Last updated on Mar 29, 2026

Get the free Form 2875 System Authorization Access Request
We are not affiliated with any brand or entity on this form
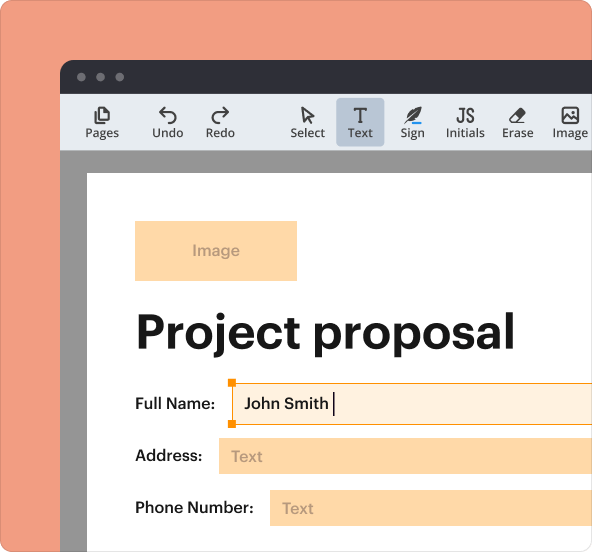
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is form 2875 system authorization
The Form 2875 is a System Authorization Access Request used by the National Defense University to validate individuals requesting access to Department of Defense systems and information.
pdfFiller scores top ratings on review platforms




Who needs form 2875 system authorization?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to form 2875 system authorization
What is the Form 2875 System Authorization Access Request?
The Form 2875 is a vital document known as the System Authorization Access Request (SAAR) within the Department of Defense (DoD). This form plays a crucial role in validating the trustworthiness of individuals proposing to access sensitive DoD systems and information. Required information includes personal details, organizational data, and a justification for access to specific systems.
This form is utilized by various personnel within the DoD, including military and civilian users, to request necessary access. Completing the Form 2875 is essential for ensuring compliance with security protocols, making it a cornerstone for maintaining the integrity of DoD systems.
Purpose and Benefits of the Form 2875
The Form 2875 serves a clear purpose: establishing trustworthiness when accessing DoD systems. By utilizing a standardized military system access form, the process ensures a uniform approach to handling requests, which enhances overall security measures.
Some key benefits include:
-
Enhancements in security protocols across systems.
-
Facilitation of consistent access requests through a single form.
-
Compliance with required annual updates and cybersecurity training.
Who Needs to Complete the Form 2875?
Filling out the Form 2875 involves several specific roles, each with distinct responsibilities. The following roles are required to sign the form:
-
Requestor
-
Supervisor
-
Security Manager
-
System Owner
-
Cybersecurity personnel
Each of these roles contributes to the oversight and submission of the request, ensuring that all eligible users meet the necessary criteria for accessing crucial DoD systems.
Key Features of the Form 2875 System Authorization Access Request
The Form 2875 is designed with user-friendliness in mind. It includes important features such as fillable fields and sections requiring signatures. Key elements of the form's layout include:
-
Prominent sections for justification of access.
-
Checkboxes for selecting types of requests.
-
Digital signing capabilities for enhanced convenience.
This structure promotes easy navigation and completion of the form in a fillable PDF format.
Step-by-Step Guide: How to Fill Out the Form 2875 Online
Completing the Form 2875 correctly is essential. Here’s a simple breakdown of the process:
-
Gather the required information for each section of the form.
-
Fill in personal and organizational details as prompted.
-
Ensure accurate justification for access is provided in the designated fields.
-
Follow guidance for digital or wet signature requirements.
Pay particular attention to common errors, such as missing information or incorrect signatures, to streamline approvals.
Information and Documentation Needed to Accompany Your Submission
A successful Form 2875 submission often requires additional documentation. Necessary materials include:
-
Supporting documents validating your identity and role.
-
Evidence showcasing training in cybersecurity awareness.
Users should utilize a pre-filing checklist to verify that all required materials are bundled with the form before submitting.
Submission Methods and Where to Send Your Form 2875
Submitting the Form 2875 can be done through various methods. Here’s how different users can send in their requests:
-
Online submission through the designated portal.
-
Physical mailing to the appropriate DoD office.
It is crucial to note any associated processing times or fees that may apply depending on the submission method chosen.
What Happens After You Submit the Form 2875?
