Last updated on Jul 22, 2012

Get the free Epic Security Individual Access Request Form
We are not affiliated with any brand or entity on this form
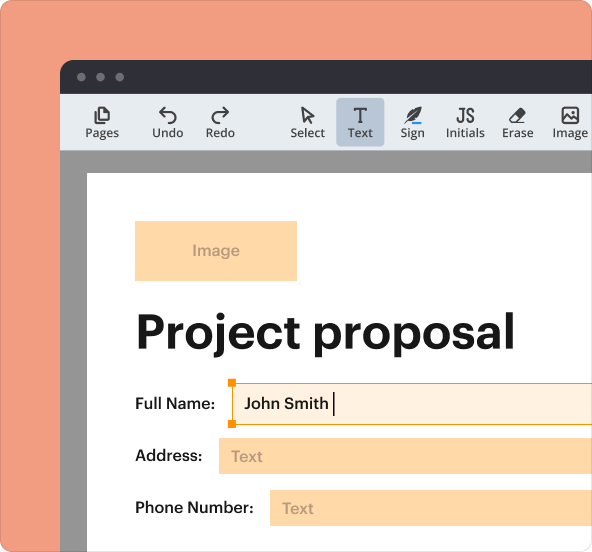
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

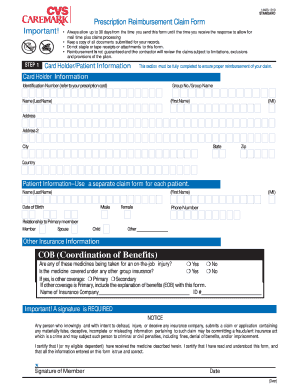
What is epic security individual access
The Epic Security Individual Access Request Form is a medical consent document used by clinic employees to request access to specific healthcare systems.
pdfFiller scores top ratings on review platforms




