Last updated on Mar 3, 2015

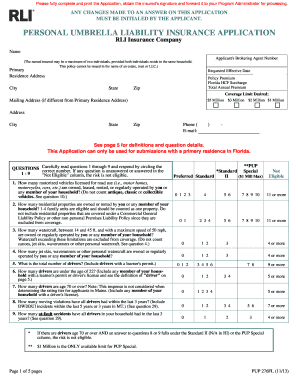
Get the free Application for Information Security and Privacy Liability Coverage
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is Security Privacy Liability Application
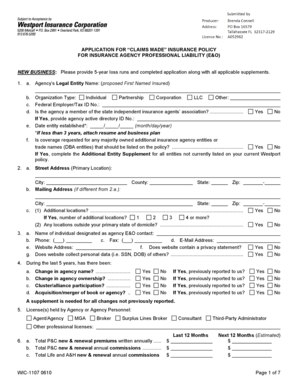
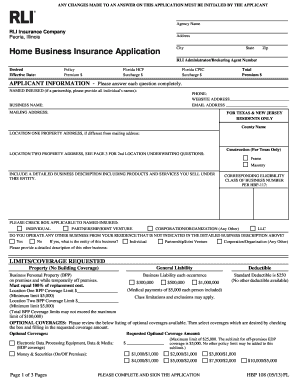
The Application for Information Security and Privacy Liability Coverage is a business form used by companies to apply for insurance against data breaches and privacy violations.
pdfFiller scores top ratings on review platforms