Once the Form 2875 has been submitted, users can expect to receive confirmation of receipt. Here’s what to anticipate next:
-
Tracking the status of your application can often be done via the submission portal.
-
Familiarizing oneself with common reasons for rejection, such as incomplete forms or invalid documentation.
Taking these steps can help navigate the process smoothly and avoid unnecessary delays.
Security and Compliance Considerations for the Form 2875
The completion and processing of the Form 2875 must adhere to stringent security measures. Key considerations include:
-
A commitment to protecting data in line with regulations such as HIPAA and GDPR.
-
Understanding record retention requirements for all submitted forms.
Utilizing secure platforms for handling sensitive documents enhances overall data security.
Experience the Ease of Using pdfFiller for Your Form 2875 Needs
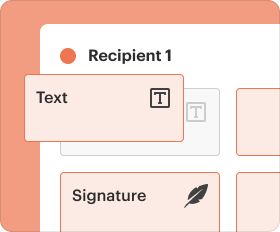
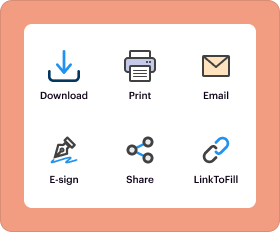
pdfFiller offers a streamlined solution for managing the Form 2875. Users can easily edit and fill out the form using the platform’s capabilities:
-
Edit text and images seamlessly.
-
Utilize cloud-based security for sensitive document management.
-
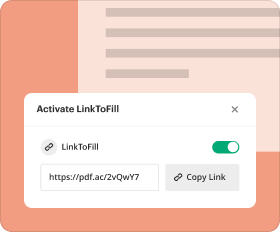
Easily eSign and share the completed form with necessary parties.
Engaging with pdfFiller simplifies the overall process of completing and submitting the Form 2875.
How to fill out the form 2875 system authorization
-
1.To access the Form 2875 on pdfFiller, visit the pdfFiller website and log in or create an account if you don’t have one.
-
2.Use the search bar to locate the Form 2875 System Authorization Access Request by entering its name or relevant keywords.
-
3.Click on the form to open it in pdfFiller's editing interface, where you can view all designated fields.
-
4.Before completing the form, gather necessary information such as your personal details, organizational information, and a justification for access.
-
5.Fill in the required fields starting with your name and other personal identifiers. Use the fillable fields to enter accurate data.
-
6.For checkboxes or fields that require options, click on the relevant box or dropdown to make your selections.
-
7.After filling out all information, review the document carefully to ensure all sections are completed and accurate.
-
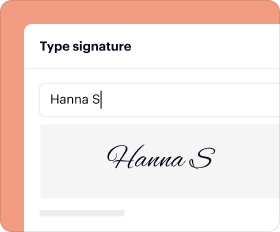
8.Ensure that all required signatures from the requestor, supervisor, security manager, system owner, and cybersecurity personnel are included.
-
9.Use the tools available in pdfFiller to sign the document electronically, following the prompts for digital signatures.
-
10.Once you have finalized the form, you can download it as a PDF file, save it within your pdfFiller account, or submit it directly through the platform if applicable.
Who is eligible to submit the Form 2875?
Anyone who needs access to Department of Defense systems is eligible to submit the Form 2875, including military personnel, contractors, and civil service employees.
What are the common mistakes to avoid when filling out Form 2875?
Common mistakes include missing required fields, failing to obtain all necessary signatures, and not providing valid justification for access. Always double-check all completed sections before submission.
How do I submit the completed Form 2875?
Once you've filled out the Form 2875, you can submit it directly through pdfFiller if your organization allows electronic submissions, or you can download it and email or hand it to the appropriate authority.
Is there a deadline for submitting the Form 2875?
The Form 2875 typically must be completed annually. However, specific deadlines may vary based on your organizational policies, so check with your supervisor for exact dates.
Are there any required supporting documents for Form 2875?
Generally, you may need to provide supporting documents to verify your identity and need for access, such as a government ID or proof of position within the DoD.
How long does it take to process the Form 2875?
Processing times for the Form 2875 may vary depending on your organization's procedures. It can take anywhere from a few days to several weeks, so plan accordingly.
What should I do if I encounter issues while filling out Form 2875 on pdfFiller?
If you encounter issues on pdfFiller, check their help section for troubleshooting tips, or contact their customer support for assistance with technical difficulties.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.