Last updated on May 10, 2026

Get the free Request for Deviation from Security Criteria
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is Security Deviation Request
The Request for Deviation from Security Criteria is a federal document used by military personnel to formally request deviations from established security criteria.
pdfFiller scores top ratings on review platforms




Who needs Security Deviation Request?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to Security Deviation Request
What is the Request for Deviation from Security Criteria?
The Request for Deviation from Security Criteria is a formal document used by military personnel and federal agencies to propose deviations from established security protocols. This form serves a crucial purpose in ensuring operational flexibility while adhering to security requirements. Each submission must be duly signed by three parties: the requester, a reviewing official, and an approval authority, ensuring a comprehensive review process. The request deviation security criteria form is integral to maintaining both security and efficiency in military operations.
Purpose and Benefits of the Request for Deviation from Security Criteria
This form is essential for enabling military personnel to navigate exceptional circumstances that may warrant security deviations. By allowing certain modifications, the form enhances operational readiness and facilitates compliance with changing security requirements. Specific scenarios where deviation may prove beneficial include:
-
Addressing urgent operational needs.
-
Accommodating unique mission requirements.
-
Mitigating unforeseen security challenges.
The efficient processing of this request ensures that personnel can maintain mission focus while adapting to necessary changes in security protocols. Furthermore, the military security deviation form represents a proactive approach to managing security challenges.
Who Needs to Use the Request for Deviation from Security Criteria?
The primary users of the request deviation security criteria form are individuals within military and federal agencies tasked with security oversight. Typically, the roles involved include:
-
Requester: The individual seeking the deviation.
-
Reviewing Official: The person responsible for validating the request’s justification.
-
Approval Authority: The official who grants final consent for the requested deviation.
Departments that may need to initiate this request include security divisions, operational commands, and compliance offices, ensuring that various roles are fulfilled appropriately.
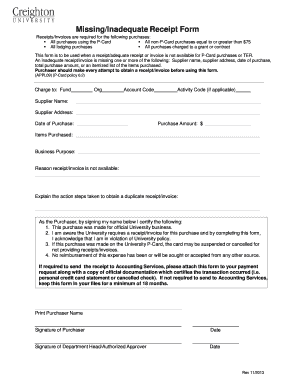
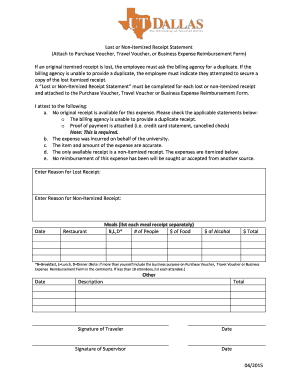
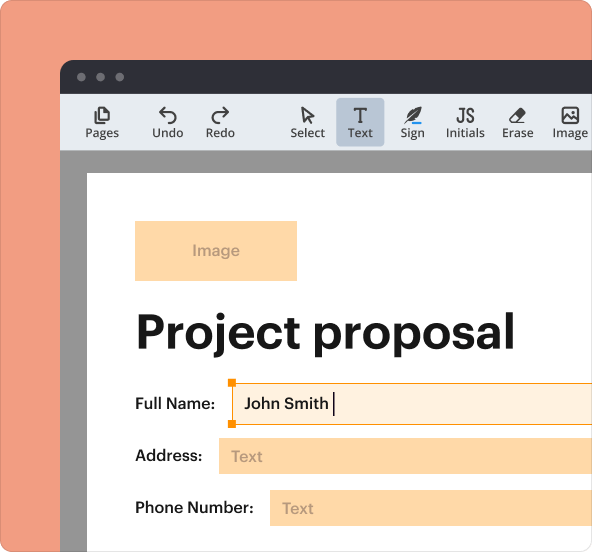
How to Fill Out the Request for Deviation from Security Criteria Online
Filling out the request for deviation from security criteria form online can be streamlined using pdfFiller. Follow these steps for accurate completion:
-
Access the fillable security deviation form on pdfFiller.
-
Fill in all required fields with accurate information.
-
Ensure all necessary signatures are obtained.
-
Review the form for completeness before submission.
Thoroughness and accuracy in filling out the form are critical, as even minor mistakes can impact the approval process.
Common Errors and How to Avoid Them When Submitting the Request for Deviation
When submitting the request for deviation, certain errors frequently occur, hindering the approval process. Common mistakes include:
-
Incomplete fields or missing information.
-
Incorrect signatures or missing dates.
-
Failure to follow submission guidelines.
To avoid these issues, carefully review all entries and confirm that each required signature is in place prior to submission. Attention to detail is essential to ensure compliance with submission requirements.