Who needs Security Privacy Liability Application?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to Security Privacy Liability Application
What is the Application for Information Security and Privacy Liability Coverage?
The Application for Information Security and Privacy Liability Coverage is essential for businesses seeking protection against data breaches and privacy violations. This document enables organizations to secure insurance that mitigates financial risks associated with these incidents.
It covers various aspects, including detailed information about the applicant's data security measures, prior claims history, and compliance with relevant regulations. Understanding its importance is vital for businesses to ensure they have adequate protection in place.
Compliance requirements are a crucial part of the application process, ensuring that organizations meet the necessary standards for data handling and privacy.
Purpose and Benefits of the Application for Information Security and Privacy Liability Coverage
Applying for information security and privacy liability coverage offers numerous advantages to businesses. By obtaining this form of protection, organizations can significantly reduce their financial exposure in case of data breaches.
This coverage not only aids in mitigating financial risks associated with potential incidents but also aligns with the importance of regulatory compliance for businesses operating in data-sensitive industries. Organizations that prioritize this application are better equipped to manage the consequences of privacy violations.
Who Needs the Application for Information Security and Privacy Liability Coverage?
The target audience for this application includes a wide range of businesses and organizations that manage sensitive data. Various sectors, such as healthcare, finance, and eCommerce, should consider applying due to their increased vulnerability to data breaches.
Assessing the risk profile of potential applicants is imperative. Businesses should evaluate their operations, data management practices, and the nature of the information they handle to determine their need for this coverage.
Eligibility Criteria for the Application
Understanding the eligibility criteria for applying for this coverage is essential. Factors such as business size, industry standards, and operational practices play a significant role in determining who can apply.
Organizations must consider any prerequisite conditions, including their data security measures and compliance history. A company’s past claims history may also influence the application process, impacting the approval and terms of coverage.
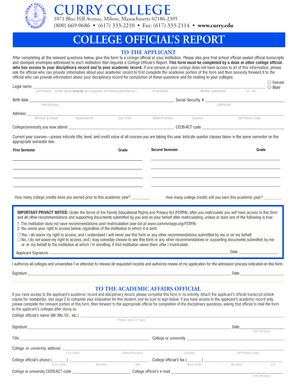
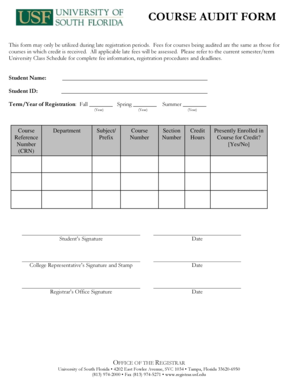
How to Fill Out the Application for Information Security and Privacy Liability Coverage Online (Step-by-Step)
Completing the application accurately is crucial for a successful submission. Follow these steps to ensure the information is correctly filled out:
-
Begin by reviewing the document to familiarize yourself with its sections.
-
Carefully fill in all blank fields, ensuring accurate details are provided.
-
Pay attention to checkboxes and answer all questions thoroughly.
-
Gather any necessary supporting information before you start the application.
By preparing in advance, you can streamline the process and reduce the chance of errors.
Common Errors and How to Avoid Them
During the application process, applicants often encounter common mistakes that can lead to delays or rejection. Here are several frequent pitfalls to watch for:
-
Omitting required information or leaving fields incomplete.
-
Providing inaccurate or outdated details that do not reflect the current situation.
To avoid these issues, double-check your entries and ensure compliance with the requirements. Utilizing a validation checklist prior to submission can help ensure accuracy.
Submission Methods and Delivery
Understanding the various submission methods available is essential for effective application delivery. You can submit the application online or via traditional mail, depending on your preference.
Once the application is submitted, it’s beneficial to know what to expect during the waiting period. Keeping track of your submission status can provide peace of mind as you await a response from the underwriter.
What Happens After You Submit the Application for Information Security and Privacy Liability Coverage
After submitting the application, the underwriting process begins. Underwriters will review the information provided, assessing the risk and determining eligibility for coverage.
Applicants should be aware that timelines for approval or rejection can vary. If further information is requested by the underwriter, timely communication and provision of the necessary details are crucial to expedite the process.
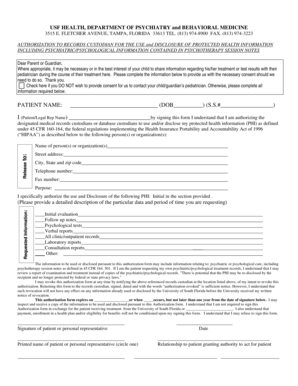
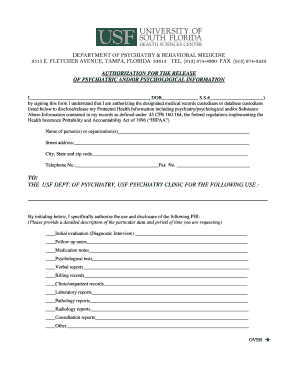
Security and Compliance in the Application Process
When submitting sensitive information through the application, it’s vital to consider the security measures in place. pdfFiller is committed to protecting user data through advanced encryption methods.
Compliance with standards such as HIPAA and GDPR ensures that the handling of sensitive information is conducted securely. Organizations must prioritize secure document management to maintain privacy and compliance during the application process.
Unlock the Benefits of Using pdfFiller for Your Application Process
Utilizing pdfFiller simplifies the application process for information security and privacy liability coverage. The platform’s user-friendly tools make filling out the application easier and more efficient.
With features like eSigning and secure sharing of completed forms, pdfFiller enhances the overall experience. Additionally, document management capabilities add value, making the organization of essential paperwork straightforward.
How to fill out the Security Privacy Liability Application
-
1.To begin, access pdfFiller and search for 'Application for Information Security and Privacy Liability Coverage'. Click to open the form.
-
2.Familiarize yourself with the layout of the form, noting sections dedicated to business information and questions regarding data security practices.
-
3.Before filling out the form, gather necessary information such as your company's operations details, data protection measures, prior claims made, and compliance with relevant regulations.
-
4.Start entering the required information in the designated fields. Use clear and precise language to describe your business and security practices.
-
5.Respond to each yes/no question by selecting the appropriate checkbox next to each statement.
-
6.Carefully review all sections to ensure that you have completed all questions and have provided any requested supplemental information.
-
7.Pay attention to the signature area, ensuring your name and title are printed clearly after signing the document.
-
8.Once you have completed the form, utilize pdfFiller's review function to verify your entries for accuracy.
-
9.Finalizing the form means checking for any missing information or errors. Make corrections as necessary.
-
10.Finally, save your completed form digitally, download it for your records, or submit it directly through pdfFiller to the appropriate insurance underwriter.

Who is eligible to use the Application for Information Security and Privacy Liability Coverage?
Any business that handles sensitive customer data or is involved in information processing may apply for this form. Ensure your operations align with insurance requirements.
What are the common mistakes to avoid while completing this application?
Avoid leaving any questions unanswered, especially those related to your data security measures, as this can delay processing. Ensure accuracy in all information provided.
How do I submit the completed application?
Once finalized, you can submit the application digitally through pdfFiller. Alternatively, you can download and email it directly to the insurance underwriter.
Are there any fees associated with processing this application?
Fees may vary based on the insurance provider. It is advisable to inquire about any processing or application fees directly with the underwriter before submission.
What supporting documents should I prepare?
You may need to include documents that demonstrate compliance with data protection regulations and any prior claims related to privacy violations or data breaches.
How long does it take to process the application?
Processing times vary; typically, it may take a few days to a few weeks. Ensure all information is accurate to avoid delays.
Is notarization required for this application?
No, notarization is not required for the Application for Information Security and Privacy Liability Coverage.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.