Who needs epic security individual access?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to epic security individual access
What is the Epic Security Individual Access Request Form?
The Epic Security Individual Access Request Form is a crucial document in healthcare access management. This form enables clinic employees and authorized agents to request access to necessary healthcare systems securely. Its significance lies in ensuring that only authorized personnel can access sensitive patient information, thereby maintaining the integrity and confidentiality of the healthcare system.
By utilizing the epic security access request form, healthcare providers can manage permissions effectively, ensuring compliance with industry standards while facilitating necessary access for those who need it most.
Purpose and Benefits of the Epic Security Individual Access Request Form
The purpose of the Epic Security Individual Access Request Form is to control and monitor access to medical systems, allowing only verified users to gain entry. One of the primary benefits is the streamlined process it provides for users, facilitating easy access while adhering to stringent security protocols.
This form also documents proper authorization, which is vital in maintaining compliance and accountability within healthcare operations. Utilizing this form minimizes risks associated with unauthorized access, creating a safer environment for patient data management.
Key Features of the Epic Security Individual Access Request Form
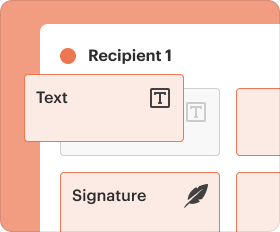
This form includes several key features designed to simplify the access request process. First, it contains fillable fields that require essential information, ensuring clarity in requests. There are checkboxes to streamline the authorization process, along with required signatures from both the user and an authorized agent, affirming compliance and accountability.
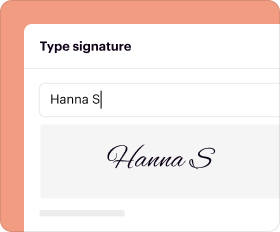
The form also supports digital capabilities, including eSigning, which enhances the overall efficiency of submitting requests, making it easier for clinic employees to manage their access permissions.
Who Needs the Epic Security Individual Access Request Form?
The Epic Security Individual Access Request Form is essential for various roles within the healthcare environment. Specifically, clinic employees who need access to patient information are required to fill out the form. Additionally, it is also necessary for authorized agents who must sign off on the request.
Other stakeholders might include IT personnel and administrative staff who directly manage access protocols and oversight, underscoring the form's critical nature in ensuring authorized access.
How to Fill Out the Epic Security Individual Access Request Form Online
To fill out the Epic Security Individual Access Request Form online, follow these step-by-step instructions:
-
Gather all necessary personal information, including role details and contact information.
-
Access the form via pdfFiller’s online platform.
-
Complete each fillable field accurately, ensuring that required fields are filled in.
-
Check off any necessary checkboxes and sign where indicated, either digitally or by hand.
-
Review the completed form for accuracy before submission.
Be aware of common pitfalls, such as forgetting to sign or omitting crucial information, as these can delay processing.
Submission Methods and Delivery for the Epic Security Individual Access Request Form
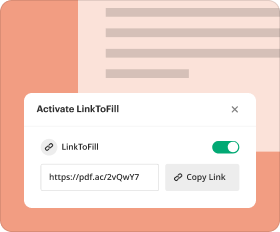
After completing the form, several methods are available for submission. Users can submit their requests via email or through an online portal specifically designed for accessing these forms.
After submission, it is vital to obtain confirmation to ensure that the request has been received successfully. Being aware of potential delivery issues and addressing them promptly can help prevent delays in accessing necessary systems.
Security and Compliance Measures
When handling sensitive information, security is paramount. pdfFiller implements several robust security features, including advanced encryption methods and adherence to compliance standards such as HIPAA.
Using secure methods for submitting and storing the Epic Security Individual Access Request Form is crucial to protect patient information. The form's design ensures that safety measures are prioritized, safeguarding both personal data and compliance with industry regulations.
Tracking Your Submission and What Happens Next
Monitoring the status of your submission is an important part of the process. You can check the status of your application by accessing the online portal where the request was submitted.
Expect to receive communications regarding processing times, and be prepared to act if any issues arise with your submitted request. Understanding what happens next helps maintain clarity during the access request process.
How to Correct or Amend the Epic Security Individual Access Request Form
If corrections or amendments to the Epic Security Individual Access Request Form are necessary, follow these guidelines. Common reasons for corrections include incorrect personal information or changes in authorization status.
To amend the form, simply access the original submission on pdfFiller, make the necessary changes, and resubmit. Timely communication regarding these changes is essential to ensure compliance and quick resolution.
Empowering Your Form Experience with pdfFiller
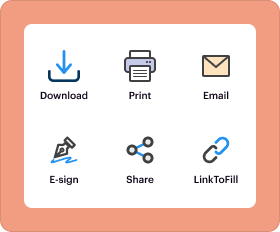
pdfFiller offers a powerful platform to enhance the efficiency of filling out forms, including the Epic Security Individual Access Request Form. Users can take advantage of features like easy editing, eSigning, and secure document management.
By leveraging pdfFiller’s capabilities, users can complete essential healthcare forms securely and efficiently, ensuring that all necessary procedures are followed while saving time and minimizing errors.
How to fill out the epic security individual access
-
1.Access the Epic Security Individual Access Request Form on pdfFiller by searching for the form name in the platform's search bar.
-
2.Once the form opens, read through the instructions provided at the top to ensure understanding of each field.
-
3.Begin filling in your personal information carefully, ensuring all required fields are completed accurately.
-
4.Select your role from the provided options, which may include User or Authorized Agent, depending on your situation.
-
5.Gather any necessary identification or documentation that supports your access request before finalizing the form.
-
6.Review all entered information for accuracy, focusing on names, dates, and relevant details.
-
7.Once satisfied with the form, use pdfFiller’s features to save your progress or download a copy for your records.
-
8.To submit the completed form, select the appropriate submission method indicated within the platform, ensuring that all signatures are included.
Who is eligible to use the Epic Security Individual Access Request Form?
Any clinic employee or authorized agent who needs access to specific medical systems in the healthcare facility is eligible to fill out the Epic Security Individual Access Request Form.
What is the deadline for submitting this form?
While the Epic Security Individual Access Request Form does not have a universal deadline, it is advisable to submit it as soon as access is required, allowing for processing time.
How do I submit the completed form?
The completed Epic Security Individual Access Request Form can typically be submitted via the method indicated on pdfFiller, which may include electronic submission or printing and delivering it to the appropriate department.
Are there any supporting documents required with this form?
Yes, if applicable, you may need to attach identification verifying your role or other documentation that supports your request for access to medical systems.
What should I avoid when completing this form?
When filling out the Epic Security Individual Access Request Form, ensure to fill in all required fields and avoid any incomplete submissions, as this can delay processing.
How long does it take for the form to be processed?
Processing times for the Epic Security Individual Access Request Form vary by organization, but typically, you can expect to receive a response within a few business days.
What if I need assistance while filling out the form?
If you require help, consider reaching out to your organization's IT or compliance department for guidance on completing the Epic Security Individual Access Request Form.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.