Last updated on Feb 13, 2015

Get the free Security Access Request Form
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

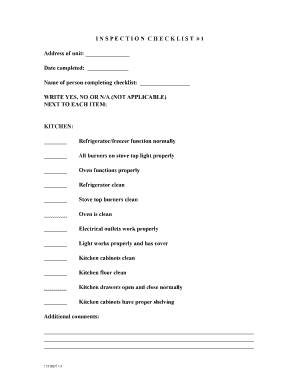
What is Security Access Form
The Security Access Request Form is a request document used by educational facilities to obtain or revoke security user access for staff members.
pdfFiller scores top ratings on review platforms




Who needs Security Access Form?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to Security Access Form
What is the Security Access Request Form?
The Security Access Request Form serves a critical function in educational settings by facilitating the request for new user access or the deletion of existing security users. This essential document ensures the proper management of access rights within schools and educational facilities. Each completed form must bear the Principal's signature, affirming the legitimacy of the access request.
Using this form correctly contributes to maintaining secure environments in educational institutions while adhering to necessary protocols.
Purpose and Benefits of the Security Access Request Form
The Security Access Request Form is crucial for educational institutions, primarily by enhancing access control measures. By clearly documenting access requests, the form aids in safeguarding sensitive areas and information on campus.
Among its many benefits, the form promotes improved campus security and compliance with regulations governing educational environments. Effective management of access rights not only protects students and staff but also supports the safe operation of facilities.
Key Features of the Security Access Request Form
-
Includes fields for essential user details and designated access areas.
-
Seamlessly integrates with the CFS Alarm Communications Dispatch Center for real-time processing.
-
User-friendly format featuring checkboxes and straightforward instructions for ease of completion.
Who Needs the Security Access Request Form?
This form is primarily utilized by principals and administrators within educational institutions. It is necessary in various situations, such as when students or staff require access to specific facilities or when access needs to be revoked.
Various educational facilities, from public schools to universities, often require this form as part of their security protocols to ensure a safe learning atmosphere.
How to Fill Out the Security Access Request Form Online (Step-by-Step)
-
Gather necessary information, including user details and school information.
-
Access the Security Access Request Form on the pdfFiller platform.
-
Complete all required fields accurately, ensuring clarity and correct input.
-
Review all entries for accuracy before submission.
-
Submit the form electronically through pdfFiller or follow the specific submission instructions provided.
Review and Validation Checklist for the Security Access Request Form
-
Ensure all required fields are completed, including user details and access areas.
-
Check for common errors, such as typos or missing information.
-
Verify the Principal's signature is present and correctly located on the form.
Thoroughly reviewing your completed form before submission can prevent common mistakes and delays.
Submission Methods for the Security Access Request Form
Completed forms can be submitted through various methods, including online submission via pdfFiller or email. It is essential to consider the timing of submission, particularly in relation to access needs and deadlines.
Be aware of any specific state or jurisdiction rules that may dictate submission protocols or timelines, which can impact the processing of the request.
What Happens After You Submit the Security Access Request Form?
After submission, the processing timeline can vary, and confirmation of receipt may be provided. Users can track their submission through the respective systems in place.
Outcomes may include approval or rejection of the access request. If rejected, understanding common reasons can help in addressing issues for future submissions.
Securely Managing the Security Access Request Form with pdfFiller
pdfFiller offers robust capabilities for managing the Security Access Request Form, including eSigning and secure document storage. Utilizing these features is critical for maintaining security and confidentiality of sensitive information contained in the form.
Users are encouraged to leverage pdfFiller's tools to ensure efficiency and compliance in managing their forms.
Final Thoughts on Completing Your Security Access Request Form
Completing the Security Access Request Form accurately is fundamental to maintaining security protocols in educational institutions. Take advantage of pdfFiller's functionalities for a seamless experience in filling and submitting the form.
Users are encouraged to explore pdfFiller’s capabilities to streamline their form submission process and enhance security measures for sensitive information.
How to fill out the Security Access Form
-
1.Access pdfFiller by visiting their website and logging in or creating an account if necessary.
-
2.Search for the 'Security Access Request Form' using the search bar to find the appropriate document.
-
3.Open the form in pdfFiller's editor; familiarize yourself with the interface to easily navigate the form's fields.
-
4.Before you start filling out the form, gather necessary information including school details, user information, and specific areas of access required.
-
5.Begin filling out the form by clicking on each field. Input the school or facility name, user’s full name, and provide the requested access areas.
-
6.Utilize checkboxes available for specifying which access types are necessary. Ensure all required fields are completed.
-
7.Add the Principal's signature by selecting the signature field and following prompts to sign electronically or upload an image of your signature.
-
8.Once all fields are filled, review the form for any errors or missing information by scrolling through each section.
-
9.After thorough review, save your work to ensure no data is lost. Use the option to download a copy for your records.
-
10.To submit the form, follow the instructions outlined by your institution. You may also use pdfFiller to email or fax the completed form directly from the platform.

Who is eligible to fill out the Security Access Request Form?
Typically, the Security Access Request Form can be filled out by school administrators, IT staff, or authorized personnel at educational institutions who require granting or revoking access for security users.
What documents should accompany the Security Access Request Form?
While the form itself does not require attachments, it may help to include any relevant identification or employment verification documents to expedite processing.
How do I submit the Security Access Request Form?
You can submit the Security Access Request Form directly through pdfFiller by using their email or fax options or by following your institution's designated submission procedures.
Are there deadlines for submitting the Security Access Request Form?
Deadlines may vary depending on your institution's policies. It's best to check with the administrative office to understand any important timelines to follow.
What are common mistakes to avoid when filling out the form?
Common mistakes include leaving required fields blank, misplacing the Principal's signature, and overlooking detailed access areas needed for users. Double-check all entries.
How long does it take to process the Security Access Request Form?
Processing times can vary based on your institution's procedures, but it usually takes a few days to a week to complete the review, depending on workload.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.