submitting the completed tool is essential for ongoing assessment and maintaining the institution's security framework.
Post-Submission Actions for the Ransomware Self-Assessment Tool
After submitting the R-SAT, organizations should focus on assessing outcomes and enhancing their security posture. Monitoring effectiveness is crucial for making necessary adjustments to current strategies.
Setting up an ongoing evaluation and renewal process for the assessment will keep cybersecurity measures relevant and up-to-date in the face of evolving threats.
Why Choose pdfFiller for Your Ransomware Self-Assessment Needs?
pdfFiller provides a reliable platform for completing the R-SAT, focusing on the security of sensitive documents with features like 256-bit encryption and GDPR compliance. The cloud-based PDF editor is designed for seamless document management, making it easy to access and fill out the R-SAT from any browser.
Taking Action to Enhance Your Cybersecurity Preparedness
Now is the time to initiate your ransomware self-assessment process. Accessing the tool via pdfFiller empowers you to maximize its capabilities to assess your organization's readiness. Remember, being proactive in cybersecurity is fundamental to safeguarding your financial institution against potential ransomware threats.
How to fill out the DHS Ransomware Self-Assessment Tool
-
1.To access the Ransomware Self-Assessment Tool on pdfFiller, navigate to the pdfFiller website and use the search bar to locate the document by typing its name.
-
2.Once you find the form, click on it to open. The intuitive pdfFiller interface will allow you to view the document with interactive fields.
-
3.Before filling out the form, gather necessary information such as your bank's critical data, current cybersecurity controls in place, and third-party vendor information. This preparation is essential for accurate completion.
-
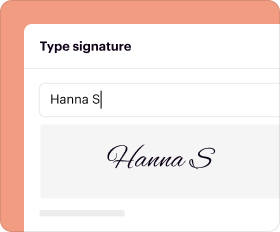
4.Start completing the document by clicking on each checkbox and filling in required fields such as 'Name and Title', 'Email', 'Phone Number', 'Institution Name', 'Date Completed', and 'Date Reviewed by Board'. Ensure all responses are accurate.
-
5.After filling in all fields, review your entries carefully to ensure all information is correct and reflects your institution's current status.
-
6.Once you are satisfied with the completed form, you can save it by clicking the save icon. Choose the appropriate file format to download, if necessary.
-
7.You also have the option to share or submit the filled form directly through pdfFiller options, ensuring you follow any specific submission guidelines required by your institution.
Who is eligible to use the Ransomware Self-Assessment Tool?
The Ransomware Self-Assessment Tool is designed for executive management and board members of financial institutions, including banks and credit unions, responsible for evaluating and improving their cybersecurity readiness.
Are there any deadlines for completing the assessment?
While there are typically no strict deadlines for completing the Ransomware Self-Assessment Tool, it is advisable to conduct assessments regularly and when significant changes to cybersecurity protocols occur.
What methods can I use to submit the completed form?
Completed forms can be submitted electronically via email or through pdfFiller's submission options. Ensure you follow your institution's guidelines for submission methods.
What supporting documents are required with the assessment?
Supporting documents may include reports on existing cybersecurity measures, previous assessments, and vendor agreements that outline third-party risks. However, the tool itself does not require additional documents for completion.
What common mistakes should I avoid when filling out the form?
Common mistakes include failing to accurately assess the current cybersecurity measures in place, overlooking certain fields, and not involving necessary stakeholders in the completion process.
How long does it take to process the assessment after submission?
The processing time for the Ransomware Self-Assessment Tool varies depending on your institution's review procedure. However, it is typically reviewed at the next scheduled board meeting or risk assessment session.
What specific concerns does the tool address?
The tool helps financial institutions evaluate their ability to identify, protect, detect, respond to, and recover from ransomware attacks, focusing on critical data, cybersecurity controls, and vendor risks.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.