Submission Methods and Tracking Your Request for Deviation from Security Criteria
Various submission methods are available for the request deviation security criteria form, including:
-
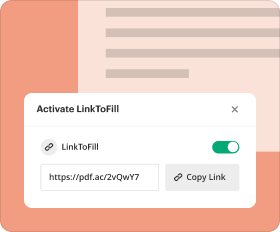
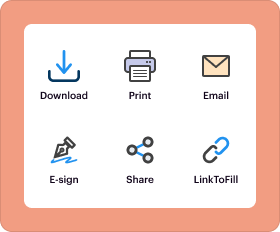
Online submission via pdfFiller.
-
Mailing the completed form to the relevant authority.
-
In-person submission at designated offices.
Once submitted, tracking the request’s status can be done through specified channels, which may include confirmation emails or a tracking system provided by the agency.
Consequences of Not Filing or Late Filing the Request for Deviation
Failure to submit the request for deviation on time may lead to significant repercussions for military personnel, including:
-
Operational delays.
-
Disciplinary actions for non-compliance.
-
Increased risks to security and mission integrity.
Timely submission is crucial to prevent these consequences, reinforcing the importance of adhering to established deadlines.
Security and Compliance When Handling the Request for Deviation from Security Criteria
When dealing with sensitive documents, such as the request for deviation from security criteria form, security and compliance are paramount. Utilizing platforms like pdfFiller, which features 256-bit encryption and adheres to HIPAA and GDPR standards, ensures that sensitive information is managed securely. This level of security is critical when handling the security criteria form, safeguarding the integrity of the data submitted.
How pdfFiller Can Help You Manage Your Request for Deviation from Security Criteria
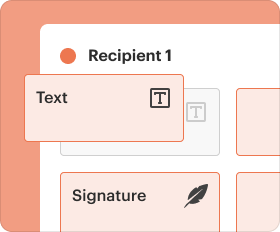
pdfFiller provides key capabilities that enhance the management of the request for deviation from security criteria form, including:
-
Comprehensive form editing options.
-
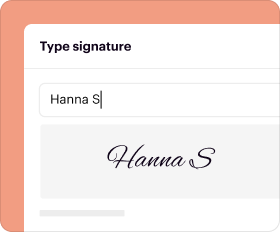
Secure eSigning processes.
-
Intuitive navigation for easier form completion.
By utilizing pdfFiller, users can ensure a hassle-free experience in managing and processing their forms, thereby streamlining compliance with operational requirements.
Sample Completed Request for Deviation from Security Criteria
To assist users in understanding the completion process, a sample filled-out request is provided. This example highlights:
-
Specific fields that require attention.
-
Checkboxes for options.
-
The overall format and structure of the form.
These contextual elements demonstrate the necessary information required in each section, facilitating a smoother completion experience.
How to fill out the Security Deviation Request
-
1.Access pdfFiller and log in to your account, or create a new account if you don't have one.
-
2.Search for 'Request for Deviation from Security Criteria' in the document library or upload the form directly if you have a copy.
-
3.Open the form in the pdfFiller editor to begin completing it.
-
4.Familiarize yourself with the form's sections, including the 'REQUEST NUMBER', 'SIGNATURE', and any checkbox options.
-
5.Gather all necessary information before you start filling in the form. This includes details on the deficiency, justification for the deviation, and proposed corrective actions.
-
6.Start entering information into the fillable fields. Ensure all details are accurate and complete to avoid processing delays.
-
7.Utilize pdfFiller's templates and guides if available for assistance while completing the form.
-
8.After filling in all required fields, review the form for any errors or incomplete sections. Ensure all signatures are included.
-
9.Once you are satisfied with the completed document, save your progress. You can also download the form for your records.
-
10.To submit the form, follow the provided submission guidelines or options within pdfFiller for emailing or sharing the document directly.
Who is eligible to submit the Request for Deviation from Security Criteria?
Eligibility to submit the Request for Deviation from Security Criteria generally includes military personnel and staff authorized by the military to request deviations. The form must be completed with necessary justifications and signed by authorized officials.
What is the deadline for submitting this form?
There are typically no strict deadlines for submitting the Request for Deviation from Security Criteria, but it should be filed as soon as a need for security deviation is identified. Prompt submission is advised to ensure timely processing.
How do I submit the completed form?
Upon completion of the Request for Deviation from Security Criteria, you can submit it through your designated military submission channels. This may include direct submission to your superiors or uploading to a military compliance system.
Are there any supporting documents required with the form?
Typically, supporting documents may include technical justifications, previous security assessments, or risk analysis reports that substantiate the need for deviation. Check with your reviewing official for specific requirements.
What are common mistakes to avoid when filling out the form?
Common mistakes include leaving required fields blank, providing vague justifications, not securing necessary signatures, or submitting the form without a thorough review. Always double-check for completeness and clarity.
How long does it take to process the request?
Processing times for the Request for Deviation from Security Criteria can vary based on the complexity of the request and the reviewing authority's workload. Generally, allow for a few weeks to receive feedback or approval.
Can the form be filled out digitally?
Yes, the Request for Deviation from Security Criteria can be filled out digitally using pdfFiller. The platform allows for easy completion, saving, and submission of the form without printing.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.