Last updated on Mar 7, 2015

Get the free Information Security Training Sign-Off Form
We are not affiliated with any brand or entity on this form
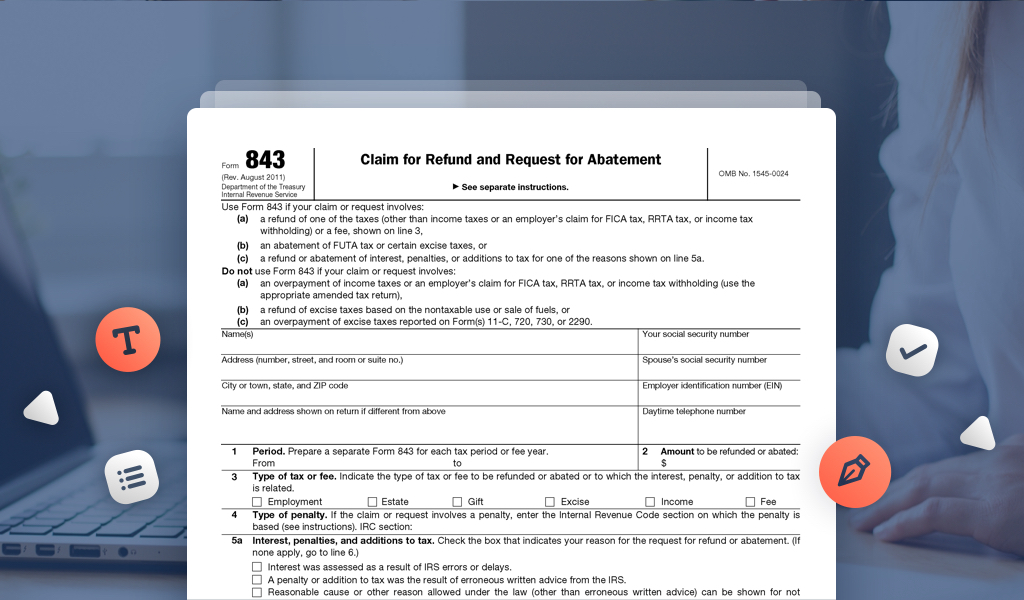
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is Security Training Sign-Off
The Information Security Training Sign-Off Form is an employee acknowledgment document used by The George Washington University to confirm that staff have completed necessary online security training.
pdfFiller scores top ratings on review platforms




Who needs Security Training Sign-Off?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to Security Training Sign-Off
What is the Information Security Training Sign-Off Form?
The Information Security Training Sign-Off Form is utilized by The George Washington University to confirm that employees have successfully completed mandatory security training. This form serves to validate participation in security training, ensuring that documentation is in place for compliance and awareness of security protocols.
Proper documentation is essential for maintaining compliance, particularly in educational institutions, as it highlights the importance of security awareness among employees.
Purpose and Benefits of the Information Security Training Sign-Off Form
This form is crucial for organizations as it guarantees that all employees are educated in information security protocols. By documenting completed training, it fosters accountability within the organization.
-
Ensures adherence to necessary security training for all employees.
-
Supports compliance with institutional policies and legal requirements.
Key Features of the Information Security Training Sign-Off Form
The Information Security Training Sign-Off Form includes several critical components designed for ease of use. Each form contains specified fields necessary for proper documentation.
-
Mandatory fields include signatures, titles, and dates for verification.
-
Instructions are provided for supervisors and management to facilitate the sign-off process.
Who Needs to Use the Information Security Training Sign-Off Form?
This form is primarily aimed at supervisors and management at The George Washington University. It is their responsibility to ensure that all staff members complete the required information security training.
-
Supervisors must oversee the training and compliance of their team members.
-
Management is responsible for validating and signing the form.
How to Fill Out the Information Security Training Sign-Off Form Online
Filling out the Information Security Training Sign-Off Form online can be accomplished using pdfFiller. Follow these step-by-step instructions to ensure accurate completion.
-
Access the Information Security Training Sign-Off Form through pdfFiller.
-
Fill out each section, ensuring that information is entered correctly.
-
Review the completed form for any missing or incorrect data.
Submission Methods for the Information Security Training Sign-Off Form
Upon completion, the form can be submitted using various methods to meet institutional requirements. Understanding these options is essential for timely processing.
-
Submitting electronically is often preferred for efficiency.
-
Paper submission options are available for individuals who prefer traditional methods.
Common Errors to Avoid When Completing the Information Security Training Sign-Off Form
When filling out the Information Security Training Sign-Off Form, being aware of common errors can aid in successful submission. Mistakes can delay the process and lead to non-compliance.
-
Inaccurate signatures can result in invalid documentation.
-
Failing to complete all required fields can lead to delays.
Security and Privacy Considerations for Handling the Information Security Training Sign-Off Form
It is vital to ensure security and compliance while handling the Information Security Training Sign-Off Form. Appropriate data protection measures should be followed to safeguard sensitive information.
-
Adhere to regulations such as HIPAA and GDPR.
-
Implement secure document handling practices when using pdfFiller.
Get Started with the Information Security Training Sign-Off Form using pdfFiller
Utilizing pdfFiller simplifies the process of completing the Information Security Training Sign-Off Form. The platform's features enhance usability and security while managing the form.
-
pdfFiller provides a user-friendly interface for efficient form completion.
-
The service includes robust security features, ensuring the safety of sensitive information.
How to fill out the Security Training Sign-Off
-
1.Access the Information Security Training Sign-Off Form on pdfFiller by searching for the form name in the search bar after logging in.
-
2.Once the form is open, navigate through the sections to locate the fields that require completion.
-
3.Before starting, gather necessary information including your name, signature, title, and the date of training completion.
-
4.Fill in your details in the designated fields, ensuring accuracy in your name, title, and date.
-
5.Supervisors and management must also enter their names, titles, and signatures where indicated on the form.
-
6.If any fields are not applicable or do not pertain to your situation, ensure you are following the instructions provided within the document.
-
7.Once you have completed all required fields, review the entire form to check for any errors or missing information.
-
8.Upon final review, save the form to your account or download it directly to your device.
-
9.Submit the completed form via the designated submission method instructed on the document, ensuring it reaches the appropriate recipient.

Who is required to complete the Information Security Training Sign-Off Form?
The form must be completed by all employees who have undergone the online security training at The George Washington University, along with their supervisors and management for verification.
Is there a deadline for submitting the Information Security Training Sign-Off Form?
It's essential to submit the form promptly after completing the training to ensure compliance and avoid any administrative issues. Check with your supervisor for specific deadlines.
How should I submit the Information Security Training Sign-Off Form once completed?
After filling out and reviewing the Information Security Training Sign-Off Form, you should submit it via the instructions outlined on the form, typically through your department's email or internal system.
What supporting documents are needed with the Information Security Training Sign-Off Form?
Generally, no additional supporting documents are required beyond the completed form itself. However, check if your department has specific documentation protocols.
What are some common mistakes to avoid while filling out the form?
Ensure that all fields are filled accurately, with no typos or missing signatures. Double-check adherence to any specific instructions provided in the form.
How long does it take for the Information Security Training Sign-Off Form to be processed?
Processing time can vary based on submission methods and departmental workload, but it is usually reviewed within a few business days. Follow up with your supervisor if there are delays.
Can I save the Information Security Training Sign-Off Form as a draft on pdfFiller?
Yes, pdfFiller allows you to save your progress. This is useful if you need to gather additional information before finalizing the form.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.